- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Remote Work Security
Detect threats 5X faster and support remote Windows, MAC, and Linus endpoints with Blumira Agent.
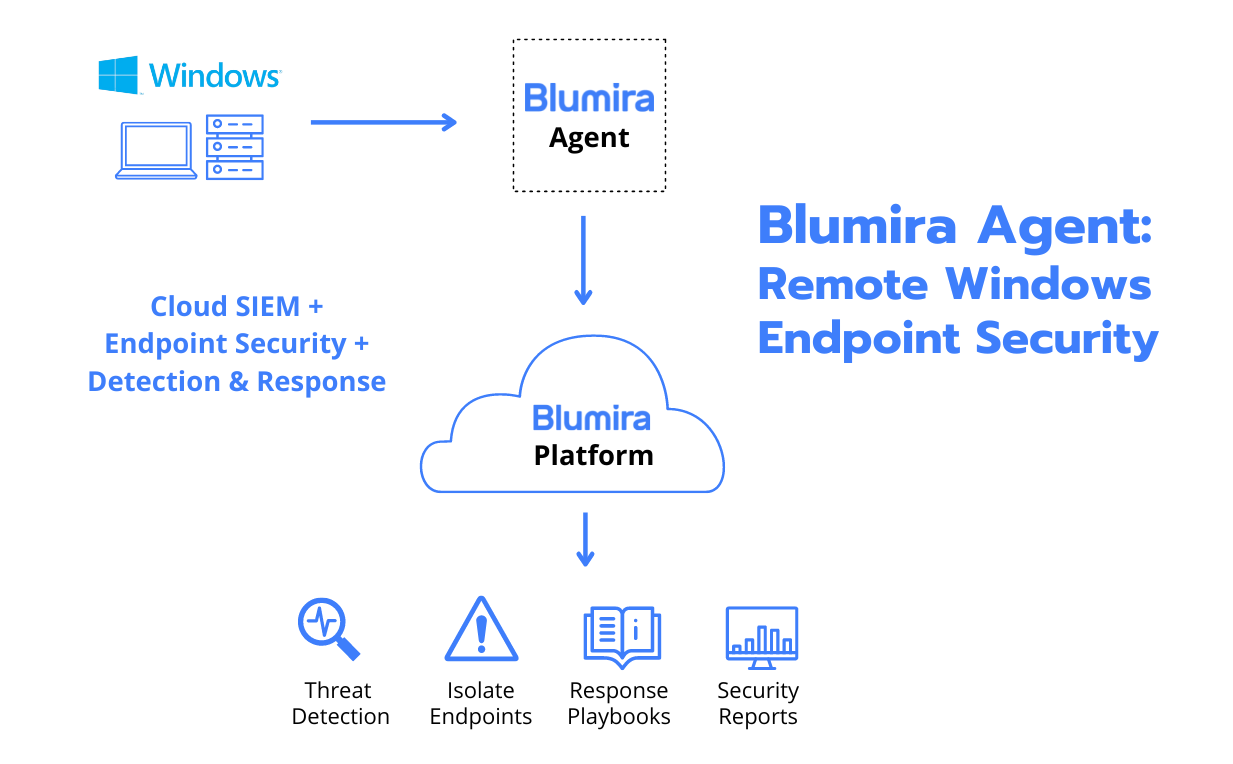
Blumira Agent
Securing Remote Windows Endpoints
Detect Windows endpoint threats early and often to prevent an incident before it results in damage or downtime. With Blumira Agent, you can extend your coverage in minutes to include your remote Windows workforce.
-
Identify remote attacker activity and prevent Windows endpoint attacks
-
Contain threats immediately with Blumira Agent host isolation to stop the spread of malware
-
Fast, easy setup with no on-prem infrastructure or sensors required
Securing Remote Work
Work from home and remote work has increased cybersecurity risk.
Shift to Cloud
Remote Access Risks
Cloud Collaboration Vulnerabilities
Endpoint Risk
What You Need for a Secure Remote Workforce
Here are just a few of the primary features you’ll need to ensure security across a remote workforce.
-
Secure Remote Access
Secure Remote Access
Visibility is the first step toward security. Blumira can help you get that insight by integrating with your identity and access providers to detect and alert you on anomalous user logins or activity, including Duo Security, Okta, and Microsoft Active Directory.
