- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Posts by Nick Dixon
Kindling Agentic Context Engine Cuts Alerts by 90% Through Auto-Triage
6 min read
| May 13, 2026
A finding fires at 2am. Your analyst opens the alert and starts from scratch. No context, no guidance, just raw log data and a clock ticking. By the time they've pieced...
Read MoreAbout the Author
Nick is a cybersecurity professional with over a decade of experience in IT security and operations management. A Detroit native and graduate of Eastern Michigan University's Information Assurance program, he currently serves as Security Analysts & Technical Support Manager at Blumira, where he has advanced through multiple leadership roles over the past seven years, progressing from Incident Detection Engineer to his current management position. Prior to Blumira, Nick developed his expertise as a Security Analyst at NetWorks Group, providing 24/7 managed detection and response services, including network traffic investigation, active intrusion response, and threat research. He combines strong technical security operations expertise with excellent interpersonal and leadership skills, making him effective at both hands-on security analysis and team management.
Blog
28 min read
| June 5, 2026
Microsoft Teams Helpdesk Impersonation Attack Explained
Read More
Security Trends and Info
9 min read
| July 2, 2025
The Iranian Cyber Threat: Key Insights for IT Teams
Read More
Compliance Security Frameworks and Insurance
5 min read
| June 26, 2024
Compliance Conundrum: Does Cybersecurity Hinder Credit Union Progress?
Read More
Product Updates
5 min read
| October 24, 2023
Elevate Security Response with Blumira’s Security Operations Team
Read More
Security Alerts
6 min read
| November 1, 2022
OpenSSL Vulnerability: What You Should Know
Read More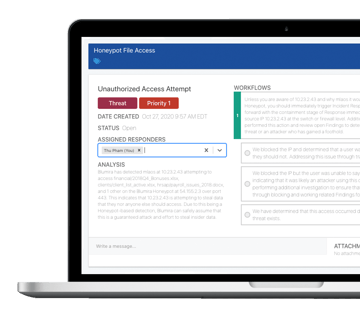
Product Updates
4 min read
| March 17, 2021
Product Update: Automating Honeypot Security Detections
Read More
Security How-To
4 min read
| March 1, 2021
Lock Down PowerShell or Else!
Read More
Security Alerts
7 min read
| January 28, 2021
Top 10 Security Detections of 2020
Read More
Product Updates
6 min read
| December 1, 2020
Blumira’s Security Operations Team Assistance on Integrations
Read More
Security Alerts
3 min read
| July 6, 2020
What You Need to Know About the Severe F5 BIG-IP Vulnerability
Read More
Product Updates
8 min read
| May 5, 2020
Blumira’s Threat Hunting Playbook
Read More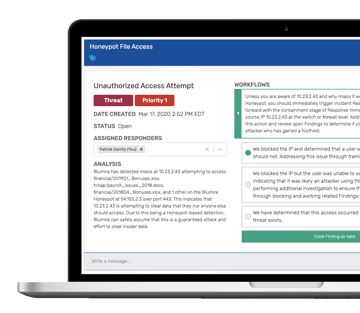
Security How-To
4 min read
| April 20, 2020
Hands in the Honeypot: Detecting Real Security Threats
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
