Blumira Blog

Blumira and Cybersecurity Tech Trends
Read More
Lessons Learned from 3 Cyberattacks in Financial Services
Read More
Security Detection Update - 2024-3-19
Read More
Now Available: CIS Control Compliance Reports
Read More
The Hedgehog Defense #2: Defend Against Automatically Mounted Disk Images
Read More
“Entra”sting Roles You’ll Want to Know About
Read More
Boosting Microsoft 365 Security: A Blumira Success Story
Read More
Security Detection Update - 2024-3-12
Read More
On-Demand: Cost-Effective Strategies for Cybersecurity Compliance
Read More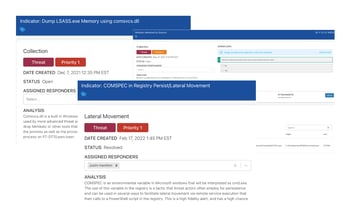
February 2024 Releases
Read More
On-Demand: Navigating PCI Compliance: Expert Insights for Small to Mid-sized Enterprises
Read More
4 Myths of XDR – The Truth about Detection and Response
Read More
Quick Cybersecurity Wins for the Public Sector
Read More
Blumira Awarded 2024 TMCnet Remote Work Pioneer Award
Read More
The 5 Most Annoying Things About Buying Cybersecurity Tools
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.