Microsoft Security
Detect threats 5X faster with Blumira’s advanced threat detection and response.
Microsoft Security Challenges
Small to mid-sized businesses and their MSPs are dealing with multiple security challenges.
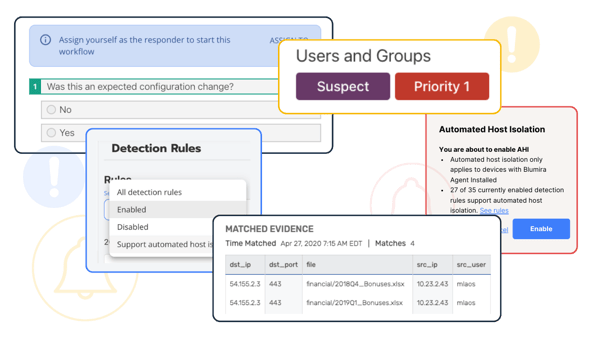
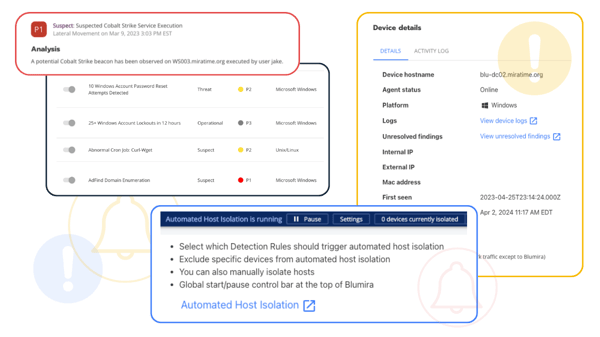
Identify & Respond to Threats
Start identifying and responding to threats in your Microsoft environment immediately – integrate Blumira’s cloud SIEM with your Microsoft stack in a matter of hours. Our M365 Threat Response allows you to take action directly within Blumira to disable potentially compromised users, saving you time and expediting remediation.
Setup is fast and easy for M365 using Cloud Connectors, no additional infrastructure or sensor required.
Microsoft Integrations for Blumira:
SIEM For Microsoft Security
Explore what SIEM for Microsoft Security looks like.
-
Windows Logging & Security
How to Enable Sysmon
To increase visibility into your environment, we recommend using System Monitor (Sysmon), an add-on for Windows logging. With Sysmon, you can detect malicious activity by tracking code behavior and network traffic. You can also create detections based on the malicious activity.
-
Preconfigured Windows Policies
Logmira for Advanced Windows Logging
To address limited default logging capabilities in Windows, Blumira offers Logmira, a pre-built set of group policy configurations. Free for everyone to use, this download shares our security team’s recommendations for increasing Windows log visibility for threat detection. It can also help you meet compliance auditing requirements.
-
NXLog Configurations
Flowmira for Windows Endpoint Security
To generate data from Windows endpoints and to get greater visibility into host actions, Blumira offers Flowmira, a set of customized NXlog configurations. We recommend using NXlog for Windows log collection to help identify security risks and policy breaches, or to analyze operational problems in server, operating system, and application logs.
How to Enable Sysmon
To increase visibility into your environment, we recommend using System Monitor (Sysmon), an add-on for Windows logging. With Sysmon, you can detect malicious activity by tracking code behavior and network traffic. You can also create detections based on the malicious activity.
Logmira for Advanced Windows Logging
To address limited default logging capabilities in Windows, Blumira offers Logmira, a pre-built set of group policy configurations. Free for everyone to use, this download shares our security team’s recommendations for increasing Windows log visibility for threat detection. It can also help you meet compliance auditing requirements.
Flowmira for Windows Endpoint Security
To generate data from Windows endpoints and to get greater visibility into host actions, Blumira offers Flowmira, a set of customized NXlog configurations. We recommend using NXlog for Windows log collection to help identify security risks and policy breaches, or to analyze operational problems in server, operating system, and application logs.
Free Guides & Tests
The Blumira security team has created best practice guides that walk you through Microsoft configurations. These guides can help your organization reduce your attack surface and security risk. They use free add-ons or tools already available in your existing Microsoft environment.
Not all traditional SIEMs or detection solutions are able to consistently identify Windows threats. We’ve developed detection tests you can use to identify security gaps in your tool capabilities to help you better understand your risk profile.
Microsoft Best Security Practice Guides:
Microsoft Security Detection Tests:
Helping IT Teams Protect Their Microsoft Environment
Hear what our customers are saying.
“I researched a number of SIEM providers online and found most were way out-of-the-ballpark expensive, required a lot of infrastructure and didn’t provide a great return on our investment.”
Fritz Ludemann
Information Systems Administrator The City of Crescent City
“For a certain size of customer with no staff or only one security staff member, Blumira is an absolute godsend.”
Jason Waits
CISO, Inductive Automotive
“Blumira added a new detection for malicious PowerShell activity. It flagged some activity in our environment. Blumira’s SecOps team immediately jumped on, saw that the scripts were legitimate activity coming from the Microsoft System Center monitoring agents, notified us that the alert was a false positive and that they had updated the detection rules for us.”
Matt Varblow
VP of Engineering Services, AdvantageCS
Additional Microsoft Security Resources
View more
Customer Story: LEAP Managed IT Streamlines Ticketing and Boosts Visibility with Blumira’s API
Read More
Customer Story: NetCenter Technologies
Read More
Customer Story: United Way of Pierce County
Read MoreGet Started for Free
Experience the Blumira Free SIEM, with automated detection and response and compliance reports for 3 cloud connectors.