- Product
Product Overview
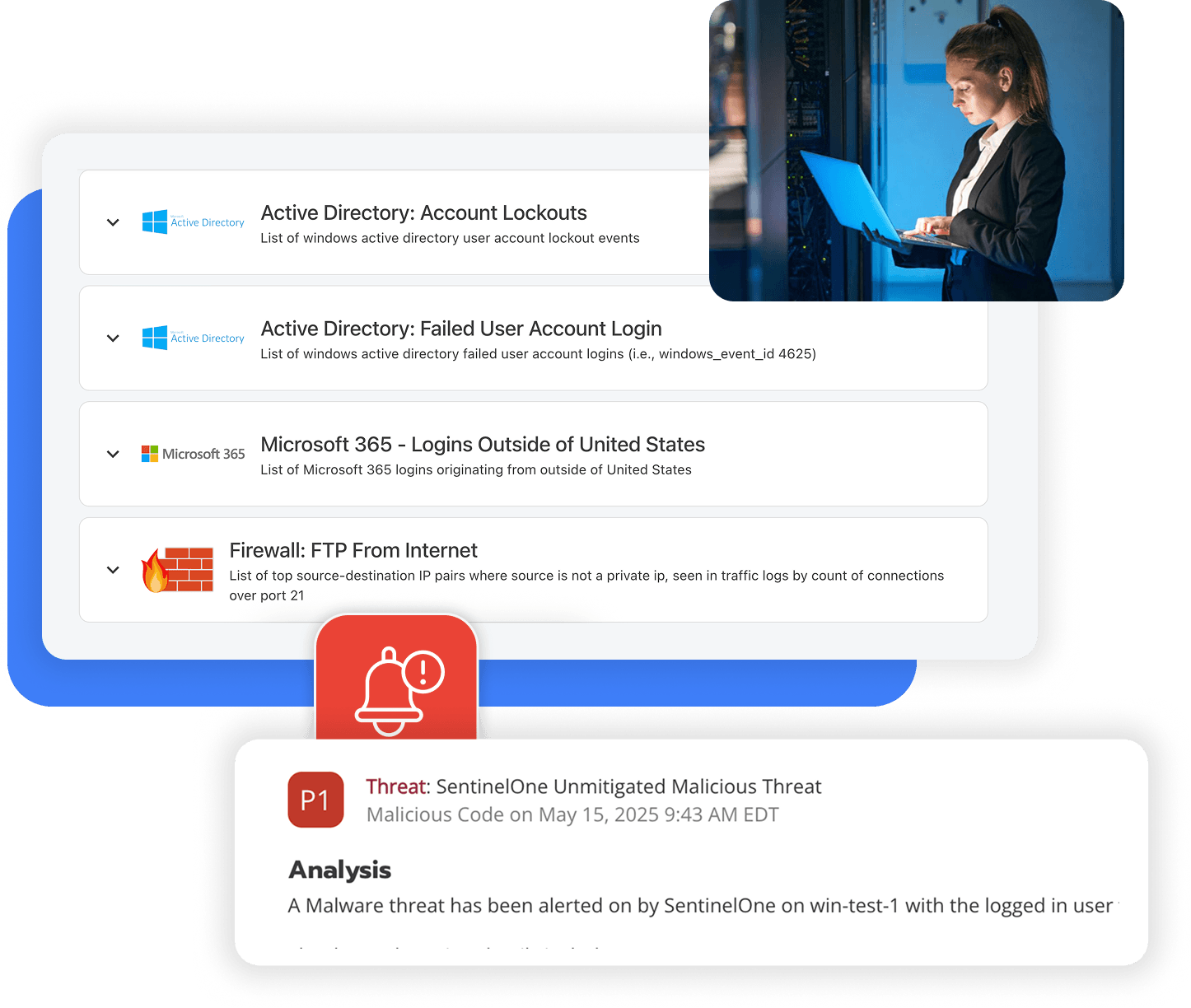
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
How Blumira Helps With
A Guide to the NIST Cybersecurity Framework (CSF)
Blumira’s security platform helps organizations easily meet and support multiple NIST CSF core functions and outcomes, including threat detection, security continuous monitoring, adverse event analysis, incident response reporting and communication, incident analysis, and more.
