Blumira Security Honeypots
Detect unauthorized access and attack lateral movement across your environment with Blumira honeypot software, a type of deception technology.
Benefits of Honeypots
Once a threat actor accesses a system, the honeypot can track their behavior to uncover information about how they infiltrate systems and move laterally around the network.
Detect Attackers’ Lateral Movement
Honeypots are one of the most powerful internal detection mechanisms a network can have, even if they only detect something once in a blue moon. A fully configured honeypot will help detect and prevent cyberattacks from happening.
-
What is a Honeypot?
What is a Honeypot?
Honeypots are a clever security tool used to gain visibility into active threats or expose curious insiders who might introduce risk to your environment. A honeypot lures attackers with a network device that appears to contain valuable data. Once an attacker attempts to log in, scan the device, or access a file on the device, the honeypot will notify your team. -
Easily Set Up and Deploy a Honeypot
Easily Set Up a Honeypot
With Blumira, you can easily deploy virtual honeypots with the click of a button. By placing virtual honeypots at various locations around your environment – such as your workstation and server subnets – you can quickly determine if a threat is poking at hosts to find new avenues for access.
-
Automatically Block Threats
Automatically Block and Contain Threats
Once Blumira has detected a honeypot security event, the platform provides step-by-step response workflows. For example, in the case of an unauthorized access attempt, we provide you the option to block the source IP at the switch or firewall level. The playbook then walks you through next steps for further remediation.
What is a Honeypot?
Honeypots are a clever security tool used to gain visibility into active threats or expose curious insiders who might introduce risk to your environment. A honeypot lures attackers with a network device that appears to contain valuable data. Once an attacker attempts to log in, scan the device, or access a file on the device, the honeypot will notify your team.Easily Set Up a Honeypot
With Blumira, you can easily deploy virtual honeypots with the click of a button. By placing virtual honeypots at various locations around your environment – such as your workstation and server subnets – you can quickly determine if a threat is poking at hosts to find new avenues for access.
Automatically Block and Contain Threats
Once Blumira has detected a honeypot security event, the platform provides step-by-step response workflows. For example, in the case of an unauthorized access attempt, we provide you the option to block the source IP at the switch or firewall level. The playbook then walks you through next steps for further remediation.Our Metrics Speak for Themselves
Blumira Customers in Their Own Words
Hear what our clients are saying.
“The honeypots are a cool add-on to the SIEM and a good way to see if there’s lateral movement on our network. It’s not something we would do ourselves, but with Blumira, we were able to click one button and deploy it.”
Mike Morrow
Technical Infrastructure Manager, Ottawa County
“Blumira reduces the number of security staff required to monitor firewall, antivirus, shared drives, infrastructure configs, and overall change management. We're alerted to only the important/critical alerts and there are actually useful information guides to walk you through resolutions.”
Network Administrator
Education Mid-Market Customer
“We have a fair amount of security alerts coming from our security tools and we are a small team. Having Blumira sort through those alerts for us helps give us the ability to focus more on projects and less on alerts.”
Jeff B.
IT Leader, Mid-Market Company
Learn More About Honeypots
See More
Honeypots: Understanding Their Role in Cybersecurity
Read More
Detecting RDP Attacks With Honeypots: Blumira Data Insights
Read More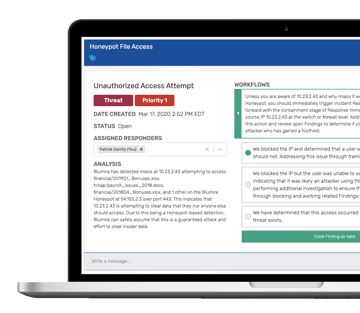
Hands in the Honeypot: Detecting Real Security Threats
Read MoreTry Honeypot, and XDR for Free
Experience Blumira XDR for free with automated detection and response for 3 cloud connectors.