Ransomware
Blumira Detections: Reduce Noise & Improve Your Time to Respond
Blumira’s detections help you save time, address risk, and reduce noise to help you protect your organization and increase operational resiliency.
Read More
SocGholish Coming Into Focus for Blumira
Read MoreImplementing Tabletop Exercises for Supply Chain IT and Cybersecurity Management
Read MoreCybersecurity and the Credit Union Mindset
Read MoreHow Manufacturers Can Secure Themselves Against Cyber Threats
Read MoreSafeguarding Municipalities Against Rising Cyber Threats
Read MoreSmall Business, Big Risk: Decoding NIST's Strategy for Mid-Sized Business Security
Read More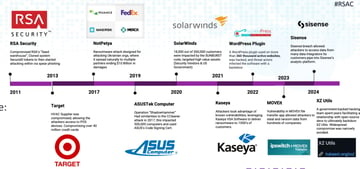
RSAC 2024 Global Threats Overview: Manufacturing, Supply Chains & School Districts Major Targets
Read More
9 Cybersecurity Measures to Protect Cities in 2024
Read More
Detecting and Preventing Ransomware Attacks in Microsoft Environments
Read More
Ransomware in Healthcare: After-the-Fact is Too Late
Read More
Small Business IT Guide: Defending Against Ransomware
Read More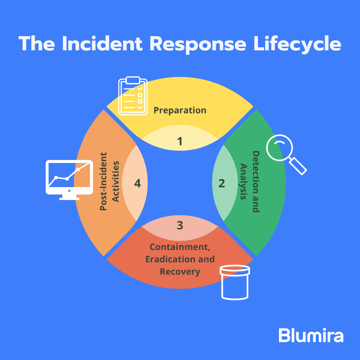
Incident Response Strategies for Ransomware
Read More
RSAC, DBIR 2022 Trends: Rise in Ransomware, Partner Attacks & Cyber Insurance
Read More
Shortening Ransomware Dwell Time Requires Fast Detection
Read More
Detecting Log4j Exploits Leading to Ransomware
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
