Download a PDF copy of the whitepaper
Introduction
1: Navigating Healthcare Security Challenges
2: Enablers to Effective Security for IT Teams
3: Value-Driven Enablers In Healthcare
4: Enablers To Demonstrating Compliance
HEALTHCARE SECURITY
1: NAVIGATING HEALTHCARE SECURITY CHALLENGES
The Complex Regulatory Environment
Securing healthcare environments presents immense challenges, especially in the United States, where healthcare is among the most highly regulated industries. From HIPAA to Medicare/ Medicaid requirements, the list of statutes healthcare organizations must comply with is extensive and continually growing.
Some of the key regulations include HIPAA, HITECH, the Emergency Medical Treatment and Labor Act, the False Claims Act, Stark Law, OSHA standards, nuclear medicine regulations, and ethics requirements stemming from the Affordable Care Act. Further complicating matters are payment card processing mandates under PCI DSS.
With new regulations added regularly, simply maintaining compliance across this complex web strains resources for healthcare organizations. The scope and interdependencies make it extremely difficult to remain fully compliant at all times.
Protecting Regulated Data
Aside from the sheer volume of data, healthcare environments have a large percentage of their workforce with access to sensitive information. This is driven by the fact that both patients and hospital workers (doctors, nurses, medical assistants, registration clerks, etc.) are transient – patients come in as needed, and staff may be working shifts 24 hours/day, or working across different locations on different days. You never know what patient will show up in the emergency room on any given day, and you never know exactly which doctors, nurses and support staff will be working at that time, so access to medical records is purposely broad to avoid any delays in patient care. These three items together – large volume of regulated data, large percentage of workers with access to regulated data, and purposefully broad access to patient data – make it difficult to manage the privacy and security of patient records.
Community Focus

Lean Staffing
With budget constraints and security teams purposefully lean, finding and retaining strong talent becomes even more necessary in healthcare. Salaries at hospitals and health systems are lower than other industries, and tools which are used to retain good talent such as educational reimbursement and training, are the first items on the chopping block when budget cuts are necessary.
Delays in hiring and training new security staff can increase risk for the organization. Lean staffing causes strict prioritization of critical tasks and organizations tend to increase their risk appetite to match the level of available technologies and support staff. Though organizations must always remain compliant, healthcare organizations with limited staff are more likely to deviate from well-established control practices, and implement less optimal controls which take less manual effort.
In 2023, technological advancements are moving at lightning speed, and it’s a challenge for any organization to maintain their staff competency in emerging technologies. Lean staffing models can exacerbate this situation, so training, education and retention are even more critical. Organizations operating with lean security staffing must work hard to retain funding necessary for staff competency training, and work with human resources on talent retention activities to reduce potential risk related to staff turnover.
2: ENABLERS TO EFFECTIVE SECURITY FOR IT TEAMS
Enablers to Effective Healthcare Security
At every organization, there are core security program capabilities necessary to maintain effective information security. Healthcare environments have similar needs to other industries, but have unique aspects specific to the challenges of patient care.Environment Visibility
As they say, you can only protect what you know about. To adequately protect an environment, security teams need strong visibility to everything in the environment. In healthcare, that not only means all the users and computers in the environment, but also anything that happens to be on the network or providing services, including medical devices, patient monitoring devices, critical cloud systems or hosting platforms, credit card processing devices and the like. Good visibility also requires accurate inventories of both systems and software in order to recognize and address unapproved devices and software.Data Inventory and Data Flows
Adequately protecting sensitive data and maintaining the privacy of patient data requires maintaining an accurate inventory of patient data. To maintain an accurate inventory, data flows must be documented to understand what data is coming into, and out of, the organization, and where that data is being stored. Hospitals send and receive large amounts of data every day as they work with healthcare insurance providers, clinical and IT service providers, state health departments, health information exchanges, laboratories, other hospitals, etc. HIPAA prohibits unauthorized access to patient records, and security and privacy teams need to understand where sensitive patient data is stored so that access can be appropriately monitored.Vulnerability Identification and Patch Management
Arguably one of the most important aspects of a strong security program is the processes surrounding vulnerability identification and patch management. Systems must be routinely scanned for configuration compliance, misconfigurations, and software vulnerabilities so that an organization can be adequately prepared for potential cyber-attacks. In a healthcare environment, this can be challenging as cloud tools may be different from on-premise tools, and there are devices in the environment (such as medical devices) which are managed by third-parties. As mentioned earlier, legacy devices can also be a challenge when software cannot be upgraded or removed from the environment due to its clinical criticality.Identity and Access Control (users, systems, APIs, etc.)
