On Tuesday, December 28, tech media outlets began reporting ‘LastPass master passwords may have been compromised’ or ‘Hackers are going after LastPass master passwords’. No surprise here – according to the latest Verizon Data Breach Investigations Report (DBIR), today’s hackers have a preference for stealing credentials over more complex attacks, so password manager accounts are obvious targets for credential stuffing attacks.
If you lack basic password hygiene (like using strong passwords, changing them on occasion, and never re-using them), your password has probably already been cracked, leaked, or stolen. And, if you use a password manager and don’t follow vendor recommendations and best-practices (like using multi-factor authentication), your password manager will probably get hacked.
While there seems to have been a recent uptick in credential stuffing attacks targeting LastPass accounts, there doesn’t seem to be any evidence of anything having been breached or compromised – other than LastPass master passwords used in the attacks, which were already compromised.
Some misinformation seems to be spreading, and we’ve had clients ask us if LastPass was breached or if LastPass was exploited. Inflammatory headlines, new articles citing concerns over LastPass’ use of embedded trackers from earlier this year (which is a genuine privacy concern, but unrelated to potential LastPass compromise) and Tweets like this one don’t really help:

So, we wrote this blog to summarize what happened, what you should do if you’re a LastPass user, and what any organization can do to detect and respond to credential stuffing attacks.
What happened?
Was LastPass hacked? Not exactly. Some LastPass accounts became targets of credential stuffing attacks. According to most of the media coverage, this was first reported on ycombinator’s Hacker News (HN) forum. In this case, attackers seemed to have obtained the account’s master password (probably from a leaked password database that has nothing to do with LastPass). But, at least some of these attempts were blocked by LastPass’ security tools, and the account was otherwise protected by two-factor authentication (2FA).
Many other LastPass users replied to the post on HN and stated that they were experiencing similar activity, and that soon began to echo on Reddit, Twitter, and elsewhere.
This chatter indicates an uptick in credential stuffing attacks targeting LastPass accounts, but there doesn’t seem to be any evidence of account breaches or compromise.
Here’s the latest statement that LastPass provided to AppleInsider’s request for information:
“LastPass investigated recent reports of blocked login attempts and we believe the activity is related to attempted ‘credential stuffing’ activity, in which a malicious or bad actor attempts to access user accounts (in this case, LastPass) using email addresses and passwords obtained from third-party breaches related to other unaffiliated services,” LastPass spokesperson Meghan Larson told us. “It’s important to note that, at this time, we do not have any indication that accounts were successfully accessed or that the LastPass service was otherwise compromised by an unauthorized party. We regularly monitor for this type of activity and will continue to take steps designed to ensure that LastPass, its users, and their data remain protected and secure.”
What should LastPass users do?
First, know this: credential stuffing attacks happen all day every day to LastPass accounts and everything else on the internet, and these attacks rely on credentials that have already been compromised. For that reason, you should be practicing good password hygiene to mitigate the risk of credentials being cracked, leaked, or stolen, and you should use the strongest available multi-factor authentication options wherever possible to protect ALL of your accounts from credential stuffing using compromised credentials. A secure single-sign on solution is one way to implement multi-factor authentication across your applications while improving user experience.
That being said, LastPass offers security features that users can implement to protect their accounts. For starters, all LastPass tiers (including free personal accounts) support multi-factor authentication (MFA). If you’re not already using MFA, you should go set this up right now.
For LastPass Premium, Business, and Enterprise users, review your security dashboard and follow guidance to improve your security score. The security dashboard allows you to make sure that all of your users are practicing good password hygiene, avoiding password reuse (a leading cause of credential theft), and avoiding passwords that are already compromised.
What else can I do to detect and respond to credential stuffing attacks?
Any security practitioner will tell you that good cyber hygiene is the most effective way to protect against most attacks, and it should be the first line of defense. After that, event logs generated by your systems and applications can provide insights that can be used to improve cyber hygiene, or early-warning signs that can be used to respond to an attack before it results in a breach.
In order to get insights or early-warning signs from data contained in massive volumes of event logs, the data need to be analyzed and filtered to avoid false-positives and provide actionable alerts. Security Information and Event Management (SIEM) tools exist to solve this problem, and a well-tuned SIEM can be a nightmare for a hacker (or a penetration tester).
SIEM solutions come in all shapes and sizes. Some solutions are infinitely scalable and extensible but require significant tuning effort (and even development) to use effectively, while others may have a more limited set of features but can be seamlessly integrated with common systems and deployed without much pain.
Depending on the size of your organization, you may be well-served by engaging a managed security service provider (MSSP) to deploy and manage a SIEM for you, or you may be a good fit for deploying and managing a SIEM in-house.
How does Blumira prevent credential stuffing attacks?
Since we’re on the topic of LastPass, we wanted to provide a specific example of a quickly deployable SIEM solution that integrates with LastPass for detecting these types of attacks. We find that Blumira strikes a nice balance between features and configurability while providing out-of-the-box integrations and detections (including LastPass) that require almost no tuning.
Blumira took us less than a few hours to set up with integrations for LastPass (which only took a few minutes), Duo, Windows and Linux endpoint logs, Microsoft 365, Azure, Cisco, Meraki, and GSuite. During our testing, we were able to trigger findings in Blumira of a LastPass policy violation like this one:
Among other things, Blumira also watches out for anomalous user behavior in the LastPass environment, and/or activity coming from an IP address with a poor reputation, both of which could help detect attacks like the credential stuffing we’re hearing about in the news right now.
Ultimately, proper security comes in multiple layers, but none more important than the basics:
- Good Password hygiene
- MFA all of the things – with security keys or on-device prompts where possible
- Secure SSO + MFA = even better
You don’t have to do it alone. Partner with IT security professionals who can guide your security journey and add additional layers of security without impacting end-user productivity.
For more information about partnering with Blumira — and to learn how you can start using Blumira for free via NFR licensing — visit blumira.com/partners/.
Jon Isaacson
Jon Isaacson is a cybersecurity consultant with over 15 years of experience in cybersecurity, enterprise software, and U.S. government cyber operations. Prior to founding JTI Cybersecurity, he held several senior technical positions at technology companies and defense contractors. Jon built the product security team...
More from the blog
View All Posts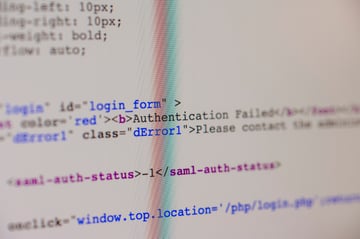
Authentication Protocols 101: NTLM, Kerberos, LDAP and RADIUS
Read More
A Guide To Cybersecurity Deception Techniques
Read More
RSA 2022 Day 1: The Importance of Identity
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
