SIEM XDR
The Iranian Cyber Threat: Key Insights for IT Teams
Although there is currently a ceasefire in place, geopolitical tensions between the United States and Iran continue to escalate. As a result, we're witnessing a corresponding...
Read More
Customer Story: NetCenter Technologies
Read More
Customer Story: United Way of Pierce County
Read More
Customer Story: TR Computer Sales
Read More
SIEM Starter: A Budget-Friendly SIEM That Meets Compliance & Keeps You Secure
Read More
How our SIEM Playbooks Guide You Through Threat Response
Read MoreManual vs Automated Security Visibility for Resource-Constrained Teams
Read More
What is Unified Visibility and What Does it Offer?
Read More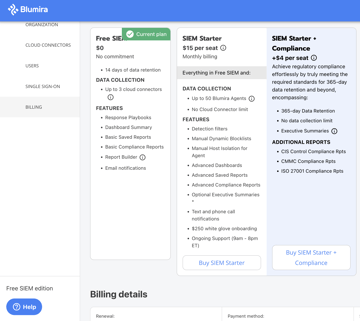
October 2024 Product Release Notes
Read More
WARNING: Some “SIEM” Vendors Are Not Actually Selling A SIEM
Read More
After the Sunset: Choosing Your Post-LogRhythm SIEM
Read MoreFear, Uncertainty, and Helplessness in Cybersecurity
Read More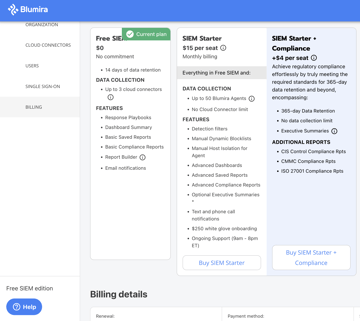
September 2024 Product Release Notes
Read MoreXDR Buyer's Guide
Read More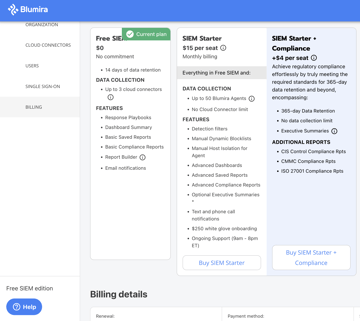
August 2024 Product Release Notes
Read MoreTraditional vs Modern SIEM vs Human MDR vs MSP
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
