- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Security Alerts

Security Alerts
7 min read
| July 22, 2020
Detect and Protect Against Emotet Malware
Read More
Security Alerts
3 min read
| July 14, 2020
What You Need to Know About SigRed: Windows DNS Vulnerability (CVE-2020-1350)
Read More
Security Alerts
3 min read
| July 6, 2020
What You Need to Know About the Severe F5 BIG-IP Vulnerability
Read More
Security Alerts
5 min read
| June 23, 2020
RDP Risk: Ransomware Targets Manufacturing and Energy Plants
Read More
Security Alerts
9 min read
| June 15, 2020
Top Security Threats: Lateral Movement
Read More
Security Alerts
4 min read
| June 11, 2020
Common Threat Vectors & Industrial Control Systems (ICS): Modern Cybersecurity Practices, Part 2
Read More
Security Alerts
9 min read
| May 27, 2020
Top Security Threats: Detecting Ransomware Tactics
Read More
Security Alerts
10 min read
| May 26, 2020
Detecting RDP Attacks With Honeypots: Blumira Data Insights
Read More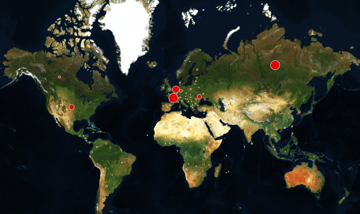
Security Alerts
2 min read
| May 19, 2020
Protecting Against the Rise in Remote Access Attacks - On-Demand
Read More
Security Alerts
12 min read
| April 21, 2020
Threat Analysis: PowerShell Malicious Activity
Read More
Security Alerts
5 min read
| April 6, 2020
Is Zoom Secure? Five Best Security Practices
Read More
Security Alerts
5 min read
| March 5, 2020
Internet Explorer Groundhog Day Critical Vulnerabilities
Read More
Security Alerts
4 min read
| January 14, 2020
Windows Certificate Spoofing Vulnerability
Read More
Security Alerts
6 min read
| January 13, 2020
What is the Citrix Gateway exploit? How should I respond?
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.