What Happened?
Researchers have released and reported active exploitation of a collection of four different vulnerabilities (CVE-2023-46805, CVE-2024-21887, CVE-2024-21888, and CVE-2024-21893) in Ivanti Connect Secure VPN and Ivanti Policy Secure appliances. These vulnerabilities allow attackers to remotely run elevated commands on the appliances.
How Bad is This Vulnerability?
Documented cases of exploitation and the impact of these attacks on organizations have resulted in CVSS scores ranging between 8.2 and 9.1. Networking devices that are susceptible to this issue include Ivanti Connect Secure (ICS), formerly known as Pulse Connect Secure and Ivanti Policy Secure gateways. These vulnerabilities impact all supported versions – Version 9.x and 22.x.. Threat actors have developed several custom tools like web shells and credential harvesters to maintain persistence and exfiltrate data from compromised appliances. They have also exhibited awareness of device configurations and logging to carefully cover their tracks. Between the broad vulnerability, active exploitation, and sophisticated tactics, this poses a serious breach risk with potential impacts like network access compromise, data theft, and lateral movement.
What Should I Do?
Apply Patches Immediately
Ivanti has begun releasing patches for affected appliances. Apply these patches to your versions of the impacted products as soon as they become available.
Implement Mitigations
If patches are not yet available for your version, apply the mitigations recommended by Ivanti immediately. However, note that some configurations can negatively impact the appliances and the guidance by Ivanti should be followed.
Reset Passwords
Immediately reset passwords for any systems or accounts that might have been compromised. This is especially critical for local user accounts on the appliance and any users who authenticated to the appliance during the period of known malware activity.
Use the Integrity Checker Tool (ICT)
Run the internal ICT first, followed by the external ICT to check for any tampering or bypass mechanisms installed by attackers. Share the ICT results with Ivanti for further analysis.
Follow the Hardening Guide
Mandiant has created a remediation and hardening guide that can be followed that is specific to the released vulnerabilities.
How Blumira Can Help
Researchers have identified many post-exploit attacks that utilize open-source tooling. Reports have listed programs such as Impacket, CrackMapExec, Iodine, and Enum4Linux among those exploiting these vulnerabilities. The Incident Detection Engineering team is actively working on creating additional detections surrounding known TTPs. Blumira also currently has many different detections for this activity including:
- Potential Impacket wmiexec.py Activity
- Suspected Cobalt Strike Service Execution
- Webshells by File Write (As also seen during MoveIT compromises)
It’s nearly impossible for admins to track every vulnerability, but Blumira’s security experts perform threat hunting on your behalf and develop detections in real time to protect your environment. Blumira is actively working on a detection for QueueJumper for its customers.
Blumira’s Free SIEM is easy to deploy; IT and security teams can start seeing immediate security value for their organizations.
Sign up for free and connect to your Microsoft 365 environment in minutes to start detecting and mitigating exposure related to Windows vulnerabilities.
Amanda Berlin
Amanda Berlin is the Senior Product Manager of Cybersecurity at Blumira, bringing nearly two decades of experience to her position. At Blumira she leads a team of incident detection engineers who are responsible for creating new detections based on threat intelligence and research for the Blumira platform. An...
More from the blog
View All Posts
Top 18 Tips to Secure SSH on Linux
Read More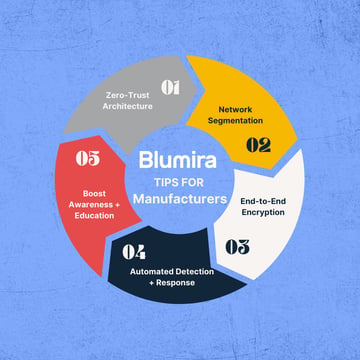
How to Secure Remote Access for Manufacturing Operations
Read MoreBlumira Domain Security Assessment Video
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.