NIST Cybersecurity Framework
The NIST Cybersecurity Framework (CSF) 2.0 is designed to help organizations of all sizes and sectors — including industry, government, academia, and nonprofit — to manage and reduce their cybersecurity risks. Although not prescriptive, the CSF assists its users in learning about and selecting specific outcomes.
The CSF core functions organize cybersecurity outcomes at their highest level: Govern, Identify, Protect, Detect, Respond, and Recover.
- Govern: Cybersecurity risk management strategy, expectations, and policy are established, communicated, and monitored.
- Identify: Understand and manage cyber risks to systems, assets, data, and capabilities.
- Protect: Implement safeguards to prevent or limit the impact of cybersecurity incidents.
- Detect: Develop and implement capabilities to identify cybersecurity events promptly.
- Respond: Take appropriate actions to mitigate the impact of cybersecurity incidents.
- Recover: Restore affected systems, services, and capabilities to normal operations after a cybersecurity incident.
How Blumira Helps With DE: Detect
DE.CM: Security Continuous Monitoring
-
DE.CM-01
Networks and network services are monitored to find potentially adverse events
Blumira automates the monitoring of an organization’s network and environment to help identify anomalies indicative of malicious acts and operational errors, analyzing them with detection rules designed to determine if they are a security event. Blumira has rules that identify potential use of compromised credentials, unauthorized access, connection of unauthorized software and more.
-
DE.CM-03
Personnel activity and technology usage are monitored to find potentially adverse events
Blumira retains security event logs for up to one year. That gives you an audit trail to trace malicious activity back to specific users, with IP addresses, usernames, timestamps, and more to help your organization investigate any suspicious activity related to both internal and external threats. The Blumira platform monitors remote access attempts (through VPNs, two-factor authentication, etc.) and any anomalous user activity, such as data exfiltration or lockouts, that may be indicative of compromised accounts or attacker lateral movement. Blumira’s honeypots also provide deception technology to track unauthorized access attempts.
-
DE.CM-06
External service provider activities and services are monitored to find potentially adverse events
Blumira's platform integrates with a wide range of third-party applications, cloud infrastructure and service providers; collecting logs and analyzing them for potentially adverse events. These detection rules are written, tested, tuned and updated by incident detection engineers, looking for signs of attacker activity. Real-time alerts are sent to teams within minutes of initial detection with guidance on how to respond. Blumira’s platform provides 24/7 automated monitoring of third-party activity to protect against external and internal threats.
-
DE.CM-09
Computing hardware and software, runtime environments, and their data are monitored to find potentially adverse events
Blumira's platform integrates with applications, analyzing data and monitoring email, web, file-sharing, collaboration services and other common attack vectors to detect malware, phishing, data exfiltration, and other adverse events. Blumira monitors authentication attempts, identifying and notifying teams of attacks against credentials. Blumira detects indicators of malicious activity and malware, including ransomware, alerting teams within minutes of initial detection and providing guidance on how to respond. Blumira Agent monitors endpoints and performs automatic threat containment for affected devices, isolating them from the rest of the network to prevent the spread of malware until further investigation.
Networks and network services are monitored to find potentially adverse events
Blumira automates the monitoring of an organization’s network and environment to help identify anomalies indicative of malicious acts and operational errors, analyzing them with detection rules designed to determine if they are a security event. Blumira has rules that identify potential use of compromised credentials, unauthorized access, connection of unauthorized software and more.
