Posts by Amanda Berlin
The Iranian Cyber Threat: Key Insights for IT Teams
Although there is currently a ceasefire in place, geopolitical tensions between the United States and Iran continue to escalate. As a result, we're witnessing a corresponding...
Read MoreAbout the Author
Amanda Berlin is the Senior Product Manager of Cybersecurity at Blumira, bringing nearly two decades of experience to her position. At Blumira she leads a team of incident detection engineers who are responsible for creating new detections based on threat intelligence and research for the Blumira platform. An accomplished author, speaker, and podcaster, Amanda is known for her ability to communicate complex technical concepts in a way that is accessible and engaging for audiences of all backgrounds. She co-authored an O’Reilly Media book Defensive Security Handbook: Best Practices for Securing Infrastructure, a comprehensive guide for starting an infosec program from the ground up. She has presented at various industry events, including Blueteam Con, RSA Conference, and DEFCON. She is also co-host of Brakeing Down Security, a podcast about the world of cybersecurity, privacy, compliance, and regulatory issues that arise in today’s workplace. Amanda is the CEO and co-founder of Mental Health Hackers, a non-profit organization that aims to raise awareness about mental health issues in the cybersecurity community. Through Mental Health Hackers, Amanda is working to break down the stigma surrounding mental health and create a supportive community for cybersecurity professionals. Passionate about educating others, Amanda frequently develops courses and leads tabletop sessions through organizations such as Antisyphon Training and Wild West Hackin’ Fest. Amanda is on multiple social media platforms as @InfoSystir, where she can be found sharing information security news, cracking jokes, and expressing her love for hedgehogs.

Security Detection Update - 2025-05-30
Read More
Security Detection Update - 2025-02-20
Read More
Security Detection Update – 2025-1-22
Read More
Security Detection Update – 2024-11-20
Read More
Security Detection Update – 2024-11-08
Read More
Security Detection Update – 2024-10-31
Read More
Security Detection Update – 2024-10-18
Read More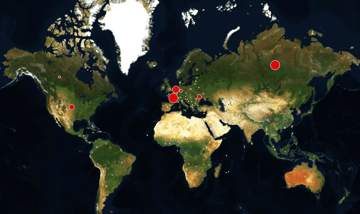
Security Detection Update – 2024-10-3
Read More
Security Detection Update - 2024-9-19
Read More
Security Detection Update - 2024-9-10
Read More
Security Detection Update - 2024-9-3
Read More
Security Detection Update - 2024-8-27
Read More
Security Detection Update - 2024-8-20
Read MoreHow To Use Nmap for Network Inventory and Asset Discovery
Read More
Security Detection Update - 2024-8-13
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