Echoing the HIPAA requirement prohibiting unauthorized access to patient information, identity management and access control are foundational elements in maintaining appropriate permissions across the organization. Strong verification processes, multi-factor authentication, expiration dates on accounts, and regular access reviews are all critical elements of good identity and access control practices. In healthcare, however, inappropriate access cannot be determined by permissions alone. Access tends to be very broad, so monitoring activities need to be in place to verify that workforce members are not accessing patient records they do not have a business reason to access. Even though a worker may have permission to access specific patient records, that does not mean they have a legitimate business reason to do so, and accessing records inappropriately can lead to employment or contract termination, and potentially criminal prosecution.Known and Anomaly-Based Threat Detection
Strong attack detection has been a need since the topic of security began. But in the past five years or so, machine learning attack detection has rapidly surpassed human ability to detect attacks, and the statistical methods used by security software are rooted in anomaly detection. Security tools need to be able to identify specific malware, but their true power lies in their ability to detect anomalous behavior, which can then be automatically or manually triaged to determine whether a significant threat exists.Detection and Response Processes
Detecting and responding to attacks is a critical function for security teams. Criminals are intelligent so they will apply techniques and tactics to evade detection, or will attack during nights and weekends to maximize their time before detection. Most security teams don’t have the luxury of staffing teams 24x7x365 so there is a time lapse where systems are not actively monitored by staff. Because of this, systems that can monitor and alert to potential incident activity 24x7x365 are critical to cover the time gap when staff are not actively working. In terms of responding to potential incident activity, organizations need processes that are tried and true and not ad-hoc or based on gut instinct. During an incident stress levels are high, and without strong process documentation, people revert to their instincts which may or may not lead to the desired end result. You never want to leave incident response to chance, so it’s important to have well documented processes and where possible, step-by-step instructions to help staff respond to incidents.
Educated Workforce
 Equally important is to have an educated workforce who are aware of the dominant types of attacks used today. Users should be trained in identifying suspicious activity, identifying phishing emails, practicing good security, and quickly contacting the help desk or security team when they suspect a potential security incident. Aside from end user awareness, the security team also needs to be educated. Security teams need to stay abreast of industry threats as well as best practices in applying security controls to reduce risk, and they need to be educated in the tools necessary to manage and monitor organizational assets, whether they are on premise, in the cloud, or in someone’s home. Security staff need continuous education to adapt to technological change and the change in attack methods used by cyber criminals.
Equally important is to have an educated workforce who are aware of the dominant types of attacks used today. Users should be trained in identifying suspicious activity, identifying phishing emails, practicing good security, and quickly contacting the help desk or security team when they suspect a potential security incident. Aside from end user awareness, the security team also needs to be educated. Security teams need to stay abreast of industry threats as well as best practices in applying security controls to reduce risk, and they need to be educated in the tools necessary to manage and monitor organizational assets, whether they are on premise, in the cloud, or in someone’s home. Security staff need continuous education to adapt to technological change and the change in attack methods used by cyber criminals.Third-Party Security
Another challenge in healthcare is the amount of third-parties that are used to deliver services, and the sensitivity of the data they can access. Health systems may leverage third-party physician or anesthesia staff, third-party software providers, third-party coding and billing providers, thirdparty medical device manufacturers, third-party ambulance services and many, many others. A large number of these service providers have access to, and even maintain, patient information on behalf of the health system. Healthcare organizations need strong processes to engage, evaluate, implement, and monitor services provided by third-parties to ensure appropriate security controls are being leveraged to manage risk to an acceptable level for the organization.Engage Outside the Security Department
With lean teams and tight budgets, healthcare security teams need to be creative in reducing security risk for the organization. One way to do that is by engaging “security champions” in the different areas of the business. Every department likely has one or more staff who are keen on technology or security and can provide value as a distributed supporter for the security team. These department champions can help in explaining security risks and concepts, can help implement those changes across different groups, and can improve adoption with their security advocacy. Often, these champions improve incident response time as they know business applications better than the security team. In essence, these department champions become part of an extended security team and provide additional manpower for the information security program.3: VALUE-DRIVEN ENABLERS IN HEALTHCARE
What are those functions and features of security programs and software that truly provide value to financially and resource-strapped healthcare organizations? Let’s examine them in the same way we looked at core security program capabilities in the last section.Visibility and System Inventory
Visibility is key for security teams, and healthcare organizations will typically have multiple tools that provide sources of system and network inventory. These could be vulnerability scanning systems, directory services, endpoint protection platforms, networking devices, medical device monitoring systems, etc. What drives value to a small healthcare security team is the ability to aggregate and orchestrate these data sources to provide a single, reliable source of truth. With a vast array of third-party integrations spanning on-premise and cloud platforms, Blumira XDR platform aggregates information sources and threat indicators to give security teams comprehensive visibility across their environment.Data Inventory and Data Flows
Maintaining an inventory of data and data flows can be challenging for any organization. Having a strong configuration management and application management platform can provide great value for not only tracking information about systems in use, but can provide the ability to document dependencies between systems, data flows between systems, and key metadata critical to security and compliance such as control gaps, exceptions, and whether systems or support staff operate overseas. For health systems that don’t have a good grasp on data inventory and data flows, Blumira can provide visibility into which systems interact with others, what logins are occurring to critical systems, and where those communications are taking place, which can provide visibility to the use of offshore resources.Vulnerability Identification and Patch Management
In a healthcare environment, vulnerabilities can be identified by different sources. Determining which results are duplicates, and why security tools rate them differently, is difficult. Blumira leverages multiple connectors to aggregate and normalize this information so that security teams spend less time analyzing differences in reports, and more time addressing the most significant risks for the organization. Blumira also deploys 5x faster than other security solutions, so organizations can quickly benefit from the normalization of data from the multiple sources.Identity and Access Control (users, systems,APIs, etc.)