Personnel activity and technology usage are monitored to find potentially adverse events
Blumira retains security event logs for up to one year. That gives you an audit trail to trace malicious activity back to specific users, with IP addresses, usernames, timestamps, and more to help your organization investigate any suspicious activity related to both internal and external threats. The Blumira platform monitors remote access attempts (through VPNs, two-factor authentication, etc.) and any anomalous user activity, such as data exfiltration or lockouts, that may be indicative of compromised accounts or attacker lateral movement. Blumira’s honeypots also provide deception technology to track unauthorized access attempts.
External service provider activities and services are monitored to find potentially adverse events
Blumira's platform integrates with a wide range of third-party applications, cloud infrastructure and service providers; collecting logs and analyzing them for potentially adverse events. These detection rules are written, tested, tuned and updated by incident detection engineers, looking for signs of attacker activity. Real-time alerts are sent to teams within minutes of initial detection with guidance on how to respond. Blumira’s platform provides 24/7 automated monitoring of third-party activity to protect against external and internal threats.
Computing hardware and software, runtime environments, and their data are monitored to find potentially adverse events
Blumira's platform integrates with applications, analyzing data and monitoring email, web, file-sharing, collaboration services and other common attack vectors to detect malware, phishing, data exfiltration, and other adverse events. Blumira monitors authentication attempts, identifying and notifying teams of attacks against credentials. Blumira detects indicators of malicious activity and malware, including ransomware, alerting teams within minutes of initial detection and providing guidance on how to respond. Blumira Agent monitors endpoints and performs automatic threat containment for affected devices, isolating them from the rest of the network to prevent the spread of malware until further investigation.DE.AE: Adverse Event Analysis
-
DE.AE-02
Potentially adverse events are analyzed to better understand associated activities
NIST's implementation example: Use security information and event management (SIEM) or other tools to continuously monitor log events for known malicious and suspicious activity. Blumira's SIEM platform provides continuous log monitoring, alerting you to known malicious and suspicious activity with guidance on how to respond. Blumira also leverages threat intelligence feeds to enhance detection of threat actors and indicators of compromise. Blumira's reporting tools can generate automatic and scheduled reports on these findings. -
DE.AE-03
Information is correlated from multiple sources
Blumira aggregates log data generated by sources in your environment to a centralized location. The SIEM platform correlates data collected from different sources, allowing you to search and easily find all data related to an incident. The platform integrates with threat intelligence feeds to identify known malicious events across log sources. -
DE.AE-04
The estimated impact and scope of adverse events are understood
NIST's implementation example: Use SIEMs or other tools to estimate impact and scope, and review and refine the estimates. Blumira's SIEM platform comes with integrations and detection rules that automatically estimate and prioritize findings by criticality (or adverse events) to help organizations understand what needs immediate attention and response. Blumira Investigate can help organizations research impacted users, endpoints and more to determine the scope of an incident.
Potentially adverse events are analyzed to better understand associated activities
NIST's implementation example: Use security information and event management (SIEM) or other tools to continuously monitor log events for known malicious and suspicious activity. Blumira's SIEM platform provides continuous log monitoring, alerting you to known malicious and suspicious activity with guidance on how to respond. Blumira also leverages threat intelligence feeds to enhance detection of threat actors and indicators of compromise. Blumira's reporting tools can generate automatic and scheduled reports on these findings.Information is correlated from multiple sources
Blumira aggregates log data generated by sources in your environment to a centralized location. The SIEM platform correlates data collected from different sources, allowing you to search and easily find all data related to an incident. The platform integrates with threat intelligence feeds to identify known malicious events across log sources.The estimated impact and scope of adverse events are understood
NIST's implementation example: Use SIEMs or other tools to estimate impact and scope, and review and refine the estimates. Blumira's SIEM platform comes with integrations and detection rules that automatically estimate and prioritize findings by criticality (or adverse events) to help organizations understand what needs immediate attention and response. Blumira Investigate can help organizations research impacted users, endpoints and more to determine the scope of an incident.-
DE.AE-06
Information on adverse events is provided to authorized staff and tools
Blumira's platform generates alerts that are sent to teams of responders, with real-time notifications sent within minutes of initial detection of a security event. All log analysis findings can be accessed within the Blumira application, with a year of data retention available for review. -
DE.AE-07
Cyber threat intelligence and other contextual information are integrated into the analysis
To help inform Blumira’s platform of new threats and relevant security information, Blumira ingests different types of data feeds. Those include threat feeds, information/risk feeds and safe feeds. With this data, analysts can enhance detections and enrich data to help reduce the time to identify, respond and contain potential threats. Blumira's detection rules identify and notify responders about known vulnerabilities, hacker tools, malicious traffic and more seen in their environment. Each finding sent to responders includes an integrated analysis and description of the identified security event, the potential impact on the organization, and other relevant contextual information to help them with threat response. -
DE.AE-08
Incidents are declared when adverse events meet the defined incident criteria
Blumira can help support organizations in determining if an incident should be declared by providing security guidance from Blumira’s Security Operations (SecOps) team, available 24/7 for critical priority issues. Blumira’s security team helps organizations understand when critical security events are occurring, and provides assistance to help prevent and support organizations during and after incidents.
