- Product
Product Overview
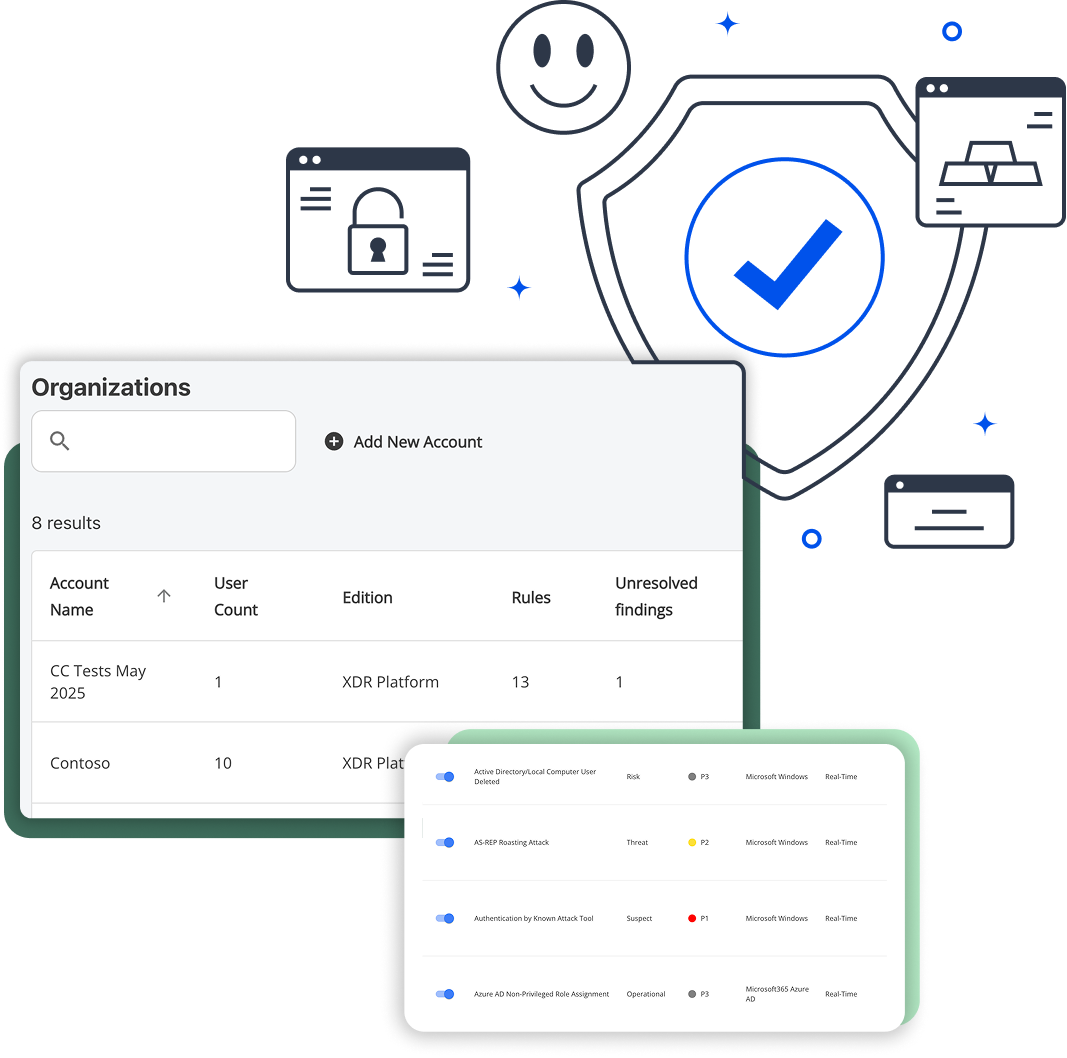
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
Splunk is the most capable SIEM on the market. It is also the most expensive to own, the hardest to staff, and the most likely to be underutilized by teams that lack dedicated Splunk administrators. According to Glassdoor (2025), the average Splunk administrator earns $132,737 per year, and most organizations need at least one full-time admin to keep the platform running. If your organization is paying for Splunk but only using a fraction of what it can do, the problem is not Splunk. The problem is the fit between an enterprise tool and a non-enterprise team.
This page is for IT leaders evaluating whether Splunk is still the right SIEM for their organization. It covers real costs, honest trade-offs, and what to look for if you decide to move on.