Monitoring access to systems has been a foundational security control, but the review process can be manual and time-consuming. Having policies in place to alert on logins from outside the country, geographic impossibilities, or even additions to privileged groups, can be a huge time saver for small security teams. Blumeria consolidates these types of alerts and presents them in a prioritized format for follow-up by the organization’s security team.Known and Anomaly-Based Threat Detection
Many times, multiple email and malware protection tools are needed to effectively protect the organization and cover all attack vectors. These multiple tools put a time burden on lean security teams, who each have their own management consoles that need to be accessed to identify and address security risks. Blumira aggregates and normalizes these threat signals so risks can be managed from a single console, and with the Blumira XDR platform, response can be automated to save even more time for lean security teams.Detection and Response Processes
During incidents, stress levels are high. That’s when it’s important to have thorough, time-tested response processes to follow, so the stress factor doesn’t affect response to a threat. For lean information security teams, they may not have documented response processes, or if they do, the quality of those plans may be questionable because they rely on the experience level of the individual who documented the plan. Even for an experienced incident responder, it still takes time to review and roll out new procedures and plan updates as different threats are identified. Using a security platform that provides time-tested remediation plans for every threat that is detected saves significant time for lean security teams. This eliminates any frustration in locating response plans or determining that plans are out of date, because it’s all laid out for the incident responder. Blumira monitors your environment for threats 24x7x365 and maintains step-by-step playbooks that populate with every alert, so there is no guesswork when it comes to quickly identifying and responding to threats. Blumira also generates and rolls out new rules automatically, saving security team members time spent on analysis and deployment .Educated Workforce
Security teams need to stay abreast of industry threats, best practices in applying security controls to reduce risk, and they need to be educated in the tools necessary to manage and monitor organizational assets, whether they are on premise, in the cloud, or in someone’s home. For lean security teams who may not be able to acquire and maintain top talent, having a platform that automates the detection process and provides playbooks for every alert generated can add significant value, as it enhances the effectiveness of less-experienced staff. Blumira detects and prioritizes threats in a simple dashboard and provides playbooks for every alert . This doesn’t eliminate the need to train staff, but it can make less experienced resources more productive in managing the security of the hospital environment.Third-Party Security
Healthcare organizations need strong processes to engage, evaluate, implement, and monitor services provided by third-parties to ensure appropriate security controls are being leveraged to control risk to an acceptable level for the organization. Platforms that can identify suspicious login attempts from vendor partners, or highlight risks of activities occurring offshore, can identify potentially significant risks related to third-party security. Blumira aggregates and consolidates security threat signals and prioritizes them in an understandable format, so potential security risks related to thirdparties can be quickly identified and investigated.Engage Outside the Security Department
Leveraging resources outside the security department involves engaging champions in different lines of business, but isn’t limited to internal staff. Security service providers also function as an extension of the information security team, and provide additional expertise and off-hours coverage that many teams cannot provide themselves. Blumira’s platform and team provide that extended expertise in identifying and responding to threats, and operate 24 hours a day, 7 days a week.4: ENABLERS TO DEMONSTRATING COMPLIANCE
Maintaining a compliant security program in the healthcare industry can be complex, but demonstrating that compliance to external auditors or government regulators can demand a significant amount of time - putting additional pressure on an already lean team. Through Blumira’s comprehensive reporting platform, evidence can be provided to demonstrate compliance with multiple requirements, thus reducing the administrative burden on security staff. This allows healthcare staff to focus their attention on higher-value risk reduction activities for the organization. Blumira’s security platform supports many administrative, physical and technical safeguards contained in the HIPAA Omnibus rule (45 CFR Parts 160, 162, and 164). The table below describes how Blumira supports specific HIPAA controls for healthcare organizations.| HIPAA REFERENCE | REQUIREMENT | HOW BLUMIRA SUPPORTS COMPLIANCE |
