Top 10 Security Detections of 2020
See our recap of last year's top security detections, and learn how you can protect, detect and respond to keep your organization safe.
Read MoreThreat Detection & Response Maturity: Modern Cybersecurity Practices, Part 3
Our interview with Pascal Ackerman covers the challenges with detecting attacker intrusions, continuous monitoring and getting value out of a SIEM solution.
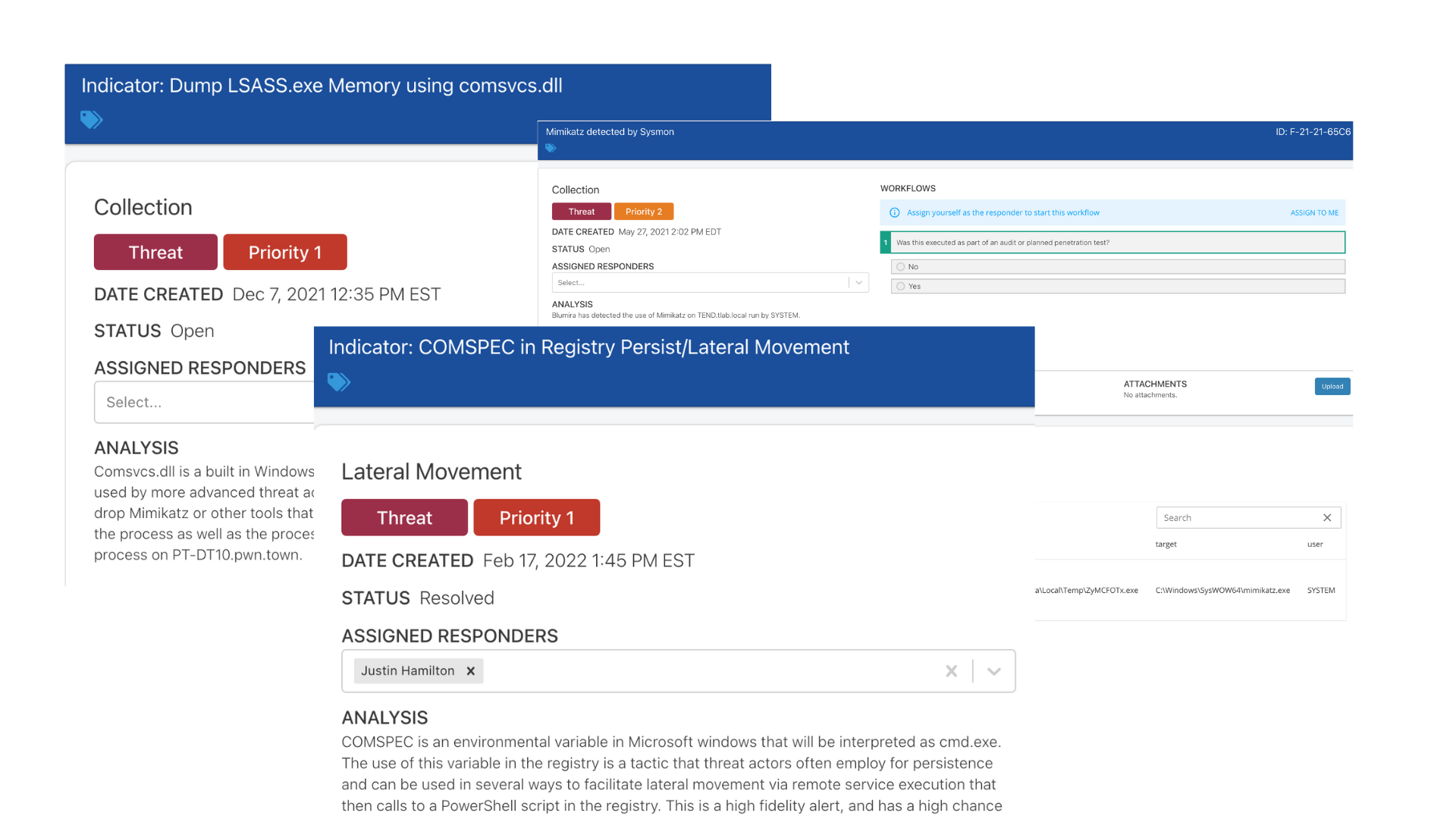
Read MoreTop Security Threats: Lateral Movement
Lateral movement can be difficult to detect internally and reliably - learn about how to detect lateral movement tactics used by attackers with Blumira.
Read MoreTop Security Threats: Detecting Ransomware Tactics
Ransomware is targeting SMBs, using new tactics to evade detection. Here's how to effectively detect on risky activity and protect against infection.
Read MoreHow To Detect Data Exfiltration
To prevent data exfiltration, it's important to know the signs. Here's what to look out for to detect data exfiltration.
Read MoreTop Five Security Threats You Should Be Detecting
A basic primer on some of the top attacker techniques you might not be catching - from ransomware to brute-force attacks - based on Blumira detections.
Read MoreBlumira’s Threat Hunting Playbook
Blumira automates threat hunting to save clients countless hours of security analysis - here's our playbook for efficiently finding network threats.
Read MoreHow To Choose a SIEM For Small Business
Small businesses often struggle to find a SIEM that's not overly complex and expensive. Here's what small teams can prioritize to find the right fit.
Read MoreThreat Analysis: PowerShell Malicious Activity
An in-depth breakdown of an analysis of a real threat detected by Blumira and our recommended security mitigations.
Read MoreHands in the Honeypot: Detecting Real Security Threats
What is a honeypot? Here's how to set up a honeypot with Blumira to help you detect and stop network intruders.
Read More