- Product
Kindling
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
One of the most basic and best security practices includes limiting which geographic regions you allow to connect to your environment – also referred to as geoblocking. It’s extremely effective to track or control inbound connections using firewall policies, IDS/IPS (Intrusion Detection and Protection Systems), and authentication attempts from certain countries you don’t typically do business in.
Monitor Connections from Certain Countries
How can you start tracking those? Next-generation firewalls (NGFW), IPS and other network security technologies generate a lot of metadata for each logged connection to your systems. This additional metadata can allow you to create more granular firewall rules to detect potential threats.
To defend your network, adopting a Positive Security model can help by denying most connections and only allowing the things which are required on your network, also known as a allowlist model. This requires defining the characteristics of all known good traffic connections, applications or endpoints on your network.
According to Blumira’s Director of Security, Mike Behrmann, it’s common for NGFWs and IPSes to geographically pinpoint an Internal Protocol (IP) address in one or more logfields (such as City: Beijing; Country Code: CN) via DNS registrant information.
A U.S. company with a customer base primarily located in one specific region, like the Midwest, may not want to allow inbound connections from countries with either lax cybersecurity laws or those that are known for state-sponsored advanced persistent threats (APTs) in order to shrink their risk profile.
Reducing Your Attack Surface With Blumira’s Detections
By leveraging firewall and IPS logs, Blumira is able to enrich our pre-built threat detection conditions with contextual data to better inform our security findings. Our security team creates customized threat detection rules for specific clients based on the industry. We can also create rules based on their request to help monitor and protect their publicly exposed assets.
Some of the relevant detections that come built into Blumira’s platform include:
Fortigate SSL VPN Anomalous Access Attempt – This finding can identify password spraying attacks, the act of trying a few authentications against many users. Attackers use this method to avoid most brute-force detections or triggering lockouts, which can call attention to their actions. In this case, an attack has been identified against the Fortigate SSL VPN login. An attacker is likely attempting to gain access through credential reuse or other credential attacks.
RDP Connection from Public IP – By detecting any public IPs connecting to your network via RDP, Blumira can alert you to potentially malicious attempts to gain access and install malware. Ransomware actors routinely use publicly accessible RDP services to gain an initial foothold in victim networks. RDP connections should be made via VPNs and never left open to the internet.
Outlook Web Access Anomalous Access Attempts – This detection finds a number of anomalous access attempts against your Outlook Web Access server, which can indicate an attacker attempting to access your environment. Blumira recommends blocking the source IP immediately and resetting passwords for targeted users.
External to Internal Scanning – By detecting scanning, you can protect against both internal and external attackers that may be performing reconnaissance on your network, searching for vulnerable areas to attack and move laterally throughout your environment. Blumira can detect any internal port scanning tools (indicators of early attack stage), multiple internal reconnaissance connections over a short period of time (target enumeration), as well as any honeypots being actively scanned.
Detect Geo-Impossible Anomalous Connections
Another way to reduce your overall attack surface is by monitoring the time and location of access attempts to detect potentially anomalous user activity. If a user is connecting from Los Angeles four hours after originally connecting from New York City, it’s possible that their account may have been compromised through stolen credentials or other identity attack.
In the above finding, we detected an authentication attempt from an unlikely location – which could indicate that the user’s credentials had been stolen or compromised, and an attacker is attempting to access your systems.
To help you with the next steps of incident response, we provide a workflow with recommendations on mitigation, including immediately disabling the user within your Duo Security two-factor authentication administrative panel. Then, confirm with the user their travel plans, or reset their credentials.
While this level of threat response is automated to help you quickly contain threats in near real-time, Blumira’s security team can also provide additional assistance or answer your questions as needed.
Additional Resources
Automating Detection and Response With Cisco Firewalls & VPN – By easily integrating Blumira’s platform with Cisco ASA & FTD firewalls and AnyConnect VPN, you can start detecting threats and misconfigurations today.
Palo Alto Next-Generation Firewalls Integration: Automated Threat Detection & Response – By collecting and parsing firewall logs, Blumira’s automated platform can detect indicators of threats and help you respond to them quickly.
Thu Pham
Thu has over 15 years of experience in the information security and technology industries. Prior to joining Blumira, she held both content and product marketing roles at Duo Security, leading go-to-market (GTM) and messaging for the portfolio solution Cisco Zero Trust. She holds a bachelor of science degree in...
More from the blog
View All Posts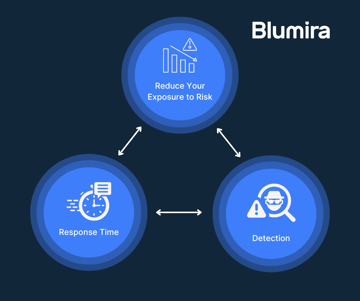
Security Trends and Info
2 min read
| May 20, 2020
Replace Your SIEM With Automated Detection & Response
Read More
Security How-To
10 min read
| April 23, 2020
Replace Your SIEM: Traditional vs. Modern SIEM
Read More
Security Trends and Info
3 min read
| May 14, 2020
What is a Traditional SIEM?
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.
