A Guide To Cybersecurity Deception Techniques
Cybersecurity deception techniques can strengthen your organization's defensive strategy -- if you're stealthy about it. Learn how to deploy honeypots.
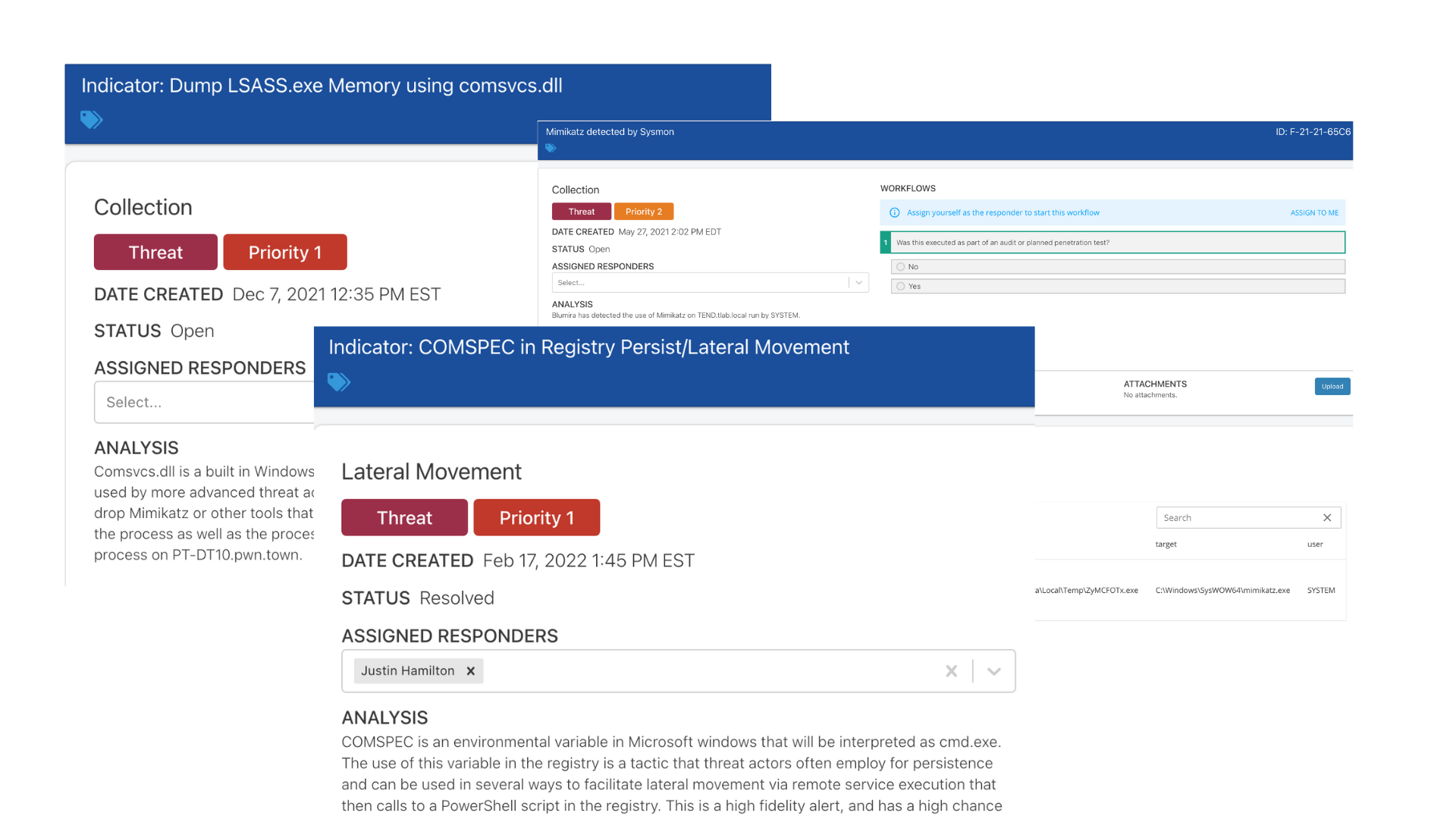
Read MoreBuilding Effective Incident Response Procedures
Multiple malware infections are serious and require a rigorous analytical approach. Developing a malware incident response plan is key.
Read MoreHow to Disrupt the Ransomware Kill Chain
Ransomware attacks often start with indicators that are easy to overlook. Learn how to identify and detect each stage in the ransomware kill chain.
Read MoreHow to Tell If You Have Ransomware 6 Warning Signs
It's important to catch ransomware before it does major damage. Here are 6 signs that indicate a ransomware attack.
Read MoreHow to Detect Web Shells With a SIEM
Web shells often fly under the radar, but these malicious scripts can wreak havoc. Learn how to detect web shells with a SIEM like Blumira's.
Read MoreLock Down PowerShell or Else!
How attackers leverage PowerShell bypass policies to gain access to your network and how Blumira enables you to detect, alert and respond to these attacks.
Read MoreDefending Against AD Kerberos Attacks
Defend against Active Directory Kerberos attacks with Blumira's advanced cybersecurity solutions. Protect your organization's critical assets today.
Read MoreDetecting SolarWinds & Ransomware Attacks With Process Monitoring
Shore up your security blindspots by monitoring and detecting obscure processes in your environment to stop modern attacks like ransomware and SolarWinds.
Read MoreDetect & Protect Against the SUNBURST Backdoor
Here's how to mitigate, detect indicators of compromise and protect against the latest SolarWinds supply chain attack and SUNBURST backdoor.
Read MoreSecurity Detections for a Hybrid Azure AD Join Environment
Enhance security in hybrid Azure AD environments with Blumira's threat detection. Identify and respond to threats efficiently for improved cloud security.
Read More