- Product
Product Overview
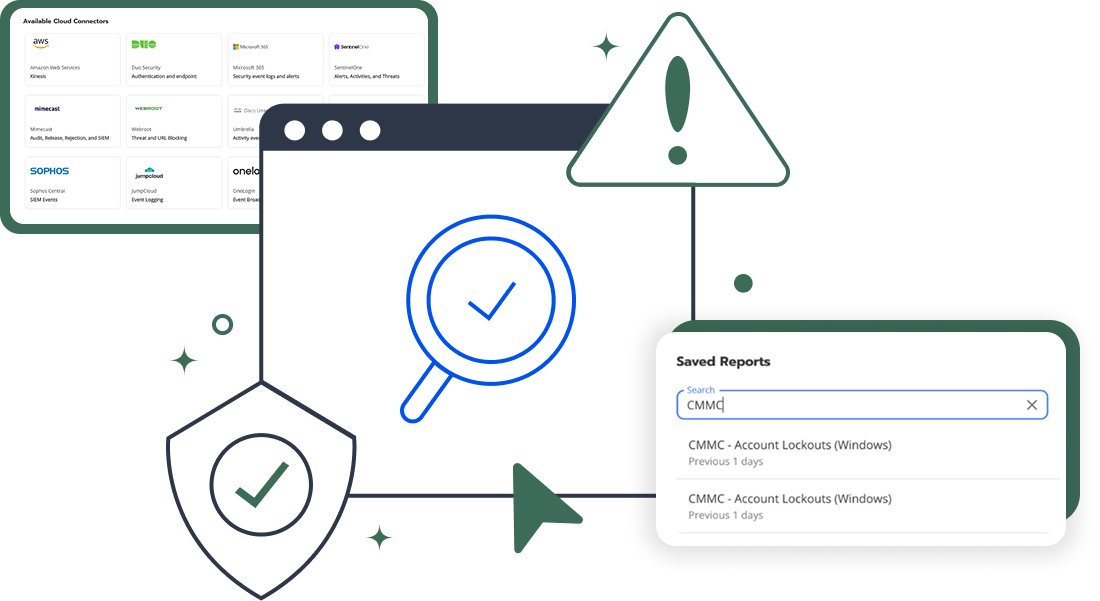
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Cybersecurity for Retail
Cybersecurity is an ongoing concern for retail organizations. The retail sector is also highly regulated by compliance frameworks such as PCI-DSS. In 2021, cyberattacks on retail and e-commerce organizations surged by 264%, according to a SonicWall report. One in every five ransomware attacks targeted a retail company.

Limited Resources Leave Retail Organizations At Risk
While many retail organizations turn to traditional Security Information and Event Management (SIEM) platforms to detect cybersecurity threats, most organizations have limited resources to engineer the product to work effectively.
Traditional SIEMs require regular optimization to defend against the latest cyberattacks. In large corporations, a 24/7 Security Operations Center (SOC) staffed by a group of specialized IT security analysts sift through alerts, determine the severity of each, take action on the most important ones, and feed and maintain the system on an ongoing basis.
Common Security Risks and Challenges for Retail Companies
Take a look at some of the most common risks and hurdles for the retail sector.
Value of Consumer Data
E-Commerce Exposure
New Technology
Credit card skimming attacks
PoS malware
Supply chain attacks
Cybersecurity Best Practices for Retail Companies
There are some best practices that IT teams in retail can follow, even with limited budgets and staff.
-
Prioritize end user training
Prioritize End User Training
IT and security teams should know about ransomware warning signs, but so should end users. Failure to train and educate users often points to a broader issue — a lack of security. That, combined with the fact that human error is the starting point for many cyberattacks, means that organizations should make training more of a priority.
At a minimum, IT and security teams should inform staff about how to spot a phishing email. More formal security awareness training is even better, but an informal chat about what a phishing email can look like and what to do is a good first step.
-
Deploy Sysmon
Deploy Sysmon
When it comes to preventing ransomware, it’s important to have visibility into an environment. Endpoint detection and response (EDR) tools can achieve that, but they can also be prohibitively expensive for retail establishments with limited budgets. System Monitor (Sysmon for short) is a free Microsoft utility that small IT teams can use to get visibility into their environments. Sysmon is part of the Sysinternals software package and provides a higher level of event monitoring than the standard Windows logs. It records events such as network connections, process creations, file hashes, and changes to the Windows Registry.
IT leaders without the budget for an EDR solution should deploy Sysmon for enhanced logging that can provide a wealth of data about endpoints. Since Sysmon is free, it does require more care and feeding than a plug-and-play paid tool. IT admins need to deploy updates as they are released and make configuration changes as necessary, but those tasks generally fall under the umbrella of standard patch management. It’s relatively easy to install and configure Sysmon in a few steps.
-
Implement Threat Detection and Response
Implement Threat Detection and Response
Using Sysmon and a centralized log management tool will provide some visibility into an environment and help with alerting, but small IT and security teams need to know how to respond to those alerts. A threat detection and response solution alerts IT and security teams on suspicious behavior that is indicative of a ransomware attack.
Prioritize End User Training
IT and security teams should know about ransomware warning signs, but so should end users. Failure to train and educate users often points to a broader issue — a lack of security. That, combined with the fact that human error is the starting point for many cyberattacks, means that organizations should make training more of a priority.