Information on adverse events is provided to authorized staff and tools
Blumira's platform generates alerts that are sent to teams of responders, with real-time notifications sent within minutes of initial detection of a security event. All log analysis findings can be accessed within the Blumira application, with a year of data retention available for review.Cyber threat intelligence and other contextual information are integrated into the analysis
To help inform Blumira’s platform of new threats and relevant security information, Blumira ingests different types of data feeds. Those include threat feeds, information/risk feeds and safe feeds. With this data, analysts can enhance detections and enrich data to help reduce the time to identify, respond and contain potential threats. Blumira's detection rules identify and notify responders about known vulnerabilities, hacker tools, malicious traffic and more seen in their environment. Each finding sent to responders includes an integrated analysis and description of the identified security event, the potential impact on the organization, and other relevant contextual information to help them with threat response.Incidents are declared when adverse events meet the defined incident criteria
Blumira can help support organizations in determining if an incident should be declared by providing security guidance from Blumira’s Security Operations (SecOps) team, available 24/7 for critical priority issues. Blumira’s security team helps organizations understand when critical security events are occurring, and provides assistance to help prevent and support organizations during and after incidents.RS: Respond
RS.AN: Incident Analysis
-
RS.AN-03
Analysis is performed to establish what has taken place during an incident and the root cause of the incident
Blumira provides an audit trail of events that occurred during incidents, giving organizations information about the assets and resources involved in each event. Blumira's findings also surface data about vulnerabilities and threat actor groups involved. Blumira Investigate can help teams analyze incidents to determine root cause and scope. -
RS.AN-06
Actions performed during an investigation are recorded, and the records’ integrity and provenance are preserved
Blumira provides a complete audit trail of events that occurred during incidents, with measures taken to ensure the logs cannot be tampered with or altered. Data is encrypted in transit and at rest, and access to the database is only granted to users that require it to do their jobs (least privilege access). -
RS.AN-07
Incident data and metadata are collected, and their integrity and provenance are preserved
Blumira’s platform gathers and correlates data across your environment (that’s configured for logging), then populates this data with every alert. That includes detailed information such as source, date, username, timestamp, source and destination addresses and more to help with forensic investigations. Additionally, Blumira’s reporting provides up to one year of log retention history available on-demand to assist with investigations. -
RS.AN-08
An incident’s magnitude is estimated and validated
Blumira provides an audit trail of events that occurred during incidents, giving organizations information about the assets and resources involved in each event. Blumira's findings also surface data about vulnerabilities and threat actor groups involved. Blumira Investigate can help teams analyze incidents to determine root cause, scope and if other assets are affected. Blumira Agent can automatically identify and isolate all affected devices to contain a threat immediately after detection, cutting off access to the network until further investigation.
