- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Blumira Healthcare Cybersecurity
Healthcare organizations have a heightened need to get their security and compliance right. Blumira offers an all-in-one solution that healthcare companies of all sizes and security experience levels can leverage. Blumira enables you to detect and respond to threats so you can prevent ransomware attacks and data breaches.
Addressing the Healthcare Security Gap with Blumira Security Operations
With Blumira cloud-based advanced threat detection and response platform for healthcare organizations, your team will get the support it needs to secure your patient data.
Traditional SIEMs require months of setup that resource-strapped IT teams in healthcare don’t have. Blumira does all of the heavy lifting for you. We parse your data, write and roll out new rules automatically, and provide pre-written playbooks for response.
Try Blumira to detect and respond to threats free for 30 days. It’s fast, and easy for IT and security teams in the healthcare industry to use.
Get StartedSecurity Challenges for Healthcare Organizations
Healthcare organizations have to manage multiple pressures on their security posture to avoid crippling consequences.
-
Regulatory Requirements
Regulatory requirements
Healthcare has greater liability and regulatory requirements than almost any other industry. HIPAA alone includes 154 separate requirements with defined audit procedures - monitoring them all is an enormous task. Any breach can result in hefty government fines and an erosion of customer trust. In fact, healthcare is the target of 25% of data breaches, costing an average of $408 per lost or stolen record (Ponemon/IBM).
-
Legacy Infrastructure
Legacy infrastructure
Due to growth through mergers and acquisitions, many healthcare organizations struggle with an influx of devices that are out of date or don’t work with their infrastructure. This makes it difficult to maintain uniformity in the environment and deploy an additional agent to detect and prevent cyber attacks. -
Resource-Draining SOCs
Resource-draining SOCs
Many institutions use traditional Security Information and Event Management (SIEM) products that only detect cyber attacks, meaning incoming events need to be addressed in real-time before any data is lost. This often requires the build-out of a 24/7 Security Operations Center (SOC) with a team of IT security analysts to sift through alerts, determine their severity, take action on the most important ones, and perform ongoing maintenance–skills and resources that not all healthcare IT teams have available to them. -
Common Healthcare Attacks
Common security issues seen in healthcare attacks
Blumira data shows that healthcare organizations are especially vulnerable to these types of attacks:
- Password spraying – A type of brute-force attack that’s used by attackers to gain initial access into a local hospital’s system.
- RDP connections – Remote Desktop Protocol is often misconfigured to allow public IP access from the internet, which can result in ransomware. Blumira notifies users of any external attempts to connect via RDP to your network to protect against attacker exploitation.
- Lateral movement – Attackers will target hospital network devices for unauthorized access to enable them to move laterally through your environment. Blumira honeypots give you an easy, one-click way to detect and respond to these attempts.
Regulatory requirements
Healthcare has greater liability and regulatory requirements than almost any other industry. HIPAA alone includes 154 separate requirements with defined audit procedures - monitoring them all is an enormous task. Any breach can result in hefty government fines and an erosion of customer trust. In fact, healthcare is the target of 25% of data breaches, costing an average of $408 per lost or stolen record (Ponemon/IBM).
Legacy infrastructure
Due to growth through mergers and acquisitions, many healthcare organizations struggle with an influx of devices that are out of date or don’t work with their infrastructure. This makes it difficult to maintain uniformity in the environment and deploy an additional agent to detect and prevent cyber attacks.Resource-draining SOCs
Many institutions use traditional Security Information and Event Management (SIEM) products that only detect cyber attacks, meaning incoming events need to be addressed in real-time before any data is lost. This often requires the build-out of a 24/7 Security Operations Center (SOC) with a team of IT security analysts to sift through alerts, determine their severity, take action on the most important ones, and perform ongoing maintenance–skills and resources that not all healthcare IT teams have available to them.Common security issues seen in healthcare attacks
Blumira data shows that healthcare organizations are especially vulnerable to these types of attacks:
- Password spraying – A type of brute-force attack that’s used by attackers to gain initial access into a local hospital’s system.
- RDP connections – Remote Desktop Protocol is often misconfigured to allow public IP access from the internet, which can result in ransomware. Blumira notifies users of any external attempts to connect via RDP to your network to protect against attacker exploitation.
- Lateral movement – Attackers will target hospital network devices for unauthorized access to enable them to move laterally through your environment. Blumira honeypots give you an easy, one-click way to detect and respond to these attempts.
How Healthcare Organizations Detect Cyber Attacks With Blumira
Blumira offers an all-in-one solution that helps healthcare organizations detect and respond to threats and prevent a ransomware attacks and data breaches
Detection
Monitor and detect real threats
Response
Enable your team to quickly respond
Expertise
Gain access to security expertise
Frequently Asked Questions
How does a SIEM protect patient health information (PHI)?