The Real Cost of Splunk
Splunk licensing is only one line item. The total cost of ownership includes staffing, training, professional services, and annual price escalation. Most mid-market organizations discover that the people cost exceeds the license cost within the first year. A Splunk administrator earns an average of $132,737 per year (Glassdoor, 2025). Add one or two SIEM analysts at $75,000 to $130,000 each (BLS, May 2024; ZipRecruiter, 2025), and staffing alone can exceed $250,000 annually before you pay for a single license. For a 200-person organization, three-year Splunk TCO typically falls between $750,000 and $1,500,000.
The table below reflects mid-market deployments (100 to 500 employees). Enterprise deployments with dedicated SOC teams often exceed the upper range. Salary data comes from the U.S. Bureau of Labor Statistics Occupational Outlook Handbook (May 2024) and Glassdoor (2025). Splunk pricing ranges come from Splunk's published pricing tiers and third-party analysis by Uptrace (2025).
| Cost Category | Annual Range | Source |
| Splunk license (annual, ingest-based) | $36,500 (10 GB/day) to $400,000+ (500 GB/day) | Uptrace Guide to Splunk Pricing (2025); Splunk Ingest Pricing Page |
| Splunk administrator (1 FTE) | $103,000 to $173,000 | Glassdoor Splunk Administrator Salary (2025), 25th-75th percentile |
| SIEM analyst(s), 1-2 FTEs | $75,000 to $130,000 each | BLS Occupational Outlook Handbook (May 2024); ZipRecruiter SIEM Analyst Salary (2025) |
| Professional services (deployment) | $15,000 to $150,000 one-time | UnderDefense Splunk Pricing Guide (2025); Uptrace (2025) |
| Training and certification | $5,000 to $15,000/year per admin | Splunk Education Pricing Page (2025); PearsonVUE exam fees |
| Annual renewal escalation | 9% per year on 1-year terms | Splunk Platform Pricing FAQ (2025) |
| 3-year TCO (200-person org, mid-range) | $750,000 to $1,500,000 | Sum of above, mid-range estimates |
Methodology note:
Splunk prices licenses as annual subscriptions based on daily ingest volume (GB/day). Unit price per GB decreases at higher volumes, but total cost grows significantly. The license ranges above reflect Splunk Cloud ingest pricing for small business (10 GB/day) through enterprise (500 GB/day) tiers, as documented by Uptrace (2025). Splunk does not publish specific per-GB dollar rates publicly. Professional services estimates come from third-party Splunk implementation partners. A note on first-year cost overruns: Uptrace (2025) and UnderDefense (2025) both report that companies often face 40 to 60 percent cost overruns in their first year of Splunk. The most common cause is underestimating daily ingest volume, which pushes organizations into a higher license tier mid-contract.
Who Splunk Is Built For vs. Who Is Using It
Splunk was designed for large security operations centers. Many of the organizations running it today do not have one. This mismatch creates frustration on both sides. Splunk support tells you to "tune your rules," but you did not write the rules. Your team inherited a deployment they were never trained to operate.
| Splunk is ideal when you have... | You might need something different when... |
| A dedicated SOC with 3 or more analysts | Your IT team handles security alongside everything else |
| SPL expertise on staff | Nobody on your team knows SPL |
| A $300,000+ annual security tool budget | Your total security tooling budget is under $100,000 per year |
| Custom threat models requiring bespoke correlation rules | You need pre-built detections that work without rule writing |
| A team that lives in dashboards 8 hours a day | You have 15 minutes a day for security monitoring |
| Complex multi-stage investigations across dozens of data sources | You need automated threat detection with guided and automated response actions |
| Budget for ongoing Splunk training and certification | You need a platform your team can operate without specialized training |
7 Things to Look For in a Splunk Alternative
Not every Splunk replacement will solve the problems that made you start looking. Some alternatives replicate the same complexity under a different brand. Here is what to evaluate.
1. No proprietary query language
2. Pre-built detections that work on day one
3. Flat-rate pricing without data volume surprises
4. Deployment in hours, not months
5. Compliance reporting built in
6. Automated response, not just alerting
7. Runs on your existing team
When Blumira is not the answer: If you need in-platform query customization (writing your own detection logic in a query language like SPL), NDR (network detection and response), or an all-in-one platform with built-in vulnerability management, Blumira is not the right fit. Consider Elastic Security or Microsoft Sentinel for query-level control, or tools like Arctic Wolf for bundled vulnerability scanning. Blumira partners with customers on custom detection asks rather than exposing a raw query interface. That is a deliberate design choice, not a limitation.
What You Give Up When You Leave Splunk
Switching from Splunk means walking away from more than a license. The ecosystem lock-in is real, and pretending otherwise does not help anyone make a good decision. Splunk deployments accumulate years of custom dashboards, saved SPL searches, Splunkbase app dependencies, and institutional knowledge embedded in correlation rules and threshold configurations. For heavily customized environments, migration is a multi-month project. For lightly customized deployments running mostly default detections, the switching cost is low and the operational savings begin immediately.