Blumira integrates with VPNs, such as Cisco AnyConnect and other remote gateways, to analyze incoming traffic for threats. We can also protect against geo-impossible logins in real time so you can quickly respond to potential account takeovers. -
Visibility & Prioritized Alerts
Visibility & Prioritized Alerts
To support a remote workforce, organizations are turning to collaboration and productivity tools. Blumira integrates with Microsoft Office 365 and Google Workspace to help you track and monitor user logins and activity for faster, automated detection and actionable response to an increase in remote attacks.
Enable your distributed workforce to connect seamlessly and securely by gaining visibility and alerts with Blumira. -
Support Cloud Migration
Support Cloud Migration
Blumira integrates with Microsoft Azure Event Hub to stream and centralize cloud security event logs and alerts. Blumira analyzes and correlates cloud logs to help identify indicators of attacker behavior and activity.
By prioritizing critical findings, Blumira also enables your team to respond automatically by blocking malicious sources, or by following guided security playbooks for remediation. -
Detect Endpoint Risks
Detect Endpoint Risks
Centralize visibility of your endpoint protection tools with Blumira. Quickly detect and respond to device-related risk such as malicious code, potentially unwanted programs (PUP), and spyware files.
Blumira integrates with endpoint security providers such as VMware Carbon Black Endpoint Protection, Carbon Black Response, Carbon Black Managed Defense, Microsoft Windows Defender, Crowdstrike Falcon Endpoint Protection, and many others.
Secure Remote Access
Visibility is the first step toward security. Blumira can help you get that insight by integrating with your identity and access providers to detect and alert you on anomalous user logins or activity, including Duo Security, Okta, and Microsoft Active Directory.
Blumira integrates with VPNs, such as Cisco AnyConnect and other remote gateways, to analyze incoming traffic for threats. We can also protect against geo-impossible logins in real time so you can quickly respond to potential account takeovers.
Visibility & Prioritized Alerts
To support a remote workforce, organizations are turning to collaboration and productivity tools. Blumira integrates with Microsoft Office 365 and Google Workspace to help you track and monitor user logins and activity for faster, automated detection and actionable response to an increase in remote attacks.
Enable your distributed workforce to connect seamlessly and securely by gaining visibility and alerts with Blumira.
Support Cloud Migration
Blumira integrates with Microsoft Azure Event Hub to stream and centralize cloud security event logs and alerts. Blumira analyzes and correlates cloud logs to help identify indicators of attacker behavior and activity.
By prioritizing critical findings, Blumira also enables your team to respond automatically by blocking malicious sources, or by following guided security playbooks for remediation.
Detect Endpoint Risks
Centralize visibility of your endpoint protection tools with Blumira. Quickly detect and respond to device-related risk such as malicious code, potentially unwanted programs (PUP), and spyware files.
Blumira integrates with endpoint security providers such as VMware Carbon Black Endpoint Protection, Carbon Black Response, Carbon Black Managed Defense, Microsoft Windows Defender, Crowdstrike Falcon Endpoint Protection, and many others.
Blumira Customers in Their Own Words
Don’t just take our word for it. Hear what our customers are saying.
“I had no idea we were going to have onboarding sessions like this, it made me realize I made the right choice and shows your company really does care about their customers”
Eric Lester
Chief Engineer, Marshall Dekalb Electric Cooperative
“We don't have to spend time reviewing logs or looking for threats. Blumira allows our help desk folks to be effective security responders. The data behind the findings is there for review, but the system streamlines what is presented so we can address the threat quickly.”
David H.
SMB, G2 Review
“I told my director it’s like adding another employee, except much cheaper. That was a major driver — that Blumira was going to be taking care of the solution.”
Les Neely
System Admin, Upward Sports
Additional Resources for Remote Work Security
Find even more tips
Security How-To
6 min read
| July 9, 2020
How to Reduce Your Overall Attack Surface With Geoblocking
Read More
Security Alerts
5 min read
| June 23, 2020
RDP Risk: Ransomware Targets Manufacturing and Energy Plants
Read More
Security Alerts
10 min read
| May 26, 2020
Detecting RDP Attacks With Honeypots: Blumira Data Insights
Read MoreStop Threats Faster with Blumira
Experience a truly integrated security solution. Our platform provides automated threat detection, rapid response capabilities, and unified visibility across your entire environment. See how easy it is to protect your organization from evolving cyber threats.