A SIEM collects and correlates security logs from every system that stores or transmits PHI, including EHR platforms, identity providers, cloud infrastructure, and endpoints. Blumira's pre-built detections flag unauthorized access attempts, abnormal login patterns, privilege escalations, and data exfiltration indicators across these systems. When a threat is detected, automated response actions can contain it without waiting for human intervention, and guided playbooks walk your team through remediation. Blumira's 24/7 SecOps team maintains detection rules so coverage evolves as healthcare-targeted threats change.
How long should healthcare organizations retain audit logs for HIPAA?
HIPAA requires that documentation of policies and procedures be retained for six years under 45 CFR 164.530(j). While the Security Rule does not specify an exact audit log retention period, most compliance advisors recommend retaining audit logs for at least six years to align with the documentation requirement and satisfy OCR investigators during breach inquiries. Blumira provides 1 year of searchable log retention. Healthcare organizations with longer retention needs should plan for archival storage beyond the searchable window.
What HIPAA controls does Blumira satisfy?
Blumira directly supports several HIPAA Security Rule technical safeguards: audit controls (45 CFR 164.312(b)), information system activity review (45 CFR 164.308(a)(1)(ii)(D)), and log-in monitoring (45 CFR 164.308(a)(5)(ii)(C)). The platform automatically collects logs, detects unauthorized access to systems containing ePHI, and generates audit-ready compliance reports. Blumira's 24/7 SecOps team and automated response capabilities also support the Security Rule's requirement for security incident procedures (45 CFR 164.308(a)(6)).
Can Blumira monitor EHR systems like Epic or Cerner?
Blumira integrates with the infrastructure surrounding EHR systems rather than directly with EHR application logs. This includes the cloud platforms hosting EHR workloads (AWS, Azure), the identity providers controlling access (Microsoft Entra ID, Okta), the endpoints used to access patient records, and the network firewalls protecting the environment. For organizations that can forward EHR-specific logs via syslog or API, Blumira's team can work with you to build custom detection rules around those data sources as a partnership.
How does ransomware target hospitals and clinics specifically?
Healthcare organizations face persistent ransomware threats. The HHS 405(d) task force and multiple industry reports consistently rank healthcare among the most targeted sectors for ransomware, driven by the value of patient data and the operational pressure to restore systems quickly. Attackers know that hospitals face life-safety pressure to restore systems quickly, which increases the likelihood of paying ransoms. Common entry points include phishing emails to clinical staff, compromised Remote Desktop Protocol (RDP) connections, and exploitation of unpatched VPN appliances. Blumira detects ransomware precursors like lateral movement, credential abuse, and mass file encryption patterns, and automated response actions can contain the threat before it spreads across the network.
Can a small clinic or practice afford SIEM for HIPAA compliance?
Yes. Blumira uses flat-rate pricing per employee with unlimited data ingestion, which makes the cost predictable for small practices. A 25-person clinic pays the same per-employee rate as a 500-bed hospital. The platform deploys in a single afternoon, ships with pre-built HIPAA-relevant detections, and is backed by a 24/7 SecOps team, so you do not need to hire a security analyst. Clinics without dedicated IT staff can deploy Blumira through a managed service provider (MSP) who handles ongoing monitoring on their behalf.
What healthcare-specific compliance reporting does Blumira provide?
Blumira generates compliance reports that map directly to HIPAA Security Rule requirements, including audit controls, access monitoring, and incident detection. These reports show auditors which controls are in place, what log sources are being monitored, and how threats were detected and responded to. Reports can be exported on demand for OCR investigations, risk assessments, or annual HIPAA security reviews. The platform also provides 1 year of searchable log retention for forensic review during breach investigations.
When is Blumira not the right fit for a healthcare organization?
Blumira is not a good fit for large health systems that need a fully customizable SIEM with in-platform query languages, custom correlation rules, and dedicated security engineering teams to operate it. If your organization has a 10+ person SOC and needs to write custom detection logic in SPL or KQL, an enterprise platform like Splunk or Microsoft Sentinel will give you more flexibility. Blumira also does not provide medical device network monitoring or biomedical equipment inventory. It monitors the IT infrastructure protecting those devices, not the devices themselves.
Additional Healthcare Cybersecurity Resources
View More
Compliance Security Frameworks and Insurance
6 min read
| April 9, 2026
2026 HIPAA Security Rule Updates: Critical Changes for IT Teams
Read More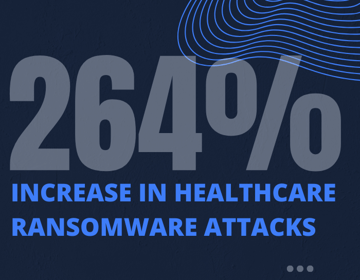
Compliance Security Frameworks and Insurance
5 min read
| May 14, 2025
Reducing Risks to Protect Patient Data & Meet HIPAA Compliance
Read More
Security Trends and Info
4 min read
| April 22, 2024
Ransomware in Healthcare: After-the-Fact is Too Late
Read MoreExperience Blumira Today
Tired of fragmented security tools and alert fatigue? Blumira centralizes your security operations, offering deep insights and actionable intelligence to identify and remediate threats before they cause damage. Discover the power of proactive defense.
