- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
SOC Auto-Focus:
AI-Powered Investigations. Human-Backed Confidence.
AI Threat Analysis in 1 Click, Guided by Our Experts.
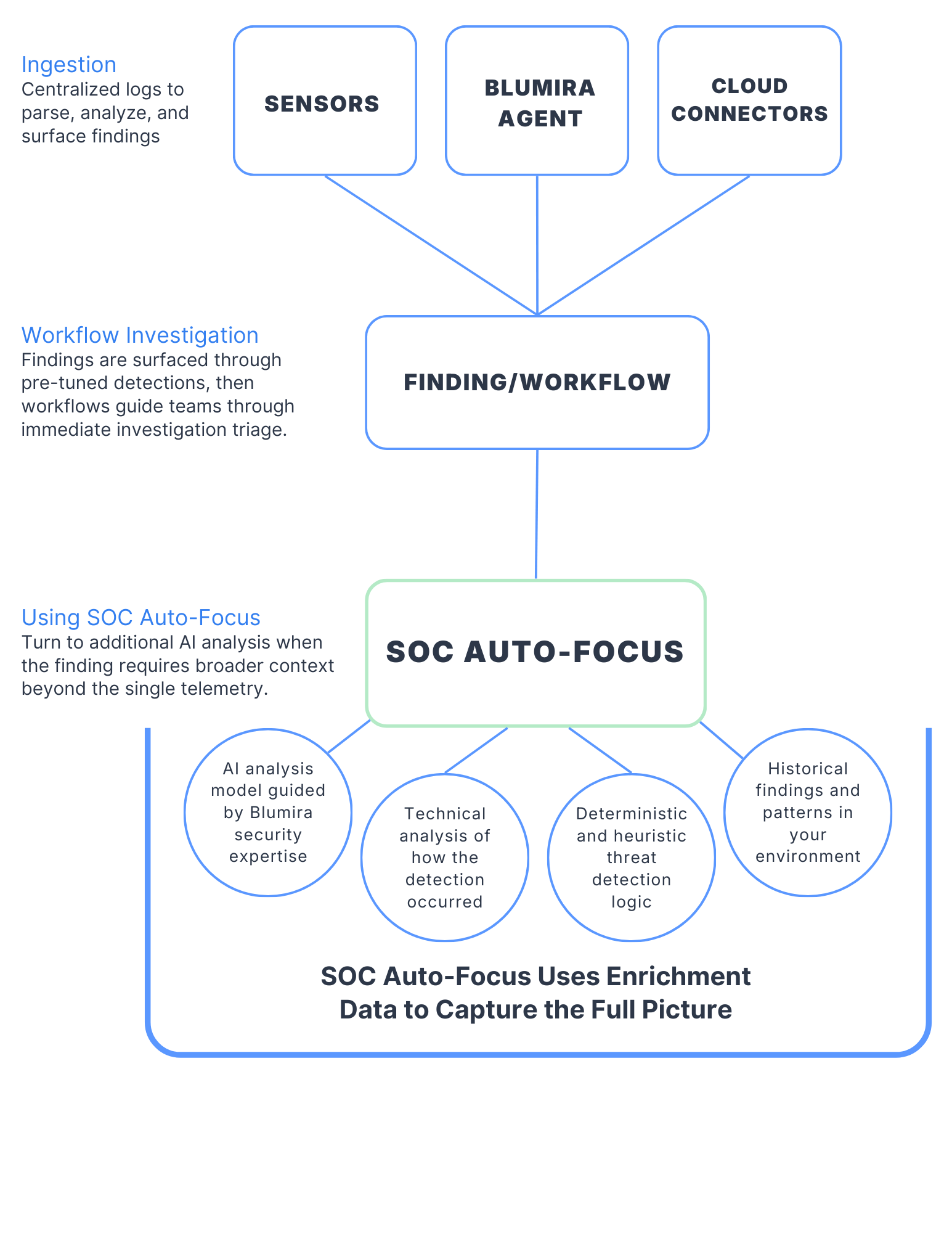
How It Works
See how SOC Auto-Focus rapidly accelerates and clarifies your investigations.
What SOC Auto-Focus Delivers
It's consistent, expert-level guidance coaching your team through every step, ensuring nothing is missed and every decision is made with confidence.
Instant Context
Get tailored insights drawn from patterns across related findings in your environment to understand what happened, why it matters, and the evidence behind it.
Clear Prioritization
See the criticality level, recommended response timeframe, and confidence rating so your team can focus on what needs attention first.
