Security Trends and Info
Blumira Detections: Reduce Noise & Improve Your Time to Respond
Blumira’s detections help you save time, address risk, and reduce noise to help you protect your organization and increase operational resiliency.
Read More
5 Steps to Minimize Impact After Vendor Security Incidents
Read More
Turn Up Your Network Defenses to Eleven. Turn Down the Noise Pollution
Read More
SocGholish Coming Into Focus for Blumira
Read More
Blumira Briefings: Disclosure Drama, Ransomware Breakdown, and MFA Bypass Techniques
Read More
Introducing Blumira Briefings: Your Weekly Security News Download! 🔔
Read More
XSS: What It Means, How It Works, and How to Prevent It
Read More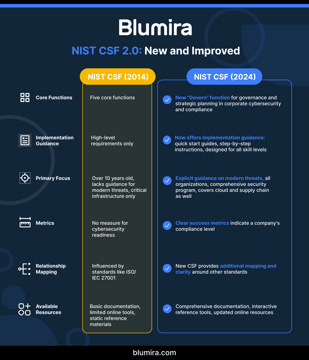
NIST Cybersecurity Framework Implementation for Mid-Market Companies: 2025 Update
Read MoreUnraveling Cybersecurity: From Virus Hunters to Intelligent Defenders
Read More
From Blind Spots to Insights: IT Security IT Visibility
Read MoreWhat’s your Security Brand? Building Trust Through Your Security Posture
Read MoreMidwest Cybersecurity Innovation: The Rise of Silicon Heartland
Read MoreThe Michigan Advantage: How Cybersecurity Innovation is Reshaping the Industry
Read MoreHuman-Centric Security: Five Strategies For A Collaborative Approach
Read More
Safeguard Your Phone Number with Supermoney's Guide
Read MoreFear, Uncertainty, and Helplessness in Cybersecurity
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
