- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
The term “malware” (short for “Malicious Software”) describes the software that is used to compromise or cause damage to a system or network. Essentially, malware is code with a malicious intent. The threat actor(s) that conducted the SUNBURST attack didn’t just use one piece of malware to achieve their objectives. They developed multiple types of malware for the SolarWinds attack, and the handful that researchers have identified so far certainly don’t fit into any one category by themselves. Malware taxonomy is the science of the classification of malware. I may be on my way to becoming a malware taxonomist, but I’ll try to make this quick and painless for us all, at least with this introduction.
The intention of this post is to give you a quick summary of the various pieces of malware that allowed the threat actors behind this supply-chain attack against SolarWinds to be successful while remaining undetected. For months, the threat actors that leveraged the supply chain attack against SolarWinds penetrated and remained undetectable against some of the world’s most secure networks. SUNSPOT, SUNBURST, SUPERNOVA, TEARDROP, and RAINDROP have been identified by researchers to be specific pieces of malware that worked together to act as a backdoor into a SolarWinds update framework.
SUNSPOT was the implant that allowed the threat actor the ability to inject the SUNBURST backdoor code into the software update pipeline. It’s also how threat actors added their malicious code to SolarWinds updates that were later deployed to SolarWinds customers. When executed, SUNSPOT ensures that only one instance of itself is running, and then creates an encrypted log file at C:\Windows\Temp\vmware-vmdmp.log.
SUNBURST was the backdoor patched into a SolarWinds update that remained dormant for up to two weeks after installation before reaching out to its command and control (C2) servers via HTTP to a subdomain of avsvmcloud[.]com.
TEARDROP was a memory-only dropper, or downloader malware, with the sole function of stealthily downloading and installing additional malware components. It ran as a service and was used to deploy Cobalt Strike Beacon. Cobalt Strike is a DARPA developed, military-grade attack framework designed to be both incredibly stealthy and malleable to allow for emulation of various types of command and control communication.
SUPERNOVA was a web shell seemingly designed to maintain persistent access to the system. SUPERNOVA created a stealthy and complete .NET Application Programming Interface (API) within an Orion binary. SUPERNOVA achieves stealth by operating entirely in memory, which makes detection much more difficult. SUPERNOVA was placed on systems by the threat actors after the initial breach and was not a part of the embedded SUNBURST payload, such as the aforementioned three.
RAINDROP was similar to TEARDROP, in that it dropped a custom payload of Cobalt Strike Beacon onto systems that it infected, but different in that it was not part of the initial SUNBURST backdoor delivery. Raindrop achieved stealth by leveraging SMB-based named pipes to establish internal peer-to-peer networks between infected hosts. Notably, this minimized the number of hosts required to beacon out, and helped the threat actor remain undetected.
There’s more to come with these posts about the malware that’s been identified to be associated with the SUNBURST attack, and surely more to come to the story as a whole. This advanced persistent threat (APT) actor is being referred to and/or tracked by a few different names: UNC2452, StellarParticle, Dark Halo, and SolarStorm. Most folks in the industry are convinced that this APT is part of an organized nation-state attack. The threat actors behind the attack that targeted public and private organizations across the world have not been publicly identified. The grapevines have been whispering, and research has been suggesting links to Russian involvement.
Adopting a Defense in Depth detection strategy can help increase the likelihood of detecting such stealthy threat actors. Though we certainly have a “new normal” in cybersecurity, it’s an ever-evolving world that we live in: both in and outside of cyberspace. We need to secure ourselves, in-depth. Become aware… and maybe even become aware how to be aware. That includes a solution to ensure you have the required visibility into your environment and know how to appropriately respond to threats and vulnerabilities.
At Blumira, our clients benefit from scales of economy when it comes to detections. Our team works tirelessly to emulate, test, and detect bad actors and guide you to taking appropriate action when anomalies are found.
Brian Henneberry
Brian is an experienced network and systems administrator with a strong background in information security training/awareness and technical support. He is a CompTIA certified Security Analytics Professional, having earned CompTIA's Network+, Security+, and CySA+ certifications. Brian has also earned the Microsoft MTA...
More from the blog
View All Posts
Security How-To
4 min read
| January 4, 2021
Detect & Protect Against the SUNBURST Backdoor
Read More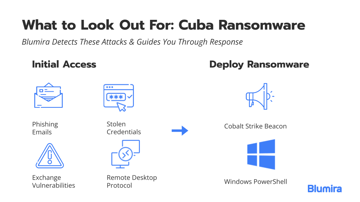
Security Alerts
6 min read
| December 9, 2021
How To Detect Signs of Cuba Ransomware
Read More
Security Trends and Info
10 min read
| January 11, 2022
SIEM Alerts To Expect During a Pentest
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.