- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Securing Operational Technology For Manufacturing
Manufacturing Security That Works With Your Reality
Transform cybersecurity from your biggest operational concern into a competitive advantage. Blumira empowers manufacturers to stop threats before they disrupt production, safeguard critical IP, streamline compliance processes, and strengthen supplier relationships—using the IT resources you already have.
What Manufacturing Operations Need Most
Cyber Attacks on the Manufacturing Industry

Cyber Attacks on the Manufacturing Industry
- Manufacturing was the most targeted industry in 2021, with 23% reporting ransomware attacks (IBM X-Force Threat Intelligence Index)
- Slowdowns and operational downtime pressure downstream supply chains into ransom payments
- Popular attack methods include phishing and vulnerability exploitation
- Sixty-one percent of incidents at OT-connected organizations last year were in the manufacturing industry
Ransomware Risks Halting Manufacturing
Ransomware Risks Halting Manufacturing
Manufacturing companies often rely on highly interconnected, automated, and complex systems to run machinery and computers for their operations. Any type of cybersecurity attack that spreads throughout their network can potentially bring operations to a halt and result in costly breaches and downtime.
Ransomware attacks not only disrupt and stop operations, they can also result in the leakage of intellectual property, as modern ransomware attacks often involve both extortion and the stealing of data.
Essential Security Infrastructure for Manufacturing Teams
Blumira provides the security foundation manufacturing IT departments need, integrating seamlessly with your existing tools and processes.
Expert-Guided Response
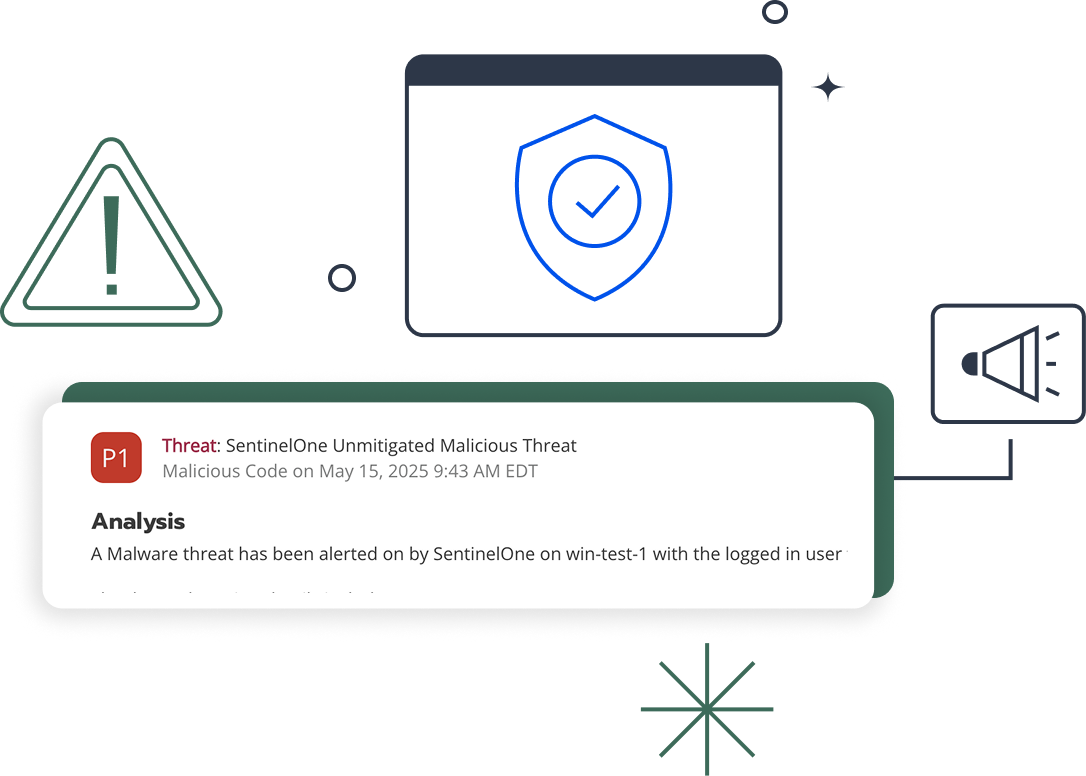
Blumira Cloud SIEM
Production-Smart Visibility
Blumira endpoint agent
Security Monitoring Core
Blumira automated threat response
Streamlined Security for Busy Teams
Atlantic Constructors, Inc. (ACI)
Challenge – The IT Director of Atlantic Constructors, Inc. (ACI) needed a simplified SIEM that his small IT team could use to keep their organization safe from ransomware and account takeovers.

Streamlined Security for Busy Teams
Atlantic Constructors, Inc. (ACI)
Challenge – The IT Director of Atlantic Constructors, Inc. (ACI) needed a simplified SIEM that his small IT team could use to keep their organization safe from ransomware and account takeovers.
Solution – ACI turned to Blumira cloud SIEM to help them detect previously unknown threats, following response playbooks written for IT teams to help them remediate threats quickly and easily.
"I don't have the staff dedicated to sit and read logs all day or with the skillset to analyze our data. We chose Blumira for its simplicity."
JIM PAOLICELLI — IT DIRECTOR
Read the full storyMeeting Manufacturing Compliance
-
CMMC
The Blumira modern security platform helps your organization easily meet and exceed CMMC framework requirements for logging, monitoring, threat detection, and response. We either support or complement a variety of CMMC controls from Levels 1 & 2, covering many domains.
-
NIST CSF
Blumira’s security platform helps organizations easily meet and support multiple NIST CSF core functions and outcomes, including threat detection, security continuous monitoring, adverse event analysis, incident response reporting and communication, incident analysis, and more.
