- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
What are honeypots? A honeypot is a network device that either appears to contain or does actually contain vulnerable data intended to lure an attacker into accessing.
Whether a threat actor tries to log in to the interface, scans the device using a scanning tool, or attempts to access anything on the device such as a file, the alerting component will instantly inform your security team that something threatening is happening.
Considered a type of deception technology, a honeypot is an effective security measure that can be used to detect malicious activity such as lateral movement and potential bad actors on your network.
For example, every organization with internet connectivity is likely going to have a firewall in place, which can eliminate a lot of potential threats. But the reality is that hackers still find ways to get into an organization’s environment. Although network segmentation can be put into place as well, that doesn’t mean it’s preventing security threats from getting access to systems.
How Do Honeypots Work?
A honeypot is designed to replicate a real computer system. This can often be in the form of a login page similar to other systems, such as finance, IT, business applications and productivity. Honeypots often have built-in weaknesses to appeal to attackers — for example, basic passwords that are easy to crack.
When an attacker logs in – whether that actor is a hacker on the internet who gains access to a corporate environment or an internal actor who is trying to access one of these systems – the honeypot will detect that activity and immediately send an alert to IT or a security team. This now provides visibility to that team, who can determine if someone is doing something malicious within the organization’s environment
Once a threat actor accesses a system, the honeypot can track their behavior to uncover information about how they infiltrate systems and move laterally around the network.
Types of Honeypots
There are two main types of honeypot designs: production honeypots and research honeypots. Each are used differently:
Production honeypots, the most common type of honeypot, collect cybersecurity data within an organization’s production network with the goal of identifying active compromise and gathering data on cybercriminals, such as originating IP addresses, traffic frequency and more. A production honeypot acts as a decoy, sitting with the rest of legitimate systems and services that typically run in an environment.
Research honeypots generally gather more data than production honeypots, with the specific goal of collecting information about attackers’ techniques. While businesses typically use production honeypots, government and research organizations may use a research honeypot.
Within these two categories, there are also different types of honeypots for various levels of complexity. For example:
Pure honeypots are full-fledged servers that are configured to lure attackers by containing “sensitive information.” Software can monitor the connection between the honeypot and the rest of the network.
High-interaction honeypots also run a variety of real production systems designed to lure attackers. A research team may use high-interaction honeypots to learn the tools an attacker uses, even adapting to each incident to further trick the attacker — making these types of honeypots highly effective. However, high-interaction honeypots require a significant amount of time and effort to set up and maintain, which doesn’t make them a good fit for smaller or less experienced teams.
Low-interaction honeypots, on the other hand, are relatively easy to deploy because they are much more static environments. While a high-interaction honeypot essentially acts as a real system and gives attackers the opportunity to interact with a variety of services, a low-interaction honeypot gives attackers limited access to the operating system and only emulates a small amount of services and protocols. Therefore they are not as effective and as in-depth; instead, they are more useful for detecting less complex threats such as bots.
There are also other related honeypot technologies that a business can incorporate into their network security strategy:
- Honeynet. A network of honeypots and other deception techniques.
- Honeywall. Routes legitimate users to the production, or real network, and routes attackers to the honeynet.
- Honeytoken. A piece of data that is used to lure in an attacker, such as API keys, database entries, executable files, and keys to cloud resources (e.g. AWS key).
- Honeycred. A username or ID that is used to identify specific types of attacks on systems.
- Honeyport. A job that listens on specific TCP Ports. When a connection is established, it can either simply log or add a local firewall rule to block the host from further connections.
- Decoy databases monitor software vulnerabilities to detect attacks that exploit insecure system architecture — for example, SQL injection or privilege abuse.
- Malware honeypots detect malware attacks by impersonating known attack vectors.
- Spam honeypots, or spamtraps, emulate email addresses with the goal of identifying spammers.
Benefits of Honeypots
Honeypots were once an overlooked and underappreciated technology. After years of working with very loud security solutions, technology workers are under the impression that if a product isn’t producing constant noise, it’s not functioning.
The truth of the matter is, these honeypots are one of the most powerful internal detection mechanisms a network can have even if they only detect something once in a blue moon. A fully configured honeypot can help detect and stop cyberattacks.
Here are just a few benefits of honeypots:
They produce high-fidelity alerts. The beauty of a honeypot is that no matter what the alert is for, it’s either a legitimate attack, a user poking around on a network where they shouldn’t be, or a planned security test. This is not in any way a noisy device that generates a high volume of false positives – all notifications from a honeypot can and should be acted upon.
They make life harder for cybercriminals. Any win against an adversary is a good thing. Honeypots tend to frustrate attackers, waste time that could be spent doing actual damage, and discourage them from targeting your real network.