Here is what does not migrate:
Custom dashboards built over years. If your team spent months building Splunk dashboards, those visualizations do not port to another platform. You will need to rebuild reporting in your new tool.
SPL queries your team has refined. Any saved searches, alerts, and correlation rules written in SPL are specific to Splunk. They do not translate to other query languages or detection engines.
Splunkbase apps and integrations. The Splunk marketplace has thousands of apps. If you depend on specific Splunkbase apps for endpoint visibility, cloud integrations, or vendor-specific log parsing, verify that your replacement covers those data sources natively.
Institutional knowledge embedded in your configuration. Your Splunk deployment encodes decisions made over years. Which logs matter, which alerts are tuned, which thresholds were set. This context lives in your Splunk instance, not in documentation.
These are real switching costs. If your Splunk deployment is heavily customized with hundreds of active rules and dozens of Splunkbase apps, a rapid migration is not realistic and should not be rushed. But if you are running mostly default detections with a few custom dashboards (which is true for the majority of mid-market Splunk deployments), the switching cost is low and the savings are immediate.
The honest question to ask: in the last 90 days, how many of your custom Splunk rules actually fired? Most teams discover the majority of their custom content has not triggered recently.
How Blumira Compares to Splunk
This comparison is designed to be fair to both platforms. Splunk is the more customizable tool. Blumira is the more practical tool for teams without dedicated security staff. Both statements can be true. Splunk deploys in 6 to 12 months for most mid-market organizations. Blumira averages 0.41 months (roughly 12 days), which is 5.17 times faster than the 16-vendor SIEM average of 2.12 months, according to G2 Winter 2022 deployment data. On daily operations, Splunk typically requires 2 to 3 full-time staff. Blumira is designed for 15 minutes per day by an existing IT team.
| Dimension | Splunk Enterprise | Blumira |
| Deployment time | 6 to 12 months typical | 4 hours average (5.17x faster than 16-vendor average per G2 Winter 2022) |
| Daily management | 2 to 3 FTEs (Splunk admin plus analysts) | 15 minutes per day, existing IT team |
| Query language | SPL (proprietary, steep learning curve, deep flexibility) | None required for daily operations |
| Detection rules | Build and maintain your own (maximum customization) | Pre-built, expert-managed, updated continuously |
| Response capability | Manual investigation or custom scripting (SOAR is a separate add-on) | Built-in playbooks with guided response steps and automated response actions for common threats |
| Pricing model | Per-GB ingest (annual license tiers, variable with volume) | Flat-rate per employee ($12 to $21/month per Blumira pricing page) |
| Compliance reporting | Custom dashboards or third-party add-ons | Built-in reports for SOC 2, HIPAA, PCI, CMMC, NIST |
| App ecosystem | Splunkbase marketplace with thousands of apps (major strength) | Native integrations for common cloud, identity, endpoint, and network sources |
| Market maturity | 20+ years, established as the enterprise standard | Purpose-built for mid-market IT teams since founding |
| Best fit | Large SOC teams with SPL expertise and budget for dedicated staff | IT teams managing security alongside other responsibilities, with 24/7 SecOps support for critical incidents |
Splunk's strengths are real. Its query language (SPL) is the most flexible in the industry. Its app ecosystem is unmatched. For organizations with a funded SOC and trained analysts, Splunk remains a strong choice. The question is whether your organization has the team to use those strengths. If you do not, the practical paths are a self-service SIEM with 24/7 SecOps support (like Blumira), working through an MSP that manages security tooling on your behalf, or a fully managed detection and response (MDR) service where you hand off security operations entirely.
Switching from Splunk: A Practical Process
Migration does not have to be a six-month project. The timeline depends on how customized your Splunk deployment actually is. For a lightly customized deployment (default rules, a few custom dashboards), expect one to two weeks. For a heavily customized environment, plan for one to three months of parallel operation.

Step 1: Inventory What You Are Actually Using
Pull your Splunk rule list. Check which rules fired in the last 90 days. Export your dashboard usage stats. Most teams discover that the majority of their custom content has not triggered an alert in months. The rules that matter are the ones that fire. Everything else is inherited complexity.

Step 2: Map Your Log Sources
List every data source currently feeding Splunk: cloud applications (Microsoft 365, Google Workspace), identity providers (Azure AD, Okta), endpoint agents (EDR tools), firewalls, and network devices. Check which log sources have native connectors in your replacement platform. For Blumira, common integrations include cloud, on-prem, and API-connected environments across major vendors.

