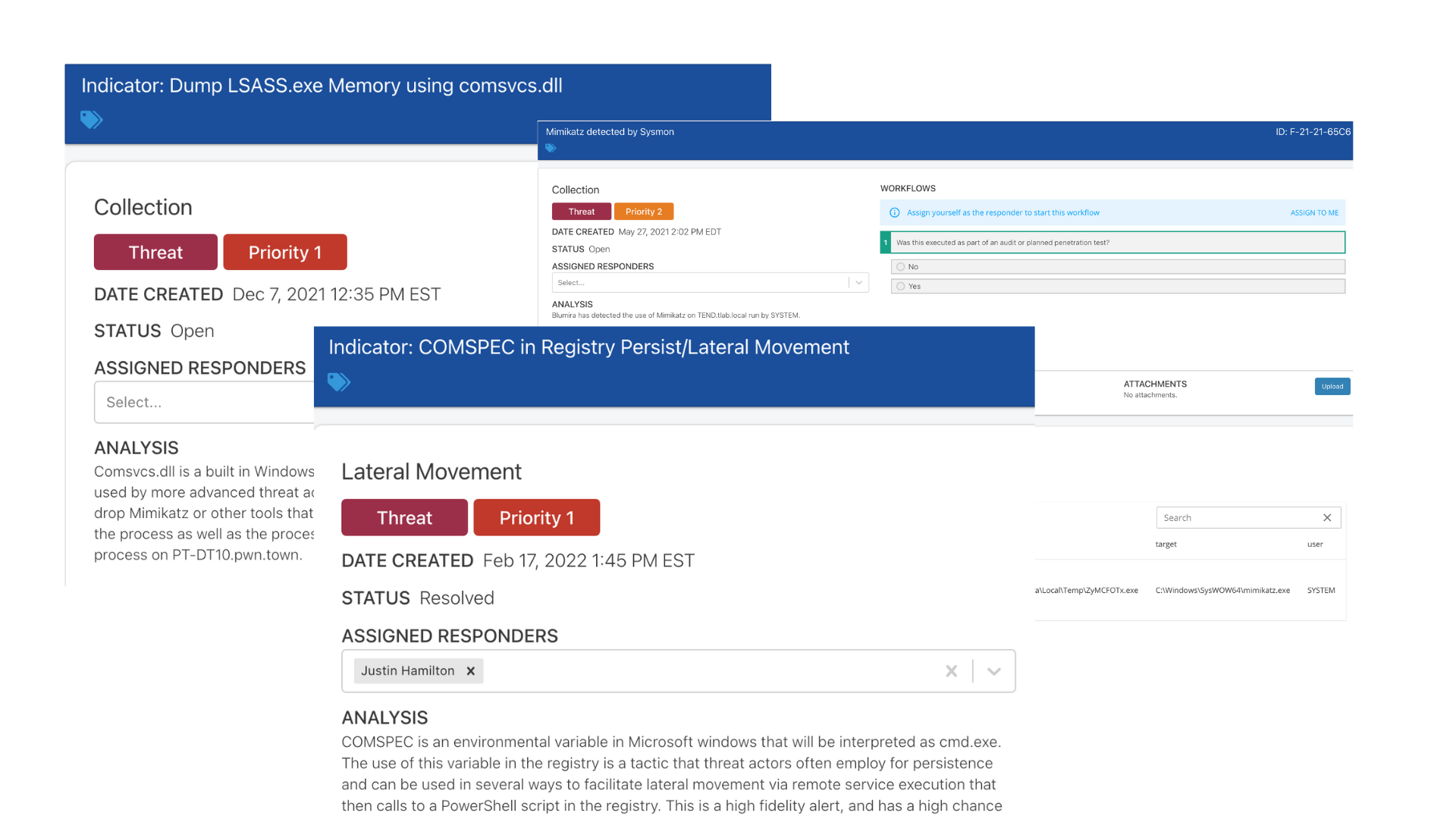
Real-World Examples of Detecting Attacks with Sysmon
Learn how Sysmon's detailed logging of system, process and command line activity reveals threats that bypass standard Windows logging.
Read MoreSocial Engineering: The Human Element in Cybersecurity
Learn how the NIST framework provides guidance for avoiding social engineering attacks on your organization.
Read MoreCatch Threats at Every Turn with Blumira SIEM
Blumira SIEM detects threats at every stage, from reconnaissance to impact, and reduces alert noise through automation.
Read More4 Cyberattacks on State/Local Government and What We Can Learn from Them
Overview of 4 recent government cyberattacks supplemented with analysis of the respective situations, and lessons learned from each instance.
Read MoreThe Hedgehog Defense – Default Apps
This small change can prevent malware from running in your network and it's not related to any security products!
Read MoreSo you think you need a SOC?
For most SMBs, building an in-house SOC is complex and costly. Automated detection and response from Blumira is what you need.
Read MoreBlumira Joins MES IT Leadership Network: Better Supporting Our Midsize Customers
Blumira recently joined the MES IT Leadership Network. This online community helps IT professionals network with peers and share best practices.
Read MoreWhy You Should Migrate From On-Premise Exchange
Migrating from on-prem exchange can be a daunting task. See why it's important based on recent attacks, vulnerabilities, and best practices.
Read MoreIncident Response Steps for State and Local Governments
Learn key incident response steps and NIST incident response strategies for enhancing government cybersecurity effectively.
Read More3 Ways the State and Local Cybersecurity Improvement Act Helps Government Cybersecurity Teams
Learn about the recently passed State and Local Cybersecurity Improvement Act and how your organization should respond.
Read More