Disadvantages of Honeypots
There are a few risks and limitations of using honeypots, especially if they are improperly deployed. Here are a few:
They sometimes require hardware. Although honeypots are generally resource light, more complex honeypots, like high-interaction and research honeypots, need hardware to appear as realistic as possible. This hardware can be in the form of physical servers, virtual machines, or old computers.
Maintenance and setup can take time. Setting up and maintaining honeypots — again, especially high-interaction honeypots — can take significant time, effort and expertise.
Is a Honeypot Right For My Company?
In short, absolutely. Any added layer of security on a company network is an excellent choice. If that added layer of security is a honeypot, you have just strengthened your internal network detection tenfold. This virtual device is extremely lightweight while being a powerful form of intrusion detection.
For organizations with smaller and less experienced IT and security teams, Blumira offers an easy, low-effort method to deploy honeypots on a network. Blumira’s virtual honeypots only require a sensor and can be implemented with a few clicks.
Honeypots were once an overlooked and under-appreciated technology. After years of working with very loud security solutions, technology workers are under the impression that if a product isn’t producing constant noise, it’s not functioning.
The truth of the matter is, these honeypots are one of the most powerful internal detection mechanisms a network can have even if they only detect something once in a blue moon. A fully configured honeypot can help detect and stop cyberattacks.
Here are just a few benefits of honeypots:
They produce high-fidelity alerts. The beauty of a honeypot is that no matter what the alert is for, it’s either a legitimate attack, a user poking around on a network where they shouldn’t be, or a planned security test. This is not in any way a noisy device that generates a high volume of false positives – all notifications from a honeypot can and should be acted upon.
They add another layer of security. Any added layer of security on a company network is an excellent choice. If that added layer of security is a honeypot, you have just strengthened your internal network detection tenfold. This virtual device is extremely lightweight while being a powerful form of an intrusion detection system.
They make life harder for cybercriminals. Any win against an adversary is a good thing. Honeypots tend to frustrate attackers, waste time that could be spent doing actual damage, and discourage them from targeting your real network.
How To Set Up a Honeypot
Blumira makes it easy to deploy and manage honeypots with low effort, allowing for early detection of attacks and threats.
Setting up a honeypot on the Blumira sensor is quick and easy. We have developed a honeypot module on our sensors which allows you to create a honeypot at the sensor IP address.
Once the Blumira sensor is created, you can choose to add the honeypot module at the click of a button. Then you will be automatically alerted when someone scans or accesses the sensor IP in any way.
See what you can detect with Blumira’s honeypots and how you can test a Blumira honeypot for lateral movement.
Within the Blumira platform, we provide actionable playbooks, also called workflows, that enable anyone in IT to easily respond to a detected threat (no security experience required). Above is an example of a detection of an attacker accessing certain files hosted on a Blumira honeypot.
In these playbooks, we offer different automated options to block the source IP address and effectively protect against any access attempts from this source.
Additional Honeypot Resources
- Detecting RDP Attacks With Honeypots. See our honeypot data on remote access attack trends against RDP since the start of the pandemic and rise in remote work, and get advice on how to protect your organization against remote attacks.
- A Guide To Cybersecurity Deception Techniques. Using “low-hanging fruit” cybersecurity deception techniques to entice an attacker that has already infiltrated an environment will offer even more opportunities for early detection — and in turn, will help to increase your organization’s defensive strategy.
Deploy a Honeypot Today
Try out Blumira's automated detection & response platform for free and deploy a honeypot in just a few hours.
Have questions around honeypots or want to learn more about Blumira? We're happy to help.
Matthew Warner
Matthew Warner is Chief Technology Officer (CTO) and co-founder of Blumira. Matt brings nearly two decades of IT and cybersecurity experience to his leadership position, and a genuine passion for cybersecurity education. Prior to founding Blumira, he was Director of Security Services at NetWorks Group, a managed...
More from the blog
View All Posts
Security Trends and Info
9 min read
| May 28, 2020
Seeking a SIEM Alternative? Choose Automation
Read More
Security Alerts
9 min read
| June 15, 2020
Top Security Threats: Lateral Movement
Read More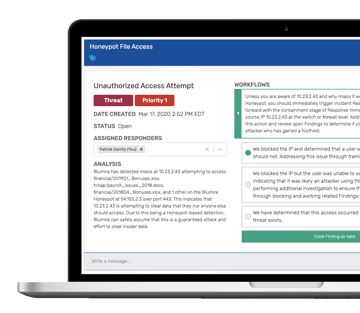
Security How-To
4 min read
| April 20, 2020
Hands in the Honeypot: Detecting Real Security Threats
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.



