This is the first in a series of five articles that can help your business adopt NIST CSF for cybersecurity planning.
A small business has hard choices to make. More always needs to be done to deal with cyber threats, but priorities lean toward serving customers and keeping products on the shelf. You’ve got some threat protections in place, but there’s this nagging feeling that you might be missing something. Finding out the hard way—after a damaging incident—cannot be an option. You’re a cybersecurity believer. Now it’s time to put together a more comprehensive plan.
It may surprise you that a government agency has a cybersecurity planning tool that’s been embraced by businesses large and small across a broad range of industries. And of course it’s got an acronym. It’s called the NIST CSF—the National Institute of Standards and Technology Cybersecurity Framework. What makes the NIST framework popular is the fact that it was developed in coordination with cybersecurity experts from around the world. While it was created in 2013 by a presidential order aimed at protecting critical infrastructure, NIST is voluntary and it’s highly adaptable. Version 1.1 has been widely adopted, and version 2.2 will be rolled out this year.
The core of NIST CSF
The NIST Cybersecurity Framework can be used by small businesses to plan and implement their risk management processes. It’s organized around three components: The framework core, profiles, and implementation tiers. The core consists of five pillars that can be used as a planning guide and checklist. The pillars are broken into categories and sub-categories. NIST also provides extensive free resources to support each item on the checklist.
The NIST framework is a comprehensive tool that aims to address cybersecurity from every angle. Small businesses and their IT partners are using the core pillars to identify risks and prioritize next steps. The Blumira SIEM is playing an important part in many aspects of implementation:
Identify. One place to start with NIST CSF is by mapping out areas of potential risk. Six categories are covered under the Identify pillar: Asset management, business environment, governance, risk assessment, risk management, and supply chain risk. Each category is broken down into sub-categories. For example, governance covers policies, procedures, and processes to manage and monitor the organization’s regulatory, legal, risk, environmental, and operational requirements.
Protect. Most businesses have a level of safeguards in place to secure data, systems, and assets. Some measures may be built into their infrastructure, and some may be required by regulatory agencies. The NIST framework outlines six categories of controls for reducing attack surfaces and hardening defenses: Identity management, authentication, and access control, awareness and training, data security, information protection processes and procedures, maintenance, and protective technology. As your organization works through the framework, you’ll likely discover areas that require additional attention.
Detect. The major focus of cybersecurity in the past has been on protection and response. Now that tools like Blumira SIEM are available for small and medium-sized businesses, greater emphasis is being put on detection. This means more timely discovery of cybersecurity threats—and the potential to shut them down before greater harm is inflicted. Categories in the Detect pillar include anomalies and events, continuous security monitoring, and detection processes.
Respond. A cyberattack response plan isn’t something you create after an incident happens. NIST recommends documenting and updating processes and procedures so the entire team understands their roles in the event of an incident. Response categories include communication, analysis, mitigation, and implementing improvements based on lessons learned. Blumira SIEM includes built-in response and mitigation playbooks that automate many of the best practices in this pillar.
Recover. Recovery focuses on restoring business capabilities impaired by a cybersecurity incident. Again, this is not a plan to be created after the fact. Rapid recovery is vital to restoring systems to normal operations so your company can continue its mission. This pillar includes recovery planning, making improvements based on lessons learned, and communications with internal and external stakeholders.
The current NIST CSF includes 23 categories under those five pillars, and it’s broken down further into more than 100 sub-categories. It can seem daunting, but a major reason the framework has been so widely embraced is that it’s meant as a guide and not a hard-and-fast set of rules. The profile portion of the framework helps businesses map their path to more effective risk management.
A profile of where you want to be
Cybersecurity planning is always going to involve making choices. The NIST framework recommends creating profiles in order to identify gaps between your current level of risk management and a realistic picture of where you want to be. First, assemble a current profile for the business by assessing progress with the five core pillars. Next, create a target profile that outlines where you need to be to achieve risk management goals and support overall business objectives.
A comparison of the two profiles—current and target—will help you prioritize next steps so you can assign the right resources. The NIST framework recognizes that risk management is an ongoing process and should be informed by careful cost/benefit analysis. As each business is different, each cybersecurity plan will be unique, and it should continue to evolve.
To help businesses identify their level of cybersecurity risk management, the NIST framework also includes four Implementation tiers: partial, risk informed, repeatable, and adaptive. A company can identify their tier by assessing their current risk management practices, threat environment, legal and regulatory requirements, information sharing practices, business/mission objectives, supply chain cybersecurity requirements, and organizational constraints. This helps to shape the conversation around the benefits and drawbacks of striving for a higher-level tier versus maximizing the current position.
How Blumira supports the NIST framework
Implementing NIST CSF requires robust logging, monitoring, and incident response—capabilities small businesses have had a hard time acquiring until recently. This is where a security information and event management (SIEM) platform like Blumira comes in. Blumira capabilities that align with the NIST framework include:
Asset discovery. Blumira’s automated, contextualized mapping of IT infrastructure, cloud environments, and data flows supports the identify function.
Log collection. Centralized gathering of log data from multi-source IT environments enables auditing and accountability. Blumira’s log analysis shines a light on risks and suspicious activities that may otherwise go unseen with siloed security tools.
Security monitoring. Blumira’s behavior analysis and threat detection leverages machine learning to support continuous monitoring as outlined in the NIST framework, enabling faster threat identification.
Incident response. Blumira helps businesses implement NIST incident response objectives with customizable playbooks. Playbooks accelerate investigation and containment when incidents occur, limiting the impact of a breach.
Rapid recovery. Protections driven by real-time, contextual security intelligence boost your ability to adapt and recover from disruptions.
Compliance reporting. Blumira automates report production, making it easy to validate security control implementation for compliance purposes.
Blumira experts work closely with customers to optimize their solution so it supports cybersecurity goals. The NIST framework is a flexible and comprehensive way to establish those goals and develop an implementation plan. Contact Blumira today for a demo and to learn more about how our platform can support your business.
More from the blog
View All Posts
Social Engineering: The Human Element in Cybersecurity
Read More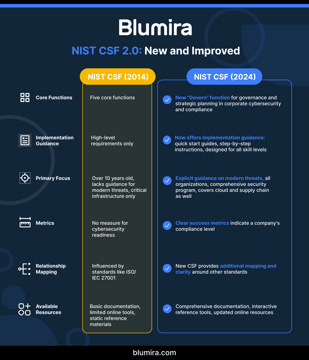
NIST Cybersecurity Framework Implementation for Mid-Market Companies: 2025 Update
Read MoreSmall Business, Big Risk: Decoding NIST's Strategy for Mid-Sized Business Security
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.