Detect and Protect Against Emotet Malware
Emotet can lead to ransomware, and enable attackers to move laterally throughout your network to steal data. Here's how to detect and defend against it.
Read MoreWhat You Need to Know About SigRed: Windows DNS Vulnerability (CVE-2020-1350)
Mitigate the SigRed Windows DNS vulnerability (CVE-2020-1350) with Blumira's detection & response. Protect your Windows DNS servers from potential attacks.
Read MoreWhat You Need to Know About the Severe F5 BIG-IP Vulnerability
This 10/10 critical F5 vulnerability can result in complete system compromise. See how it works, who's affected and how to mitigate.
Read MoreRDP Risk: Ransomware Targets Manufacturing and Energy Plants
Ransomware targeting industrial control systems shut down major manufacturing and energy plants - detecting RDP risk is key to stop infection.
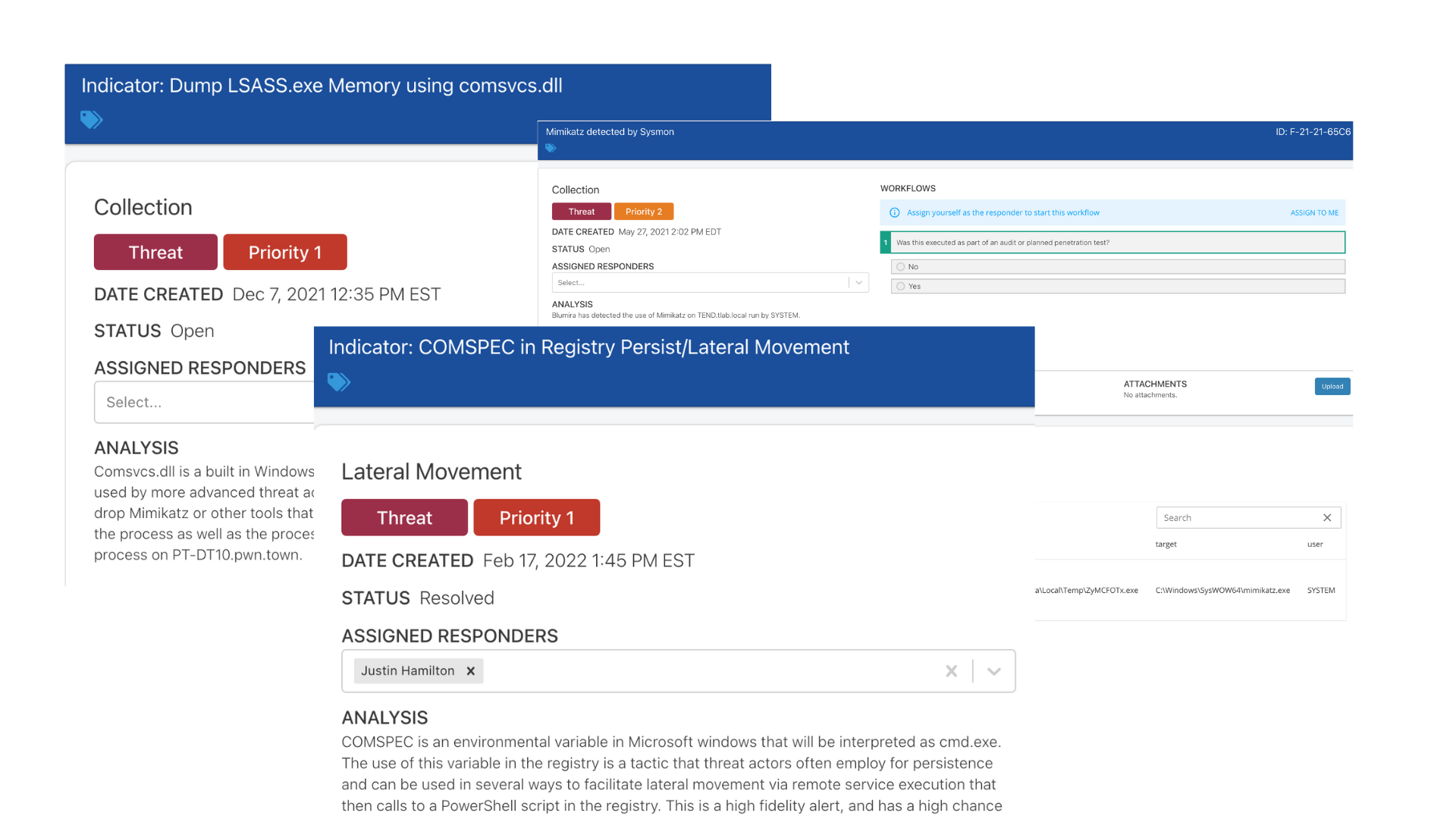
Read MoreTop Security Threats: Lateral Movement
Lateral movement can be difficult to detect internally and reliably - learn about how to detect lateral movement tactics used by attackers with Blumira.
Read MoreCommon Threat Vectors & Industrial Control Systems (ICS): Modern Cybersecurity Practices, Part 2
Listen to an interview with Modern Cybersecurity Practices author Pascal Ackerman about common threat vectors and industrial control systems security.
Read MoreHow to Mitigate Against the SMBleed Vulnerability & POC Exploit
Everything you need to know about the new Windows SMBleed vulnerability, proof of concepts, mitigations, and resources to patch and protect against it.
Read MoreTop Security Threats: Detecting Ransomware Tactics
Ransomware is targeting SMBs, using new tactics to evade detection. Here's how to effectively detect on risky activity and protect against infection.
Read MoreDetecting RDP Attacks With Honeypots: Blumira Data Insights
See our proprietary honeypot data on recent remote access attack trends against RDP, and get advice on how to protect your organization against remote attacks.
Read MoreHow To Detect Data Exfiltration
To prevent data exfiltration, it's important to know the signs. Here's what to look out for to detect data exfiltration.
Read More