-
ISO 27001
Complying with ISO 27001 verifies an organization has a system in place to handle risks related to the security of data owned or handled by the company. Blumira helps manufacturers and service providers protect against operational disruptions and business downtime, as well as supporting many ISO 27001 controls.
The Blumira modern security platform helps your organization easily meet and exceed CMMC framework requirements for logging, monitoring, threat detection, and response. We either support or complement a variety of CMMC controls from Levels 1 & 2, covering many domains.
Blumira’s security platform helps organizations easily meet and support multiple NIST CSF core functions and outcomes, including threat detection, security continuous monitoring, adverse event analysis, incident response reporting and communication, incident analysis, and more.
Complying with ISO 27001 verifies an organization has a system in place to handle risks related to the security of data owned or handled by the company. Blumira helps manufacturers and service providers protect against operational disruptions and business downtime, as well as supporting many ISO 27001 controls.
Frequently Asked Questions
Does a SIEM monitor industrial control systems and OT networks?
It depends on the SIEM. Blumira monitors the IT side of manufacturing environments: cloud platforms, identity providers, endpoints, firewalls, and business applications. It does not natively monitor OT protocols like Modbus, BACnet, or EtherNet/IP. For organizations that need visibility into programmable logic controllers (PLCs), SCADA systems, or industrial IoT devices, a dedicated OT monitoring tool like Claroty, Dragos, or Nozomi Networks is the right choice. Blumira protects the IT infrastructure that connects to and controls the OT environment, which is where most manufacturing cyberattacks originate.
What NIST frameworks apply to manufacturing cybersecurity?
NIST SP 800-171 is required for manufacturers in the Department of Defense supply chain, and CMMC 2.0 is the certification framework that enforces it. NIST CSF (Cybersecurity Framework) is widely adopted voluntarily across all manufacturing sectors. Both frameworks require continuous monitoring, audit logging, and incident response capabilities. Blumira maps its detections and compliance reporting to NIST 800-171, CMMC 2.0, and NIST CSF controls, and provides 1 year of searchable log retention to satisfy audit requirements.
How do manufacturers with small IT teams manage a SIEM?
Most manufacturers run IT teams of 2 to 5 people responsible for everything from help desk to production floor networking. Blumira is built for exactly this situation. Detection rules are written and maintained by Blumira's 24/7 SecOps team, so your IT staff does not need security engineering expertise. Alerts come with guided response playbooks, and automated response actions can contain threats without waiting for human intervention. The platform deploys in a single afternoon and connects to existing infrastructure through pre-built integrations. Manufacturers without dedicated security staff can also deploy Blumira through a managed service provider (MSP).
What cybersecurity threats target manufacturing companies?
Manufacturing was the most targeted industry for cyberattacks in 2023 for the third consecutive year, according to IBM X-Force's 2024 Threat Intelligence Index. Attackers target manufacturers because production downtime creates immediate financial pressure to pay ransoms. Common attack vectors include phishing emails, compromised remote access tools (especially VPNs and RDP), and supply chain software vulnerabilities. Blumira detects the precursors to these attacks, including credential theft, lateral movement across networks, privilege escalation, and data staging for exfiltration, and automated response actions can contain the threat before it reaches production systems.
How does a SIEM help with supply chain security requirements?
Large manufacturers and defense contractors increasingly require their suppliers to demonstrate cybersecurity controls as a condition of doing business. CMMC 2.0 formalizes this for the DOD supply chain, but private-sector primes like Boeing, Lockheed Martin, and automotive OEMs have similar expectations. A SIEM provides the continuous monitoring, audit logging, and incident detection that supply chain assessors look for. Blumira's compliance reporting maps to NIST 800-171 and CMMC controls, and 1 year of searchable log retention provides the audit trail that assessors require.
Can Blumira monitor both office IT and production floor networks?
Blumira monitors the IT systems present in both environments: firewalls, switches, Windows servers, endpoints, cloud platforms, and identity providers. If your production floor uses standard IT networking equipment that forwards syslog or integrates via API, Blumira can ingest those logs. However, Blumira does not decode or inspect OT-specific protocols used by industrial control systems. The recommended approach for converged OT/IT environments is to pair Blumira for IT-layer detection with an OT-specific monitoring tool for protocol-level ICS visibility.
When is Blumira not the right fit for a manufacturing company?
Blumira is not the right fit if your primary need is native OT protocol monitoring, deep packet inspection of industrial control system traffic, or asset inventory of PLCs and SCADA controllers. Those requirements call for a dedicated OT security platform. Blumira is also less customizable than enterprise SIEMs like Splunk, so manufacturers with large security teams that want to write custom correlation rules and build bespoke dashboards may prefer a platform that offers in-platform query languages. For manufacturers with small IT teams focused on meeting compliance requirements and stopping ransomware before it hits production, Blumira is purpose-built.
Essential Manufacturing Security Resources
View All
Compliance Security Frameworks and Insurance
5 min read
| March 3, 2026
OnDemand - Your CMMC Certification Playbook (and Pitfalls To Avoid)
Read More
Compliance Security Frameworks and Insurance
9 min read
| January 14, 2026
The New CMMC Compliance Rule: What It Means for Defense Contractors and How Blumira Makes Compliance Achievable
Read More
Compliance Security Frameworks and Insurance
10 min read
| November 10, 2025
What is NIST 800-171? A Non-Technical Guide
Read MoreExperience Blumira Today
Tired of fragmented security tools and alert fatigue? Blumira centralizes your security operations, offering deep insights and actionable intelligence to identify and remediate threats before they cause damage. Discover the power of proactive defense.
