Microsoft Security
The Iranian Cyber Threat: Key Insights for IT Teams
Although there is currently a ceasefire in place, geopolitical tensions between the United States and Iran continue to escalate. As a result, we're witnessing a corresponding...
Read More
Customer Story: LEAP Managed IT Streamlines Ticketing and Boosts Visibility with Blumira’s API
Read More
Customer Story: NetCenter Technologies
Read More
Customer Story: United Way of Pierce County
Read More
Customer Story: Vangard IT
Read More
Customer Story: TR Computer Sales
Read More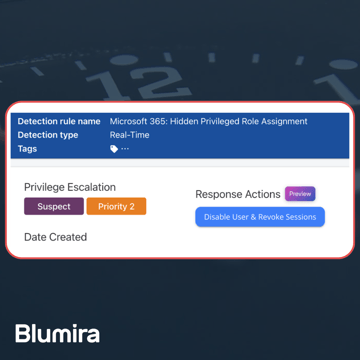
Blumira Launches New Microsoft 365 Threat Response Feature for Faster and More Efficient Security Operations
Read More
Now Available: Microsoft 365 Threat Response From Blumira
Read More
Customer Story: District of Sparwood
Read More
Microsoft Defender for Cloud Apps: Integrate with Blumira SIEM
Read More
Customer Story: Girl Scouts of Southeastern Michigan
Read More
Customer Story: Mid-Sized Manufacturing Firm
Read More
Detect and Respond to Azure Threats With Blumira: Easy Cloud SIEM Setup
Read More
Detecting and Preventing Ransomware Attacks in Microsoft Environments
Read More
Why are Threat Actors enabling Windows Restricted Admin mode?
Read More
The Hedgehog Defense #2: Defend Against Automatically Mounted Disk Images
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