Step 3: Run Parallel for One to Two Weeks
Deploy your replacement alongside Splunk. Send the same log data to both platforms simultaneously. Compare detection coverage on identical events. This parallel period validates that your new SIEM catches what Splunk catches (and shows where the new platform's pre-built detections cover gaps your custom rules never addressed). With a cloud-native SIEM, parallel deployment takes hours to set up, not months.

Step 4: Cut Over and Decommission
Once parallel operation confirms coverage, redirect log sources to your new platform. Export any Splunk data you need for compliance retention requirements. Cancel the Splunk renewal before the next billing cycle. Keep your SPL query library archived (not deleted) in case you need to reference detection logic later.
Realistic timeline: Blumira deploys in an average of 0.41 months (roughly 12 days), compared to the 16-vendor SIEM average of 2.12 months, according to G2 Winter 2022 deployment data. Your total migration, including parallel operation, typically takes two to four weeks for mid-market organizations.
Frequently Asked Questions
How much does Splunk actually cost per year?
For mid-market organizations (100 to 500 employees), the total cost of ownership ranges from $250,000 to $500,000 per year when you include licensing, staffing, training, and professional services. License costs alone range from $36,500/year for 10 GB/day ingest to over $400,000/year for 500 GB/day, based on Uptrace analysis of Splunk pricing (2025). Staffing is typically the largest cost component.
Can I replace Splunk without losing threat detection coverage?
Yes, for most mid-market deployments. The majority of custom Splunk rules duplicate what pre-built detections in modern SIEM platforms already cover. Run a parallel deployment to validate coverage before cutting over. The rules that matter are the ones that fire. If a custom rule has not triggered in 90 days, it is not providing value.
How long does it take to switch from Splunk to another SIEM?
It depends on your level of customization. Organizations running mostly default Splunk configurations can switch in one to two weeks. Heavily customized deployments with hundreds of active SPL rules and dozens of Splunkbase apps should plan for one to three months of parallel operation.
Is Blumira as customizable as Splunk?
No. Splunk is the most customizable SIEM available. Its query language (SPL) allows virtually unlimited in-platform customization, its app marketplace has thousands of integrations, and its data handling scales to petabytes. Blumira trades that customizability for simplicity, speed, automated response, 24/7 SecOps support, and lower total cost of ownership. If you need SPL-level control and have the team to use it, keep Splunk.
What is the cheapest Splunk alternative?
It depends on the pricing model. Per-GB alternatives may appear less expensive until data volume spikes. Flat-rate alternatives like Blumira offer predictable pricing at $12 to $21 per employee per month (per Blumira's published pricing page, 2026), which includes all log ingestion without per-GB charges. For a 200-person organization, that is $28,800 to $50,400 per year.
Does Splunk have a free tier?
Splunk Free allows 500 MB per day of ingestion with limited features and no alerting. It is suitable for lab environments but not production security monitoring. Blumira offers a free edition with core SIEM capabilities for up to three cloud connectors.
What compliance frameworks does Blumira support?
Blumira includes built-in reporting for SOC 2, HIPAA, PCI DSS, CMMC, CJIS, and NIST frameworks. Splunk can support these frameworks through custom dashboards or third-party apps, but compliance reporting requires configuration and ongoing maintenance by your team.
Can Blumira ingest the same log sources as Splunk?
Blumira supports native integrations for the most common enterprise log sources: Microsoft 365, Google Workspace, Azure AD, Okta, CrowdStrike, SentinelOne, SonicWall, Fortinet, Palo Alto, and others. Splunk supports a broader range of sources through Splunkbase apps. If you rely on a niche or proprietary log source, verify native support with both vendors before committing.
See How Blumira Compares to Your Splunk Deployment
The fastest way to evaluate a Splunk alternative is to run it alongside Splunk on the same data. Blumira deploys in under an hour. Connect your existing log sources, compare detections side by side for a week, and decide based on what you see.
Related Resources
- QRadar Alternative (IBM QRadar EOL migration options)
- Running a SIEM Without a SOC (how IT teams manage SIEM without dedicated analysts)
- Cyber Insurance SIEM Requirements (what underwriters expect for security monitoring)
- The Real Cost of Running a SIEM (full TCO analysis across SIEM platforms)
- SIEM Migration Guide (step-by-step process for switching SIEM providers)
- Splunk vs. Blumira (direct feature comparison)
- Hidden Costs of SIEM: Splunk vs. Blumira (detailed cost comparison)
- How Much Is Your SIEM Costing You? (broader SIEM cost breakdown)