Analysis is performed to establish what has taken place during an incident and the root cause of the incident
Blumira provides an audit trail of events that occurred during incidents, giving organizations information about the assets and resources involved in each event. Blumira's findings also surface data about vulnerabilities and threat actor groups involved. Blumira Investigate can help teams analyze incidents to determine root cause and scope.Actions performed during an investigation are recorded, and the records’ integrity and provenance are preserved
Blumira provides a complete audit trail of events that occurred during incidents, with measures taken to ensure the logs cannot be tampered with or altered. Data is encrypted in transit and at rest, and access to the database is only granted to users that require it to do their jobs (least privilege access).Incident data and metadata are collected, and their integrity and provenance are preserved
Blumira’s platform gathers and correlates data across your environment (that’s configured for logging), then populates this data with every alert. That includes detailed information such as source, date, username, timestamp, source and destination addresses and more to help with forensic investigations. Additionally, Blumira’s reporting provides up to one year of log retention history available on-demand to assist with investigations.An incident’s magnitude is estimated and validated
Blumira provides an audit trail of events that occurred during incidents, giving organizations information about the assets and resources involved in each event. Blumira's findings also surface data about vulnerabilities and threat actor groups involved. Blumira Investigate can help teams analyze incidents to determine root cause, scope and if other assets are affected. Blumira Agent can automatically identify and isolate all affected devices to contain a threat immediately after detection, cutting off access to the network until further investigation.RS.CO: Incident Response Reporting And Communication
-
RS.CO-03
Information is shared with designated internal and external stakeholders
Blumira helps support information-sharing with stakeholders by providing findings with contextual information about an attacker's observed TTPs (Tactics, Techniques, and Procedures) along every stage of attack. Some examples of TTPs include Network Denial of Service (DoS) attacks, exfiltration over alternative protocols, supply chain compromise, compromised cloud account credentials, public-facing application exploits and more.
Information is shared with designated internal and external stakeholders
Blumira helps support information-sharing with stakeholders by providing findings with contextual information about an attacker's observed TTPs (Tactics, Techniques, and Procedures) along every stage of attack. Some examples of TTPs include Network Denial of Service (DoS) attacks, exfiltration over alternative protocols, supply chain compromise, compromised cloud account credentials, public-facing application exploits and more.RS.MI: Incident Mitigation
-
RS.MI-01
Incidents are contained
Blumira Agent monitors endpoints, identifies potentially adverse security events and threats, then automatically performs containment actions by isolating affected endpoints from the rest of the network until further investigation. Blumira's platform notifies responders to take action, and provides options for manual endpoint isolation, as well as configuring containment by priority level (P1-P3).
Incidents are contained
Blumira Agent monitors endpoints, identifies potentially adverse security events and threats, then automatically performs containment actions by isolating affected endpoints from the rest of the network until further investigation. Blumira's platform notifies responders to take action, and provides options for manual endpoint isolation, as well as configuring containment by priority level (P1-P3).Frequently Asked Questions
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework (CSF) is a voluntary set of standards, guidelines, and best practices published by the National Institute of Standards and Technology for managing cybersecurity risk. Version 2.0, released in February 2024, is organized around six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. Unlike NIST SP 800-171 (which prescribes 110 specific controls for government contractors), the CSF is flexible and widely adopted across industries and organization sizes. Cyber insurance providers, industry regulators, and enterprise customers frequently reference the CSF when evaluating an organization's security maturity.
What changed in NIST CSF 2.0?
NIST CSF 2.0, released February 26, 2024, introduced several significant changes from version 1.1. The biggest addition is the Govern function, which addresses cybersecurity governance, risk management strategy, and supply chain risk management. The framework was also expanded in scope from critical infrastructure to all organizations, regardless of size or sector. CSF 2.0 added improved guidance on using Profiles (to assess current and target security states), updated references to current standards and practices, and updated implementation tier descriptions. Organizations that previously aligned to CSF 1.1 should review their programs against the new Govern function and updated outcome categories.
How does a SIEM map to the NIST CSF Detect function?
