Blumira Blog

20-Minute Live Demo: Blumira XDR
Read More
Monitor Remote Employees Ethically and Effectively
Read More
QueueJumper: (CVE-2023-21554) Enables Remote MSMQ Exec
Read More
5 XDR Features Small Businesses Should Prioritize
Read More
XDR: Better Security Outcomes
Read More
G2 Recognizes Blumira in Spring 2023 Reports
Read More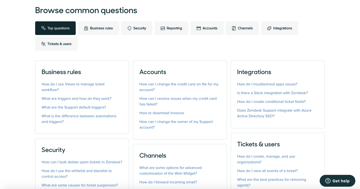
Top Help Desk Tools 2023: Choose the Best for Your Needs
Read More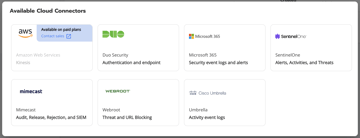
Free SIEM: Now With More Cloud Integrations!
Read More
Assessing Your Firewall Needs for Enhanced Security
Read More
Unleash Your Inner Cyber Hero: Must-See Talks at RSAC 2023
Read More
The Culture of Connection: the Art of Thriving at RSA Conference 2023
Read More
Blumira By The Numbers in 2022
Read More
Top 10 XDR Definitions | Blumira: Extended Detect & Response
Read More
How Endpoint Isolation Locks Down Cyber Attacks
Read More
Top 5 Steps For SMB Endpoint Security Success
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.