- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Faster Network Intrusion Detection
Blumira Security Honeypots
Detect unauthorized access and attack lateral movement across your environment with Blumira honeypot software, a type of deception technology.
Benefits of Honeypots
Once a threat actor accesses a system, the honeypot can track their behavior to uncover information about how they infiltrate systems and move laterally around the network.
They produce high-fidelity alerts
They make life harder for cybercriminals
Detect Attackers’ Lateral Movement
Honeypots are one of the most powerful internal detection mechanisms a network can have, even if they only detect something once in a blue moon. A fully configured honeypot will help detect and prevent cyberattacks from happening.
-
What is a Honeypot?
What is a Honeypot?
Honeypots are a clever security tool used to gain visibility into active threats or expose curious insiders who might introduce risk to your environment. A honeypot lures attackers with a network device that appears to contain valuable data. Once an attacker attempts to log in, scan the device, or access a file on the device, the honeypot will notify your team. -
Easily Set Up and Deploy a Honeypot
Easily Set Up a Honeypot
With Blumira, you can easily deploy virtual honeypots with the click of a button. By placing virtual honeypots at various locations around your environment – such as your workstation and server subnets – you can quickly determine if a threat is poking at hosts to find new avenues for access.
-
Automatically Block Threats
Automatically Block and Contain Threats
Once Blumira has detected a honeypot security event, the platform provides step-by-step response workflows. For example, in the case of an unauthorized access attempt, we provide you the option to block the source IP at the switch or firewall level. The playbook then walks you through next steps for further remediation.
What is a Honeypot?
Honeypots are a clever security tool used to gain visibility into active threats or expose curious insiders who might introduce risk to your environment. A honeypot lures attackers with a network device that appears to contain valuable data. Once an attacker attempts to log in, scan the device, or access a file on the device, the honeypot will notify your team.Easily Set Up a Honeypot
With Blumira, you can easily deploy virtual honeypots with the click of a button. By placing virtual honeypots at various locations around your environment – such as your workstation and server subnets – you can quickly determine if a threat is poking at hosts to find new avenues for access.
Automatically Block and Contain Threats
Once Blumira has detected a honeypot security event, the platform provides step-by-step response workflows. For example, in the case of an unauthorized access attempt, we provide you the option to block the source IP at the switch or firewall level. The playbook then walks you through next steps for further remediation.Our Metrics Speak for Themselves
15
min/day
on average to manage Blumira and respond to threats
99.4
%
faster average detection time vs industry average
24
/7
automated monitoring
99.7
%
CSAT rating for our support teams
Blumira Customers in Their Own Words
Hear what our clients are saying.
“The honeypots are a cool add-on to the SIEM and a good way to see if there’s lateral movement on our network. It’s not something we would do ourselves, but with Blumira, we were able to click one button and deploy it.”
Mike Morrow
Technical Infrastructure Manager, Ottawa County
“Blumira reduces the number of security staff required to monitor firewall, antivirus, shared drives, infrastructure configs, and overall change management. We're alerted to only the important/critical alerts and there are actually useful information guides to walk you through resolutions.”
Network Administrator
Education Mid-Market Customer
Frequently Asked Questions
What is a honeypot in cybersecurity?
A honeypot is a decoy system or resource deployed on your network that has no legitimate business purpose. It exists solely to attract and detect unauthorized activity. Because no real user or application should ever interact with a honeypot, any connection to it is suspicious by definition. Honeypots are one of the highest-signal, lowest-noise detection methods available. They do not require complex rule tuning or behavioral baselines because the logic is simple: if something touches the honeypot, investigate it.
How does Blumira's honeypot detection work?
Blumira deploys honeypot sensors within your network that mimic real services. When any device, user, or process interacts with the honeypot, Blumira generates an alert. Because these sensors have no legitimate traffic, the detection has very high fidelity. The alert feeds into the same detection and response workflow as all other Blumira findings: automated response capabilities can contain the threat, and guided playbooks provide remediation steps. The 24/7 SecOps team is available for direct support on any honeypot-triggered incident.
Do honeypots generate a lot of false positives?
No. Honeypots are among the lowest false-positive detection methods in security. The reason is straightforward: a honeypot has no real purpose on the network, so any interaction with it is inherently suspicious. There is no legitimate traffic to separate from malicious traffic. Misconfigured network scanners or IT tools that accidentally discover the honeypot can generate occasional alerts, but these are easily identified and worth investigating anyway since they reveal uncontrolled scanning in your environment.
What types of threats do honeypots catch?
Honeypots are particularly effective at detecting lateral movement, which is when an attacker (or malware) has already gained initial access and is scanning the network for additional targets. This is one of the hardest attack phases to detect with traditional tools because the traffic can look similar to normal network activity. Honeypots also detect internal reconnaissance, unauthorized network scanning, insider threats, and compromised devices probing for accessible services. They catch threats that perimeter-focused tools miss entirely.
How do you deploy Blumira honeypots?
Blumira honeypots are deployed as lightweight sensors on your network. The deployment process is guided by the Blumira team and typically involves placing sensors on network segments where you want visibility into lateral movement or unauthorized access. Effective placement means putting honeypots where an attacker scanning the network would encounter them: alongside real servers, in sensitive subnets, or near high-value assets. The 24/7 SecOps team helps determine optimal placement based on your network topology.
When are honeypots not enough on their own?
Honeypots only detect threats that interact with them. An attacker who knows exactly which systems to target and never scans the network may never trigger a honeypot. They are also blind to cloud-based attacks, email compromise, identity-based attacks, and any activity that does not involve network-level reconnaissance. Honeypots work best as one detection layer within a broader security stack. In Blumira's platform, honeypot detections are combined with cloud log analysis, endpoint telemetry, and identity monitoring to cover the full attack surface, not just the network layer.
Learn More About Honeypots
Blumira security blog
Security Trends and Info
13 min read
| March 11, 2020
Honeypots: Understanding Their Role in Cybersecurity
Read More
Security Alerts
10 min read
| May 26, 2020
Detecting RDP Attacks With Honeypots: Blumira Data Insights
Read More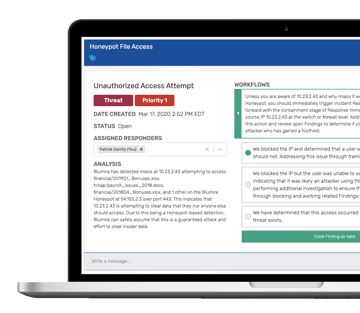
Security How-To
4 min read
| April 20, 2020
Hands in the Honeypot: Detecting Real Security Threats
Read More