Posts by Matthew Warner
The Iranian Cyber Threat: Key Insights for IT Teams
Although there is currently a ceasefire in place, geopolitical tensions between the United States and Iran continue to escalate. As a result, we're witnessing a corresponding...
Read MoreAbout the Author
Matthew Warner is Chief Technology Officer (CTO) and co-founder of Blumira. Matt brings nearly two decades of IT and cybersecurity experience to his leadership position, and a genuine passion for cybersecurity education. Prior to founding Blumira, he was Director of Security Services at NetWorks Group, a managed security services provider (MSSP) with a focus on compliance and ethical hacking. While at NetWorks Group, Matthew’s team searched for a SIEM that would serve their small to midsize business (SMB) clients well, but found that most products on the market were overly complex, expensive, and difficult to maintain. The concept of Blumira formed when Matthew noticed this significant gap in the market, and he developed a threat detection and response platform that was easy for SMBs to use. After the technology’s internal success at NetWorks Group, Matthew founded Blumira to focus his efforts on growing the platform to scale. Matthew is passionate about helping SMBs, which are often most vulnerable to cyberattacks, improve their security maturity with thoughtful and intentional changes. Through educational opportunities such as webinars, articles, podcasts, conference sessions and more, Matthew shares actionable advice that the most under-resourced and time-strapped teams can undertake. Threat research is another passion of Matthew’s. In late 2021, he led research efforts at Blumira that resulted in the discovery of an additional attack vector in the Log4j vulnerability, offering proactive solutions to help affected entities recover and protect themselves quickly. He works closely with the IT community to determine their pain points and challenges, and develops a product strategy that addresses their specific needs. In 2022, the Globee Cybersecurity Global Excellence Awards program recognized Matthew as CTO of the Year for his leadership and innovative problem-solving, as well as his credible research on Log4j vulnerabilities and notable contributions to Blumira’s 2022 State of Threat Detection and Response Report. Matthew’s dedication to Blumira is as long-lasting as the hedgehog tattoo etched on his leg.

What Iran-Based Activity Can Teach Us About Everyday Security Resilience
Read MoreMidwest Cybersecurity Innovation: The Rise of Silicon Heartland
Read MoreHow Manufacturers Can Secure Themselves Against Cyber Threats
Read MoreSupply Chain Vulnerabilities: Addressing Cybersecurity Risks in Manufacturing Networks
Read More
The Blumira Guarantee of Security, Reliability, and Availability
Read More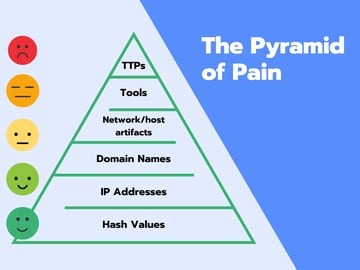
Inescapable: Why Detecting Behaviors Beats Zero-Days
Read More
Complete Guide to the NIST Cybersecurity Framework
Read More
Zero-Day Vulnerabilities Found in Microsoft Exchange (CVE-2022-41040 and CVE-2022-41082)
Read More
Why Blumira Launched a Free SIEM
Read More
Let’s All Calm Down About Spring4Shell
Read More
Patch for Sophos Firewall: (CVE-2022-1040)
Read More
Lapsus$ Claims To Breach Okta Customer Data
Read More
Top 7 Cloud Security Best Practices For 2022
Read More
5 Reasons Why We ❤️ Sysmon
Read More
Critical Bugs in Apache HTTPD Server: DoS & RCE
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
