The Blumira Mission
Security and reliability are the backbone of Blumira’s service. We are dedicated to providing excellence in customer experience and protecting your organization.
The Blumira Difference
Our core values

The People, Processes, and Technologies To Succeed
-
Leaders in Defensive Security
Blumira is co-founded by leaders in defensive and managed security, CSO Steve Fuller and CEO/CTO Matt Warner. Matt's user-centric approach to solving problems for customers is unique in an industry that is long known for overly complex, legacy solutions that often fail to protect organizations. He has over a decade of experience in IT and development, focusing on business strategy, development, compliance, threat detection and penetration testing.
-
Giving Back to the Security Community
The security and incident detection team at Blumira writes detection rules that power the Blumira platform to help identify indicators of compromise early and often for our customers. They are also dedicated to contributing to the greater security community by developing open-source Microsoft tools (known as Flowmira and Logmira) to make threat detection and response easier for all organizations.
-
Deep Security Roots
Sr. Incident Detection Engineer Amanda Berlin is a highly accomplished network defender, author of “Defensive Security Handbook: Best Practices for Securing Infrastructure” with Lee Brotherston, published by O’Reilly Media.
The Blumira operations, marketing, sales, and engineering teams are composed of several experienced security professionals who previously held positions at Duo Security and Censys. -
Data Security and Integrity
By protecting log data both in transit and at rest, Blumira ensures attackers can’t gain access to your log archives to read data without the appropriate keys. Least privilege practices makes the Blumira log database accessible only to internal Blumira services and parties that require access. For data integrity, Blumira validates that incoming logs haven’t been tampered with through periodic review and internal processes, and provides alerts for file-integrity monitoring (FIM) technology whenever changes are detected.
-
Automatic Updates
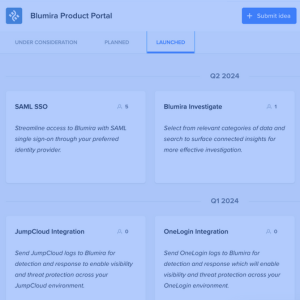
Blumira platform updates are cloud-delivered, sending them automatically to your organization to reduce any lag or downtime. This ensures that you’re detecting and alerting on the most important issues, around the clock. The Blumira engineering team develops and maintains parsers for a wide variety of technical integrations on an ongoing basis to save your team the time and resources of standardizing log data collection.
-
Our Detection Methodology
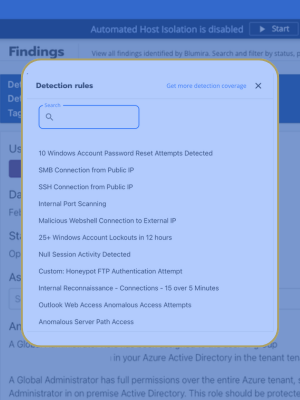
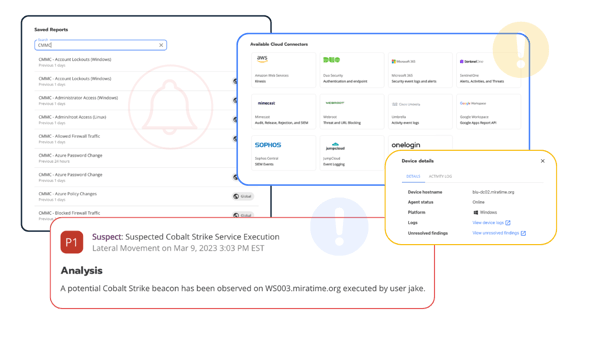
The Blumira threat detection framework focuses on intrusion behaviors given the ubiquity of Living-Off-the-Land tactics, while also aligning with the MITRE ATT&CK Framework. Loud and/or inaccurate security products can easily lead to alert fatigue, resulting in customers that ultimately ignore their own security tools. With that in mind, the Blumira security team designs, tests, and curates threat detections to be high fidelity from the moment of deployment. All customers receive both a contextual analysis and explicit workflow steps to first qualify and then mitigate all detected threats.
-
High-Availability Platform
Blumira leverages Google Cloud and Google Compute Platform (GCP) to provide a highly available security platform for our customers. Blumira maintains 99.99% uptime to ensure our service is always available and reliable.
