- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Data is crucial to nearly every company in today’s digital age, which means that when data loss occurs, it’s a major problem.
What is Data Exfiltration?
Exfiltrating data is when an adversary is trying to steal data, typically falling in the latter stages of a cyber attack (known as the ‘cyber kill chain’). Data exfiltration also comes later in the attacker tactics on the MITRE ATT&CK Framework after discovery, lateral movement, collection, etc.
The concept of data leaving an organization’s network has been used to help identify a data breach or ransomware attack. However, if data is leaving your network, it means you’ve definitely had an intrusion, and it indicates that earlier protective measures prior to exfiltration failed to detect or prevent against stolen data.
How a Data Exfiltration Attack Happens
Data exfiltration generally happens through outsider attacks or insider threats. Both can have devastating effects on an organization, so IT and security teams should be aware of data exfiltration prevention methods, as well as an incident response plan.
Outsider Attacks
Outsider attacks generally start with initial attack vectors such as phishing attacks or malware injection. Once a threat actor has gained access into the system, they will typically move laterally throughout the network and use a variety of techniques to exfiltrate data.
The different techniques used to for data transfer include sending it over their command and control channel, and packaging, compressing and encrypting data prior to exfiltration in order to both minimize the amount of data as well as hide the information being sent over the network.
What is command and control? Also known as C&C or C2 servers, these are used by a malicious actor to send commands to systems after they’ve compromised them in order to send back stolen data. MITRE lists out different procedure examples (known backdoors and techniques used by each tool) for sending data over command and control channels.
By establishing C2 communications through DNS, HTTP and FTP protocols, attackers can also send commands to steal data or spread malware throughout several different compromised machines in a botnet. They can initiate distributed denial of service (DDoS) attacks that overwhelm and disrupt internet services by flooding them with internet traffic, such as in the Mirai botnet attack of 2016 that infected many unprotected Internet of Things (IoT) devices.
Insider Threats
Examples of insider threats include disgruntled employees with physical access to the organization’s environment. Many malicious insiders steal the organization’s valuable data to then sell to cybercriminals.
Indicators of a Data Exfiltration Attack
At Blumira, we regularly detect data exfiltration attacks. Here are some ways we’ve identified the attacks:
Outbound connections to an external source via a generic network protocol. In one example of Blumira’s detections, we found that there was a 50GB+ outbound connection to an external source via a generic network protocol, which can indicate either a legitimate business-related connection or potential data exfiltration.
In the workflow steps, we recommend that the source machine is taken offline immediately, if the outbound connection of 50GB+ of data isn’t correlated to a typical business operation, such as a large backup process.
Large flow to unexpected IP addresses. In another example of detected exfiltration, Blumira has identified a specific user attempting to transfer data to a public IP address that they/no one else in the organization had never connected to previously, indicating potential data theft in progress.
In the workflow steps, Blumira recommends temporarily stopping access for the user by locking out their account, disabling their Active Directory account ID, and killing active sessions that allow the outbound connection, such as virtual private networks (VPNs).
We also recommend investigating access control lists (ACLs) associated with the user’s access within the environment that data could be stolen. You can do this by using the Windows AccessEnum tool that can allow you to get a view of your file system and Registry security settings to help identify security holes and lock down permissions, according to Microsoft.
Major spikes in anomalous outbound web traffic. Other rules that Blumira uses to detect potential data exfiltration include a major spike in anomalous outbound web traffic (such as 1000%), and allowed outbound or inbound evasive/malicious encrypted-tunnel software.
Mass download. A user downloading or accessing a massive amount of files in a short span of time could be a legitimate action — or it could be a sign of data exfiltration. You can detect mass downloads in Microsoft 365 with Blumira.
How To Prevent Data Exfiltration
Use cybersecurity technology that can detect C2. Every organization has at least some capacity to detect C2 in a classic network architecture, whether it’s with next-generation firewalls, intrusion prevention systems (IPS), email security solutions or proxies, etc.
Pairing this with threat intelligence is useful to help enrich and narrow the scope of detection. Since data must pass through a designed egress point in order for it to leave the network, typically a next-generation firewall (NGFW) or network IPS with visibility into network traffic protocols can help detect exfiltration. They can include signature-based antivirus capabilities that are useful for C2 detection.
However, quality C2 detection doesn’t just rely on signatures. Based on the design of a network, attackers must use whatever egress channels are available to them for C2 or data exfiltration – these particular “choke points” are advantageous for defense as they make attackers predictable. In the military, a choke point is a land feature (such as a narrow strait connecting bodies of water) that an armed force must pass, making it more difficult for passage and decreasing their combat power.
Implement data loss prevention (DLP) solutions. DLP software enables admins to control the data that users can transfer, using rules to classify and protect sensitive information. For example, DLP software may prevent an employee from forwarding a business email outside of the corporate domain.
Use a SIEM. Security information and event management (SIEM) collects and converges data from different parts of your IT environment, such as firewall traffic, endpoint data, and more. SIEMs are used for real-time security event analysis to help with investigation, early threat detection and incident response.
Blumira’s threat detections bring together threat intelligence, geo-specific data and other attack patterns such as outbound data volume in order to identify data exfiltration in progress. We also enable security and IT teams to quickly respond to detections through our platform with guided pre-built playbooks that walk you through different remediation steps.

Detect Data Exfiltration with Blumira
Blumira is ready out of the box to detect suspicious activity that is indicative of data exfiltration.
Here what you get to protect M365:
- Security monitoring for Microsoft 365, with unlimited users and data (no special licensing required)
- Easy, guided setup with Cloud Connectors that takes only minutes
- Detection rules automatically rolled out to your account, fine-tuned to filter out the noise
- Summary dashboard of key findings and security reports
- Playbooks with each finding to guide you through response steps, written by security operations experts
- One week of log data retention – upgrade for up to one year
Sign up for your trial account to take advantage of these Microsoft 365 detections and more.
In addition to monitoring Microsoft 365, organizations looking to strengthen their overall security posture should start with understanding their external attack surface. After all, preventing unauthorized access to your domain is the first step in protecting against data exfiltration.
Try Blumira's free Domain Security Assessment tool. It automatically scans your publicly accessible assets and provides actionable insights about security gaps - helping you build a stronger first line of defense against data theft.
Thu Pham
Thu has over 15 years of experience in the information security and technology industries. Prior to joining Blumira, she held both content and product marketing roles at Duo Security, leading go-to-market (GTM) and messaging for the portfolio solution Cisco Zero Trust. She holds a bachelor of science degree in...
More from the blog
View All Posts
Security How-To
9 min read
| March 11, 2022
Analyzing MITRE’s Top Observed Attacker Techniques
Read More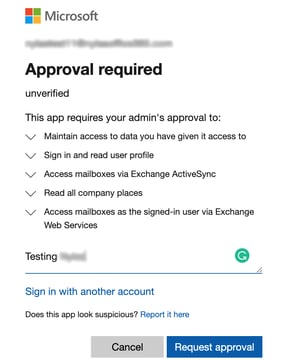
Blog
7 min read
| December 5, 2024
Protect Your Microsoft 365 Ecosystem from Third-Party App Risks
Read More
Security How-To
9 min read
| February 3, 2022
Email Forwarding Security Risk (And How to Detect)
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.