The Detect function in NIST CSF 2.0 contains two categories: Continuous Monitoring (DE.CM) and Adverse Event Analysis (DE.AE). DE.CM requires that assets are monitored to find anomalies, indicators of compromise, and other potentially adverse events. DE.AE requires that anomalies and potential adverse events are analyzed to characterize the events and detect cybersecurity incidents. A SIEM directly implements both categories by collecting logs from across your environment, applying detection rules to identify anomalous activity, and correlating events to distinguish genuine threats from noise. Blumira covers DE.CM through continuous log collection from 75+ integrations and DE.AE through automated threat detection and alert prioritization.
Does the NIST Cybersecurity Framework apply to small businesses?
Yes. NIST CSF 2.0 explicitly expanded its scope to include organizations of all sizes and sectors, not just critical infrastructure. For small businesses, the CSF provides a structured approach to security that scales with your resources. You do not need to implement every outcome at the highest tier on day one. The framework's tiered maturity model (Partial, Risk Informed, Repeatable, Adaptive) lets you start with basic practices and build over time. Many cyber insurance questionnaires map directly to CSF functions, so aligning your security program to the CSF can also simplify your insurance application process.
What is the difference between NIST CSF and NIST 800-171?
NIST CSF is a voluntary framework for managing cybersecurity risk, applicable to any organization. It is organized around six functions (Govern, Identify, Protect, Detect, Respond, Recover) and is intentionally flexible. NIST SP 800-171 is a mandatory set of 110 specific security controls that organizations must implement to protect Controlled Unclassified Information (CUI) in non-federal systems. It is required for government contractors, particularly in the defense supply chain where it forms the basis of CMMC. Many organizations use the CSF as their overarching security framework and implement 800-171 controls specifically when contract requirements demand it. There is significant overlap, but 800-171 is more prescriptive and its requirements are directly auditable.
How does Blumira support NIST CSF compliance?
Blumira primarily supports the Detect and Respond functions of NIST CSF 2.0. For Detect, it provides continuous monitoring (DE.CM) through real-time log collection from cloud, endpoint, network, and identity systems across 75+ integrations. It performs adverse event analysis (DE.AE) through automated detection rules that identify threats, anomalies, and policy violations. For Respond, it supports incident analysis (RS.AN) through detailed alert context and investigation tools, incident mitigation (RS.MI) through response playbooks and endpoint isolation capabilities, and reporting (RS.CO) through alert documentation and compliance-ready reports. The platform deploys in hours and takes about 15 minutes a day to manage.
Is NIST CSF compliance mandatory?
The NIST CSF itself is voluntary for private sector organizations. However, several regulatory and contractual contexts effectively require it. Executive Order 13800 (2017) required federal agencies to use the CSF for managing cybersecurity risk. Some state regulations reference the CSF as an accepted framework for demonstrating cybersecurity due diligence. Cyber insurance providers increasingly map their underwriting questionnaires to CSF functions. Enterprise customers, particularly in government, healthcare, and financial services, may require CSF alignment from their vendors. While no law forces a private company to adopt the CSF, organizations that do not align to any recognized framework will find it harder to win contracts, obtain insurance, and demonstrate security maturity to customers.
Additional Compliance Resources
View more
Compliance Security Frameworks and Insurance
5 min read
| March 3, 2026
OnDemand - Your CMMC Certification Playbook (and Pitfalls To Avoid)
Read More
Compliance Security Frameworks and Insurance
10 min read
| February 10, 2026
Customer Story: Enhancing Ottawa County’s Security with Blumira Solutions
Read More
Compliance Security Frameworks and Insurance
9 min read
| January 14, 2026
The New CMMC Compliance Rule: What It Means for Defense Contractors and How Blumira Makes Compliance Achievable
Read MoreExperience Blumira Today
Tired of fragmented security tools and alert fatigue? Blumira centralizes your security operations, offering deep insights and actionable intelligence to identify and remediate threats before they cause damage. Discover the power of proactive defense.