Blumira is co-founded by leaders in defensive and managed security, CSO Steve Fuller and CEO/CTO Matt Warner. Matt's user-centric approach to solving problems for customers is unique in an industry that is long known for overly complex, legacy solutions that often fail to protect organizations. He has over a decade of experience in IT and development, focusing on business strategy, development, compliance, threat detection and penetration testing.
The security and incident detection team at Blumira writes detection rules that power the Blumira platform to help identify indicators of compromise early and often for our customers. They are also dedicated to contributing to the greater security community by developing open-source Microsoft tools (known as Flowmira and Logmira) to make threat detection and response easier for all organizations.
Sr. Incident Detection Engineer Amanda Berlin is a highly accomplished network defender, author of “Defensive Security Handbook: Best Practices for Securing Infrastructure” with Lee Brotherston, published by O’Reilly Media.
The Blumira operations, marketing, sales, and engineering teams are composed of several experienced security professionals who previously held positions at Duo Security and Censys.
By protecting log data both in transit and at rest, Blumira ensures attackers can’t gain access to your log archives to read data without the appropriate keys. Least privilege practices makes the Blumira log database accessible only to internal Blumira services and parties that require access. For data integrity, Blumira validates that incoming logs haven’t been tampered with through periodic review and internal processes, and provides alerts for file-integrity monitoring (FIM) technology whenever changes are detected.
Blumira platform updates are cloud-delivered, sending them automatically to your organization to reduce any lag or downtime. This ensures that you’re detecting and alerting on the most important issues, around the clock. The Blumira engineering team develops and maintains parsers for a wide variety of technical integrations on an ongoing basis to save your team the time and resources of standardizing log data collection.
The Blumira threat detection framework focuses on intrusion behaviors given the ubiquity of Living-Off-the-Land tactics, while also aligning with the MITRE ATT&CK Framework. Loud and/or inaccurate security products can easily lead to alert fatigue, resulting in customers that ultimately ignore their own security tools. With that in mind, the Blumira security team designs, tests, and curates threat detections to be high fidelity from the moment of deployment. All customers receive both a contextual analysis and explicit workflow steps to first qualify and then mitigate all detected threats.
Blumira leverages Google Cloud and Google Compute Platform (GCP) to provide a highly available security platform for our customers. Blumira maintains 99.99% uptime to ensure our service is always available and reliable.
Compliance for Every Industry
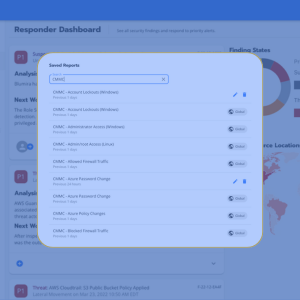
Blumira endeavors to meet many different compliance standards for logging, auditing, reporting, threat detection and more, including CMMC, NIST 800-171, NIST 800-53, PCI DSS, HIPAA and FFIEC compliance regulations for data security, confidentiality and integrity.
Learn more about compliance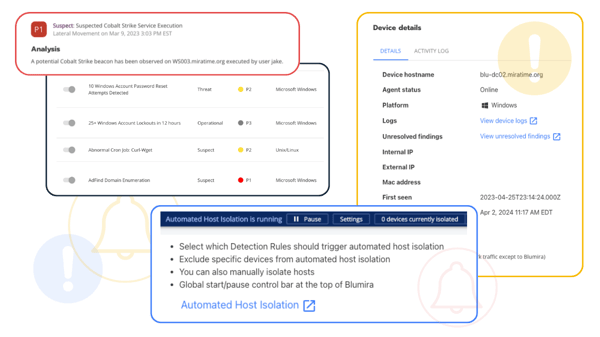
SOC 2 Compliant
Blumira undergoes a rigorous independent annual audit conducted by Insight Assurance to complete a SOC 2 (Service Organization and Availability Control) examination that ensures Blumira’s security protocols and use of data meet strict data security requirements established by the American Institute of CPAs (AICPA).
View Our Trust PortalGet Started For Free
Experience the Blumira Free SIEM, with automated detection and response plus compliance reports for 3 cloud connectors.