Posts by Erica Mixon
The Iranian Cyber Threat: Key Insights for IT Teams
Although there is currently a ceasefire in place, geopolitical tensions between the United States and Iran continue to escalate. As a result, we're witnessing a corresponding...
Read MoreAbout the Author
Erica is an award-winning writer, editor and journalist with over ten years of experience in the digital publishing industry. She holds a Bachelor’s degree in writing, literature and publishing from Emerson College. Her foray into technology began at TechTarget, where she provided editorial coverage on a wide variety of IT topics, from virtual desktops and Windows to data center infrastructure. In 2020, the American Society of Business Publication Editors (ASBPE) recognized her work for covering Citrix Synergy, an annual user conference. In 2021, ASBPE awarded her the Young Leader Scholarship, which recognizes up-and-coming leaders under 30 in the B2B industry. At Blumira, she covers topics such as ransomware, Windows security, and zero-day vulnerabilities.

Compliance: From Cost Center To Revenue Driver
Read More
Saving Time (and Sanity) in Healthcare Security
Read More
5 Tools To Make The Most Of Your Security Budget
Read More
Choosing Cybersecurity Framework: NIST vs. CIS
Read More
Sysmon 101: Leveling Up Windows Security
Read More
6 Tips for a Remote Working Security Policy
Read More
How to Select a SIEM for CrowdStrike
Read More
How to Select a SIEM for Google Workspace
Read More
How to Select SIEM for Microsoft 365
Read More
20-Minute Live Demo: Blumira XDR
Read More
Monitor Remote Employees Ethically and Effectively
Read More
5 XDR Features Small Businesses Should Prioritize
Read More
XDR: Better Security Outcomes
Read More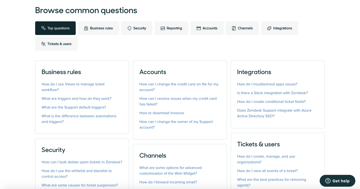
Top Help Desk Tools 2023: Choose the Best for Your Needs
Read More
Blumira By The Numbers in 2022
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