At a minimum, IT and security teams should inform staff about how to spot a phishing email. More formal security awareness training is even better, but an informal chat about what a phishing email can look like and what to do is a good first step.
Deploy Sysmon
When it comes to preventing ransomware, it’s important to have visibility into an environment. Endpoint detection and response (EDR) tools can achieve that, but they can also be prohibitively expensive for retail establishments with limited budgets. System Monitor (Sysmon for short) is a free Microsoft utility that small IT teams can use to get visibility into their environments. Sysmon is part of the Sysinternals software package and provides a higher level of event monitoring than the standard Windows logs. It records events such as network connections, process creations, file hashes, and changes to the Windows Registry.
IT leaders without the budget for an EDR solution should deploy Sysmon for enhanced logging that can provide a wealth of data about endpoints. Since Sysmon is free, it does require more care and feeding than a plug-and-play paid tool. IT admins need to deploy updates as they are released and make configuration changes as necessary, but those tasks generally fall under the umbrella of standard patch management. It’s relatively easy to install and configure Sysmon in a few steps.
Implement Threat Detection and Response
Using Sysmon and a centralized log management tool will provide some visibility into an environment and help with alerting, but small IT and security teams need to know how to respond to those alerts. A threat detection and response solution alerts IT and security teams on suspicious behavior that is indicative of a ransomware attack.
Blumira Addresses the Retail Cybersecurity Gap
Blumira is a PCI-compliant SIEM with threat detection and response that alerts your team about critical cyber threats in real-time and provides automated and actionable response capabilities that reduce the overhead associated with traditional SIEM products.
With Blumira SIEM, you can detect and respond to threats for 3 cloud integrations. It’s fast and easy for IT and security teams in the retail industry to use.
Frequently Asked Questions
Does a retailer need a SIEM for PCI DSS compliance?
PCI DSS 4.0 Requirement 10 mandates that organizations log and monitor all access to cardholder data environments. Requirement 10.4 specifically requires audit logs to be reviewed at least daily, and Requirement 10.7 requires that failures of critical security systems be detected and responded to promptly. A SIEM is the most practical way to meet these requirements because it automates log collection, correlation, and alerting. Blumira's pre-built detections cover PCI-relevant scenarios, and the 24/7 SecOps team maintains detection rules as PCI DSS requirements evolve.
How does Blumira help protect point-of-sale systems?
Blumira monitors the IT infrastructure surrounding point-of-sale (POS) environments: the firewalls protecting POS network segments, the identity providers controlling employee access, the endpoints in back-office systems, and the cloud platforms processing transactions. The platform detects credential theft, unauthorized network access, lateral movement toward POS segments, and data exfiltration patterns. Automated response actions can contain threats without waiting for human intervention, which is critical for retail environments that operate outside standard business hours.
What cybersecurity threats target retail companies?
Retail faces a concentrated set of threats: payment card skimming (both physical and digital via Magecart-style attacks), phishing campaigns targeting store managers and corporate employees, ransomware timed to peak shopping seasons, and credential stuffing attacks against e-commerce accounts. The Verizon 2024 Data Breach Investigations Report found that web application attacks and system intrusion were the top patterns in retail breaches. Blumira detects the IT-layer indicators of all of these attack types, including anomalous login patterns, privilege escalation, and lateral movement.
Can Blumira handle seasonal traffic spikes without extra cost?
Yes. Blumira uses flat-rate pricing per employee with unlimited data ingestion, so your cost stays the same whether your systems generate 1 GB or 100 GB of logs per day. This matters for retailers with seasonal peaks (holiday shopping, back-to-school, promotional events) that dramatically increase transaction volumes and log output. Per-GB SIEMs can double or triple in cost during peak seasons, which creates a perverse incentive to reduce logging when you need the most visibility.
How does a SIEM work for multi-location retail chains?
Blumira is multi-tenant by default, which means it can ingest and correlate logs from multiple store locations, distribution centers, and corporate offices into a single view. Each location's firewalls, endpoints, and cloud systems send logs to Blumira through pre-built integrations. Your team gets a centralized view of threats across all locations without deploying on-premises hardware at each site. Alerts include location context so your team knows exactly which store or facility is affected.
How long does PCI DSS require audit log retention?
PCI DSS 4.0 Requirement 10.7 requires that audit log history be retained for at least 12 months, with at least the most recent three months immediately available for analysis. Blumira provides 1 year of searchable log retention, which satisfies both the 12-month retention and the immediate availability requirements without additional storage configuration. This eliminates the need for separate archival solutions that many retailers cobble together to meet PCI audit expectations.
When is Blumira not the right fit for a retail organization?
Blumira is not the right fit for large enterprise retailers that need a fully customizable SIEM with in-platform query languages, custom correlation engines, and dedicated security engineering staff to operate. Retailers with 50+ person security teams and complex data warehouse architectures may need the flexibility of Splunk, Microsoft Sentinel, or Chronicle. Blumira also does not provide application-level monitoring for custom e-commerce platforms. If you need APM (application performance monitoring) or WAF (web application firewall) capabilities, those are separate tools that complement a SIEM rather than replace one. Retailers without dedicated security staff can deploy Blumira through a managed service provider (MSP) who handles monitoring on their behalf.
Additional Cybersecurity Resources
View AllExperience Blumira Today
Tired of fragmented security tools and alert fatigue? Blumira centralizes your security operations, offering deep insights and actionable intelligence to identify and remediate threats before they cause damage. Discover the power of proactive defense.



