- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Why You Need An Incident Response Plan
An effective Incident Response Program includes written procedures that clearly define responsibilities and tasks for each role. Responding to incidents can be stressful, often spanning days, weeks, or sometimes even months.
Well-documented procedures not only provide guidance to help responders successfully handle incidents, but also help minimize errors throughout prolonged response processes. Clear documentation reduces reliance on individual responders’ memories and judgments under pressure, enabling more consistent and accurate execution of response plans. With detailed procedures in place beforehand, responders can focus on analysis and restoration rather than determining next steps.
The best practices in this article are organized according to guidelines set by the National Institute of Standards and Technology (NIST) Computer Security Incident Handling Guide. In this guide, incident response procedures are broken down into four stages:
- Preparation,
- Detection & Analysis,
- Containment, Eradication, & Recovery,
- and Post-Incident Activity.
We’ll explore these stages in a high-level overview and discuss how to build procedures around them.

Assumptions
This article aims to provide organizations practical guidance on building an effective response to handling security incidents in a prompt and efficient manner. It assumes you’ve established a basic security program including centralizing logs in a security information event management (SIEM) tool like Blumira. Establishing a security program will provide incident responders with the tools necessary to quickly detect, analyze, and respond to incidents.
Preparation
Effective preparation for security incidents requires establishing an incident response team, providing them with necessary tools, and training incident responders to utilize those tools in protecting systems and networks. A mature security program implements monitoring, logging, and detection capabilities enabling the incident response team’s ability to obtain the information needed to detect, analyze and respond to incidents.
At minimum, preparation procedures should document:
- Reporting methods for potential incidents; at least one method should allow anonymous reporting.
- Contact information for the incident response team or third-party provider.
- Where to store incident reports and who should be able to access them.
- How and when to assemble the incident response team.
- Required physical equipment like forensic workstations and storage for evidence collection.
- Essential software for detection and response including AV, EDR, SIEM, and forensics tools.
- Documentation of internal assets, networks, critical systems, network diagrams, and asset inventories.
Detection & Analysis
Detection of security events is critical for an organization to respond to and remediate security incidents. Core tools for detection and analysis include Security Information and Event Management (SIEM) and Endpoint Detection and Response (EDR) solutions. However, these tools are only effective if all assets an organization would like to secure are shipping logs to a SIEM and are being monitored by an EDR solution.
Validate the incident. Detection procedures should outline general guidelines to help incident responders validate potential incidents and identify impacted assets. Understanding the devices and networks segments at risk is necessary to scope and effectively contain an active security incident. Analysis playbooks empower responders to thoroughly investigate various incident types.
Detection and analysis is not a discrete phase – it initiates the incident response process and enables ongoing investigation throughout containment, eradication, and recovery.
Containment, Eradication, Recovery
Once a compromise is detected, responders may shift to containment, eradication, and recovery. This phase often intersects with ongoing detection and analysis in an iterative process.
Containment procedures outline responding to incidents of varying severity and for varying asset types. Predetermining appropriate containment responses, like when to isolate a user workstation vs. when to isolate a domain controller, enables effective response action within an organization’s risk tolerance.
Eradication procedures provide steps to resolve the root causes of incidents by modifying existing system and network configurations. This includes removing malware, deleting unauthorized accounts, and patching exploited vulnerabilities.
Recovery procedures enable restoring applications, systems, and networks to a known good state. This may involve reverting to backups, resetting account credentials, adding firewall rules, and raising logging levels to support future response. Defined recovery processes help responders swiftly restore services.
Key aspects to address in containment, eradication, and recovery procedures include:
- Criteria and methods for isolation at the network, host, account, and application levels.
- Protocols for evidence gathering aligned to investigative needs.
- Root cause analysis techniques to identify and remediate vulnerabilities.
- Validation testing to confirm threat removal and system integrity.
- Backup and restoration methodology for affected assets.
- Password resetting protocols including communication and enforcement.
- Process for controlled reconnection of isolated assets after remediation.
By planning these response aspects in advance, organizations can act decisively while minimizing business disruption when security incidents occur.
Post-Incident Activities
After an incident is resolved, conducting a post-mortem review is critical for organizations to improve security going forward. The post-mortem enables assessment of what transpired, the business impact, lessons learned, and actions to bolster defenses and response.
Key post-mortem activities include:
- Reviewing the timeline recorded in the Incident Report.
- Quantifying direct and indirect financial, operational, and reputational impact.
- Identifying gaps in detection, response, and containment.
- Interviewing involved personnel to capture feedback.
- Extracting lessons learned across technical, process, policy, awareness, and training.
- Updating policies, procedures, controls, and budgets based on findings.
- Communicating results to leadership and across the organization.
Performing thorough post-mortems in a blameless manner is key to capitalizing on incidents to bolster an organization’s overall security posture for the future.
How Blumira Can Help
Blumira’s cloud threat detection and response solution alerts your team about suspicious behavior that leads to security incidents and provides recommendations on next steps. Get started with Blumira by trying out our free SIEM.
For more information on how to develop an incident response plan for malware infections, watch our on-demand webinar.
Additional Resources
For in-depth guidance on developing a comprehensive Incident Response Program, we recommend consulting the NIST Computer Security Incident Handling Guide. This article outlines best practices for incident response procedures based on the frameworks and methodologies detailed in the NIST guide. The guide serves as an invaluable resource for organizations looking to establish or mature their capabilities for detecting, analyzing, containing, eradicating, and recovering from security incidents. It provides actionable recommendations that can be tailored to an organization’s unique risk profile, resources, and objectives.
More from the blog
View All Posts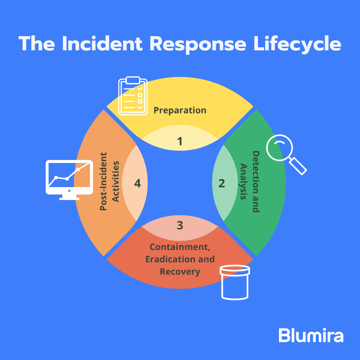
Security How-To
13 min read
| October 30, 2023
Incident Response Strategies for Ransomware
Read More
Security Trends and Info
8 min read
| June 2, 2021
Ransomware vs. Malware: What’s the Difference?
Read More
Security How-To
18 min read
| February 12, 2024
The Hedgehog Defense – Default Apps
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
