- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
How Blumira Helps With
HIPAA Compliance Monitoring Solutions
Blumira’s cloud security solutions help healthcare organizations like yours easily meet and exceed HIPAA security compliance standards and HIPAA security controls.
HIPAA (Health Insurance Portability and Accountability Act of 1996) is a federal law that protects the confidentiality of sensitive patient health information.
While extremely important, HIPAA compliance can also be difficult to maintain as protocols evolve and organizational workflows change. With automated HIPAA compliance solutions from Blumira, you can be confident that your organization stays compliant while also remaining scalable, adaptable, and agile.
Why Blumira?
Healthcare organizations trust our HIPAA compliance tools for these reasons:
- End-to-End HIPAA Compliance Monitoring: Detect, prevent, and respond to security threats in real time.
- Automated Compliance Reports: Create HIPAA compliance reports for auditors and internal teams.
- Advanced Threat Detection: Blumira’s automated HIPAA cyber security capabilities help you identify threats before they become breaches.
- Seamless Integration: Blumira’s cloud security solutions for HIPAA compliance integrated with your existing cloud security stack and compliance solutions.
HIPAA and Cybersecurity: How Blumira HIPAA Compliance Tools Help
The following guidelines illustrate how Blumira HIPAA compliance software helps address the needs of HIPAA Phase 2:
-
Section 164.308(a)(1)(ii)(D)
Section 164.308(a)(1)(ii)(D)
Information system activity review (required). Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.
-
Section 164.308(a)(5)(ii)(C)
Section 164.308(a)(5)(ii)(C)
Log-in monitoring (addressable). Procedures for monitoring log-in attempts and reporting discrepancies.
-
Section 164.312(b)
Section 164.312(b)
Audit controls. Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.
-
Section 164.316(b)(2)(i)
Section 164.316(b)(2)(i)
Retain the documentation required by paragraph (b)(1) of this section for 6 years from the date of its creation or the date when it last was in effect, whichever is later.
-
References
Section 164.308(a)(1)(ii)(D)
Information system activity review (required). Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.
Section 164.308(a)(5)(ii)(C)
Log-in monitoring (addressable). Procedures for monitoring log-in attempts and reporting discrepancies.
Section 164.312(b)
Audit controls. Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.
Section 164.316(b)(2)(i)
Retain the documentation required by paragraph (b)(1) of this section for 6 years from the date of its creation or the date when it last was in effect, whichever is later.
Frequently Asked Questions
What HIPAA requirements does a SIEM satisfy?
A SIEM helps satisfy several HIPAA Security Rule requirements, including audit controls (45 CFR 164.312(b)), information system activity review (45 CFR 164.308(a)(1)(ii)(D)), and log-in monitoring (45 CFR 164.308(a)(5)(ii)(C)). Blumira's cloud SIEM automatically collects, correlates, and retains audit logs from systems that store or transmit ePHI, giving covered entities and business associates the monitoring and evidence trail that HIPAA auditors expect.
Do you need a SIEM for HIPAA compliance?
HIPAA does not explicitly require a SIEM by name, but the Security Rule does require audit controls, activity monitoring, and log retention. In practice, a SIEM is the most effective way to meet these requirements because it centralizes log collection, detects unauthorized access to ePHI, and generates the audit evidence that OCR investigators request during breach investigations. Without a SIEM, most organizations struggle to demonstrate continuous monitoring.
How long do HIPAA audit logs need to be retained?
HIPAA requires that documentation of policies and procedures be retained for six years (45 CFR 164.530(j)), but the Security Rule does not specify an exact retention period for audit logs. Industry best practice is to retain audit logs for at least one year, with many compliance consultants recommending six years to align with the documentation retention requirement. Blumira includes one year of log retention by default on all plans, with extended retention available.
What is the HIPAA Security Rule?
The HIPAA Security Rule (45 CFR Part 164, Subparts A and C) establishes national standards for protecting electronic protected health information (ePHI). It requires covered entities and business associates to implement administrative, physical, and technical safeguards. The technical safeguards include access controls, audit controls, integrity controls, and transmission security. A cloud SIEM like Blumira directly supports the audit controls and information system activity review standards by collecting and analyzing security logs across your environment.
Does Blumira help with HIPAA breach notification?
Yes. Blumira detects threats in real time and provides automated alerts with response playbooks, which helps organizations identify potential breaches quickly. Under HIPAA's Breach Notification Rule (45 CFR 164.400-414), covered entities must notify affected individuals within 60 days of discovering a breach. Blumira's detection and logging capabilities help organizations determine the scope of an incident faster, document what happened for OCR reporting, and demonstrate that they had reasonable safeguards in place.
How does Blumira handle PHI and ePHI logging?
Blumira ingests logs from systems that store or process ePHI, including cloud platforms, identity providers, endpoints, firewalls, and healthcare applications. The platform monitors for unauthorized access attempts, privilege escalations, and anomalous behavior across these systems. Blumira does not store the ePHI itself. Instead, it collects the security event logs and metadata that show who accessed what, when, and from where. All log data is encrypted in transit and at rest.
What HIPAA controls does Blumira automate?
Blumira automates several HIPAA technical safeguards, including continuous audit log collection (45 CFR 164.312(b)), automated threat detection and alerting for information system activity review (45 CFR 164.308(a)(1)(ii)(D)), and real-time monitoring for log-in attempts and access anomalies (45 CFR 164.308(a)(5)(ii)(C)). The platform deploys in hours (not months), takes about 15 minutes a day to manage, and connects to 75+ integrations, so IT teams at healthcare organizations can meet these controls without hiring dedicated security analysts.
Additional Healthcare Security Resources
View more
Compliance Security Frameworks and Insurance
6 min read
| April 9, 2026
2026 HIPAA Security Rule Updates: Critical Changes for IT Teams
Read More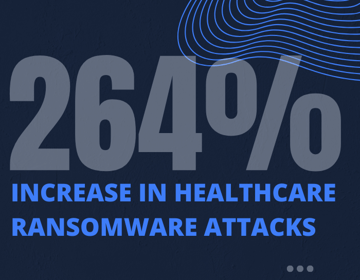
Compliance Security Frameworks and Insurance
5 min read
| May 14, 2025
Reducing Risks to Protect Patient Data & Meet HIPAA Compliance
Read More
Security Trends and Info
4 min read
| April 22, 2024
Ransomware in Healthcare: After-the-Fact is Too Late
Read MoreExperience Blumira Today
Tired of fragmented security tools and alert fatigue? Blumira centralizes your security operations, offering deep insights and actionable intelligence to identify and remediate threats before they cause damage. Discover the power of proactive defense.