Guided Response with MITRE Tagging
Tailored investigation and remediation steps based on Blumira best-practices, with MITRE category tagging for documentation for audits.
Built-in Learning
Receive practical guidance that helps your team learn as they work. Auto-Focus provides consistent, expert-level guidance with every finding.
“We’ve been using Auto-Focus on unique, out of the ordinary alerts. It translates findings into plain English, human-readable summaries and has cut the time I spend on alerts in half.”
Travis
SOC Analyst Ninestar Connect
Unlike Other AI Solutions,
SOC Auto-Focus Provides
Deep Human Expertise, Not Magic Algorithms
Contextual Understanding, Not Generic Analysis
Day One Insight, No Training Required
Measurable ROI
Frequently Asked Questions
What is Blumira SOC Auto-Focus?
SOC Auto-Focus is a feature within the Blumira platform that automatically prioritizes security findings based on severity, context, and environmental factors. Instead of presenting every alert at the same weight, SOC Auto-Focus surfaces the findings that need attention first and suppresses noise from low-priority or informational events. It works alongside Blumira's pre-built detections and automated response capabilities, giving security teams (or the solo IT admin wearing the security hat) a filtered view of what actually matters right now.
How does SOC Auto-Focus prioritize alerts?
SOC Auto-Focus evaluates multiple factors: the severity of the detection rule that fired, the context of the affected asset (is it a domain controller or a test laptop), the behavioral pattern (is this a single event or part of a sequence), and whether automated response has already contained the threat. Findings that require immediate human action rise to the top. Events where automated response has already handled containment are deprioritized but still visible. The goal is to reduce the time between detection and meaningful human action on the alerts that matter.
Does SOC Auto-Focus replace human security analysts?
No. SOC Auto-Focus helps analysts (or IT generalists handling security) focus their limited time on the highest-impact findings instead of reviewing every alert sequentially. It is a prioritization layer, not a decision-making layer. Critical findings still require human review, investigation, and judgment calls. For organizations without dedicated security staff, SOC Auto-Focus is particularly valuable because it reduces the expertise needed to triage alerts. The 24/7 SecOps team is also available for direct support when an alert requires deeper investigation.
What data does SOC Auto-Focus use to rank findings?
SOC Auto-Focus draws from the same data the detection engine uses: log data from 75+ integrations (per blumira.com/integrations) across your cloud services, identity providers, endpoints, firewalls, and network devices. It factors in detection rule metadata (severity, confidence, threat category), asset context from your environment, historical alert patterns, and whether automated response actions have already fired. It does not require additional data sources or configuration beyond what you have already connected to Blumira.
How does SOC Auto-Focus reduce alert fatigue?
Alert fatigue happens when security tools generate so many notifications that the team starts ignoring them, including the important ones. SOC Auto-Focus addresses this by separating high-priority findings that need human action from lower-priority events that are informational or already handled. Instead of a flat list of hundreds of alerts, you get a prioritized queue. Blumira's automated response capabilities also reduce the total volume of alerts requiring human intervention by containing known threats automatically, so what reaches the analyst queue is smaller and more meaningful.
When is SOC Auto-Focus not enough for alert management?
SOC Auto-Focus prioritizes and filters, but it does not replace a detection and response strategy. If your environment generates a high volume of legitimate security events (large enterprise with complex infrastructure, heavily targeted industry), you may need dedicated SOC staff or an MDR service to handle the volume even after prioritization. SOC Auto-Focus also works within the detections Blumira provides. If you need custom detection logic for niche use cases, Blumira partners with you to build those rules, but SOC Auto-Focus itself does not create new detections, it prioritizes existing ones.
Blumira AI Security Resources

Product Updates
5 min read
| October 15, 2025
SOC Auto-Focus Cuts Investigation And Response Time Through AI-Powered Analysis
Read More
Product Updates
12 min read
| October 17, 2025
AI Integration at Blumira: How We Did It
Read More
Product Updates
9 min read
| October 16, 2025
The Human Side of AI: Why Blumira's Investigation Capabilities Put Partnership First
Read MoreIntegrated Security Operations
with AI
Cloud SIEM
Deploy in hours with pre-tuned detections and prioritized alerts for active threats and operational risks
Endpoint Visibility
Real-time monitoring and analysis, with automated blocklists and host isolation for compromised devices
Rapid Threat Response, Early Risk Awareness
Continuously monitoring for threats, and operational risks across your environment, with they automation, guidance, and support you need to address
Compliance & Investigation
Schedule automatic reports for CMMC, ISO, SOC 2, and other industry standards. Show immediate security ROI with executive summaries that speak in language your leadership understands.