|---|---|---|
| §164.308(a)(1)(i) | Implement policies and procedures to prevent, detect, contain, and correct security violations. | Blumira incorporates activity monitoring policies, thus allowing security teams to be alerted to undesired behavior, allowing them to act quickly to contain the security risk and potentially address any security violation. |
| §164.308(a)(1)(ii)(A) | Conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by the covered entity or business associate. | Blumira’s security reports can highlight risks to ePHI across the organization, and report trends for an entire year, helping demonstrate compliance and control effectiveness to regulators and insurance brokers. |
| §164.308(a)(1)(ii)(D) | Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports. | Blumira ingests logs from multiple security and system sources and performs automated monitoring to quickly highlight the most important risks that could affect the organization. |
| §164.308(a)(3)(i) | Implement policies and procedures to ensure that all members of its workforce have appropriate access to electronic protected health information | Blumira can alert on activity from accounts with elevated activity. Security staff can see who’s performing activities with elevated permissions and quickly respond if the activity or permissions appear to be inappropriate. |
| §164.308(a)(5)(ii)(B) | Implement procedures for guarding against, detecting, and reporting malicious software. | Blumira’s continuous monitoring capabilities can quickly detect and respond to potentially malicious activity. |
| §164.308(a)(5)(ii)(C) | Implement procedures for monitoring log-in attempts and reporting discrepancies. | Through its ingestion of security logs, Blumira can detect suspicious or anomalous login events, and provide alerts and reporting of those activities. |
| §164.308(a)(6)(ii) | Identify and respond to suspected or known security incidents; mitigate, to the extent practicable, harmful effects of security incidents that are known to the covered entity or business associate; and document security incidents and their outcomes | Blumira’s XDR and reporting capabilities can dynamically identify and respond to threats in the environment, and upon staff responding to alerts in the Blumira console, security incident documentation is generated which can be used to demonstrate due diligence and compliance. |
| §164.310(b) | Implement policies and procedures that specify the proper functions to be performed, the manner in which those functions are to be performed, and the physical attributes of the surroundings of a specific workstation or class of workstation that can access electronic protected health information. | Blumira’s XDR capabilities can monitor behavior on endpoint computing devices and alert on high-risk activities from end users or automated processes. |
| §164.310(c) | Implement physical safeguards for all workstations that access electronic protected health information, to restrict access to authorized users. | Blumira can leverage Windows kernel controls to isolate workstation access in situations where they may be accessed by unauthorized individuals. |
| §164.310(d)(2)(iii) | Maintain a record of the movements of hardware and electronic media and any person responsible therefore. | The Blumira agent’s visibility to workstations logs and activity enables consistent tracking of devices and media usage. |
| §164.312(b) | Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information. | Blumira’s cloud console is constantly ingesting logs from multiple sources to provide security teams superior visibility to user and device activity across the environment |
| §164.316(b)(2)(i) | Retain the documentation required by paragraph (b)(1) of this section for 6 years from the date of its creation or the date when it last was in effect, whichever is later. | With Blumira’s XDR platform, long term storage options exceeding 1 year are available to meet industry or company retention requirements. |

For more information on how Blumira helps healthcare organizations with security and compliance, we encourage you to visit https://www.blumira.com/industry/healthcare.
Blumira’s Free edition is available for unlimited users and data, no additional licenses required. For more information and to sign up free for Blumira’s self-service cloud SIEM, visit https://www.blumira.com/free.
More from the blog
View All Posts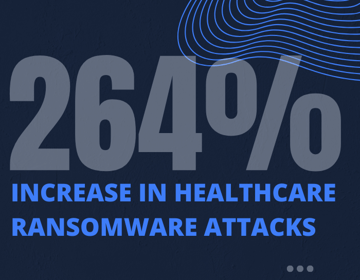
Reducing Risks to Protect Patient Data & Meet HIPAA Compliance
Read More
Ransomware in Healthcare: After-the-Fact is Too Late
Read More
Using the NIST CSF to Support GDPR and HIPAA Compliance
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.